All Use Cases Posts

AI
Life in the SOC Sucks. Here’s How HyperSOC Can Save Us
Read More
AI
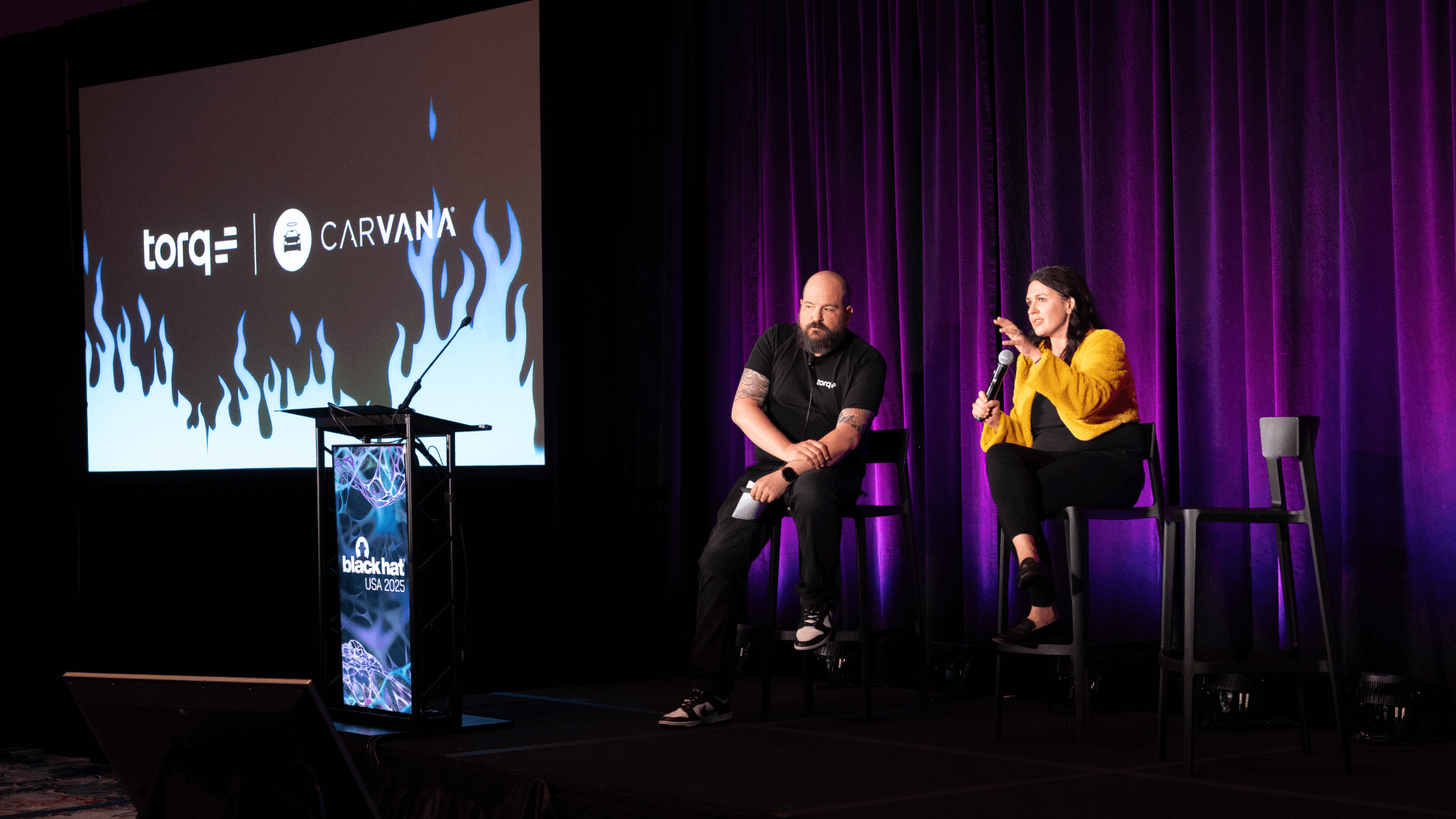
Hyper-AUTO-Mation: Why Carvana’s CISO Bet on Agentic AI for 5x SOC Efficiency
Read More

Security Automation 101
What is a Whaling Phishing Attack? How to Prevent One with Automation
Read More
Hyperautomation
MTTD vs. MTTR: Definition, Differences, & Why They Matter
Read More

AI
Take Control with Torq’s AI Data Transformation
Read More

Integrations
How to Streamline Security with Notion, Torq, and Slack
Read More
AI
Chatbot Automation for Security Teams: Streamline Response and Collaboration
Read More

AI
How Torq and Wiz Power End-to-End Cloud Threat Detection and Response
Read More
Hyperautomation
SIEM vs SOAR vs Hyperautomation: What Actually Works for the Modern SOC
Read More

AI
Squish the Phish: 6 Automated Phishing Response Strategies
Read More

