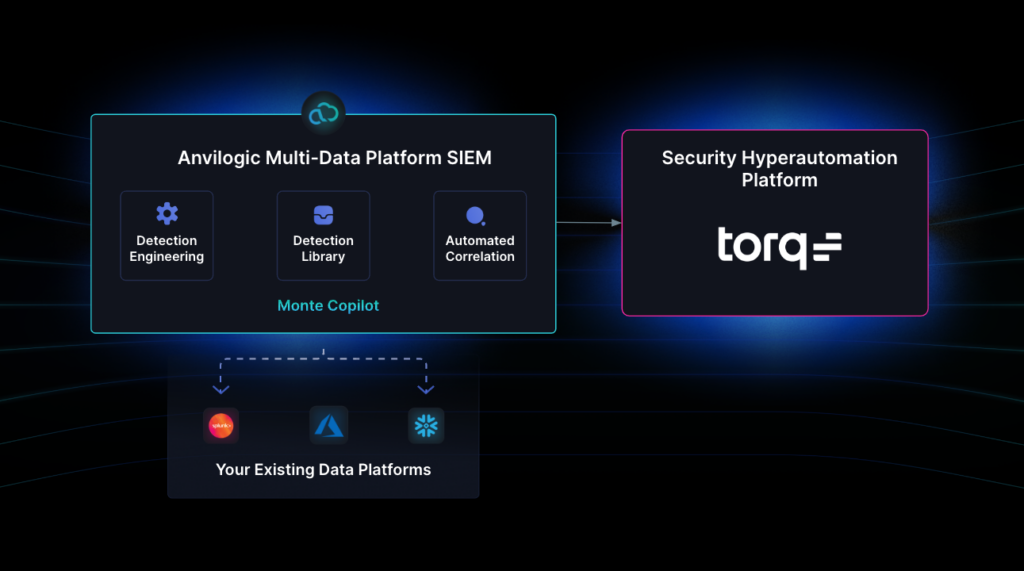
Is SIEM lock-in preventing the transformational impact of Torq Hyperautomation? Due to cost and scale challenges, endpoint activity, cloud telemetry, and network flows are often missing from detection and security automation. For security teams that keep these and other large datasets outside their SIEM, Anvilogic has teamed up with Torq to take SOC automation to the next level.
Integrating Torq and Anvilogic gives security operations teams a new way to detect threats across data platforms like Splunk, Snowflake, and Azure Sentinel- and then quickly handle those detections with interactive remediation workflows. Sound complicated? Let’s walk through an example of how Torq and Anvilogic make it easy.
Detection Scenarios Across Your SIEM and Data Lake
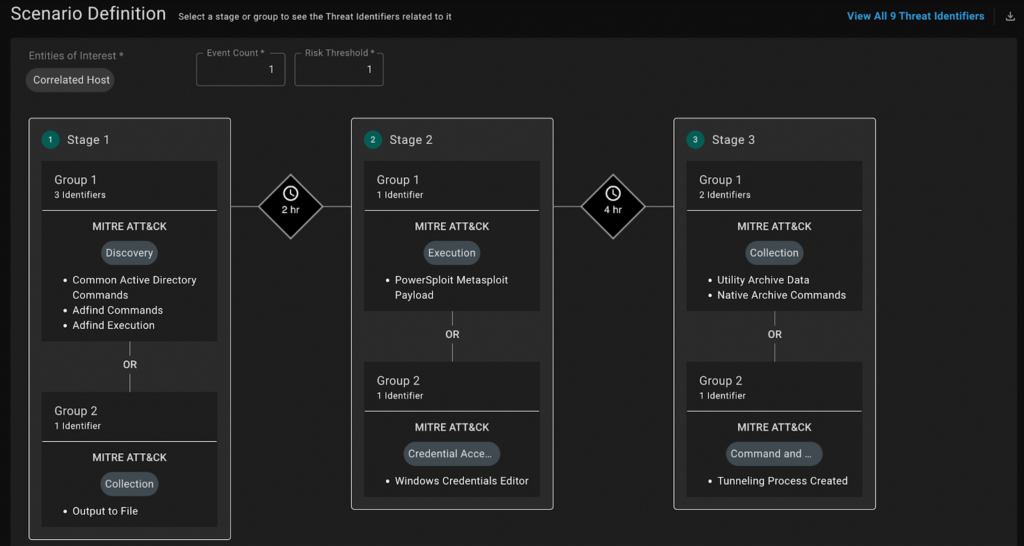
Traditionally, critical data sets such as Active Directory and endpoint activity logs are a SIEM blind spot. Anvilogic’s support for cost-effective data lake alternatives means these high-volume security feeds can be used for detection rules and correlated scenarios.
For example, the FIN6 cybercrime group targets the retail and hospitality sectors to steal payment card data using Active Directory (AD) attack techniques. While these may often seem benign, one of Anvilogic’s thousands of curated detection scenarios correlates FIN6-associated AD activity and what the threat group later does on victim endpoint hosts. The combination of these data points, which are often not available in a traditional SIEM, serves as a high-confidence indication that an attack is in progress.
Slashing the Mean Time to Respond
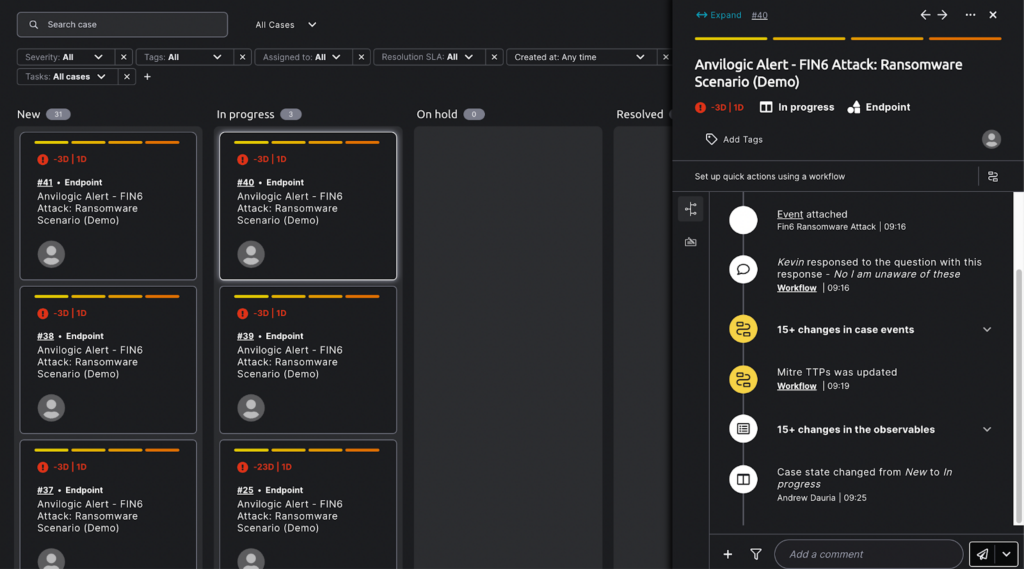
With the new integration between Anvilogic and Torq, the alert for possible FIN6 activity can quickly turn into mitigation, reducing the risk of payment card data theft. The Torq Hyperautomation platform receives a detailed alert from Anvilogic, with information about the users involved and potential indicators of compromise (IOCs). In parallel, the affected user receives a Slack message to determine if they’re aware of the suspicious activity, while the IOCs are extracted for investigation. All of this happens without analyst involvement.
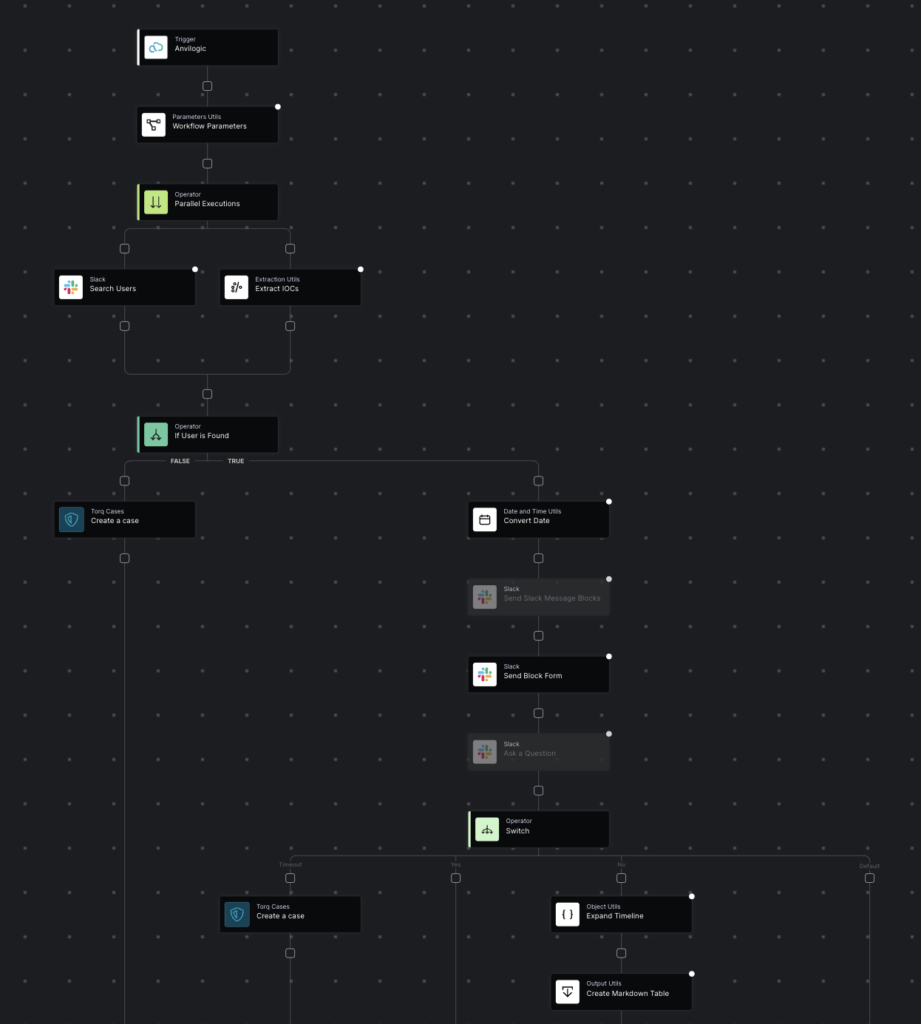
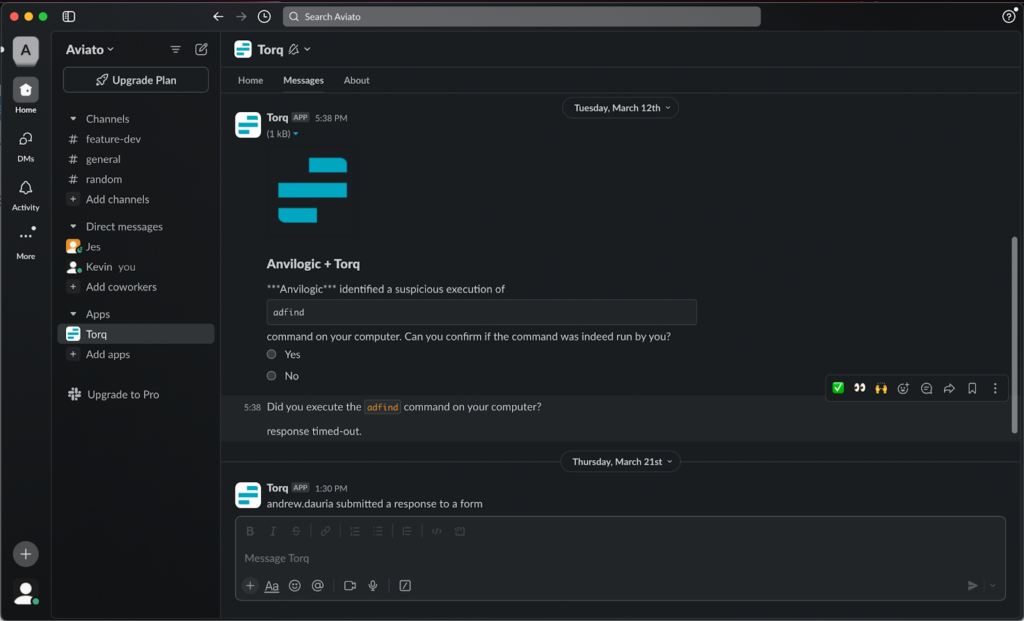
If the user is not aware of the activity, their response, as well as the extracted IOCs, are funneled into the case management system, where the SOC can see why Anvilogic triggered the alert together with the context that’s been automatically gathered. The team can then isolate the system and take any additional steps needed to eliminate the threat from the environment.
Fewer Silos, Better Fidelity: Keys to Effective Automation
We’ve shown how a security operations team can keep an initial network compromise from becoming a full-blown breach. To do this, the team needed to correlate high-volume datasets often unavailable to detection engineers. Anvilogic breaks SIEM lock-in so the SOC can put these large-scale security sources to work. In addition to supporting multiple data platforms, Anvilogic provides thousands of multi-stage detection scenarios off the shelf. This cuts the alert noise that can keep security teams from adopting hyperautomation across more of their processes.
For Torq customers, fewer data silos and better alert fidelity translate to more value from their existing investments. Doing more with less is a common demand in the current climate. We’ve only shown one example of the many opportunities to tackle threats like ransomware, cryptomining, and data theft across clouds, networks, and endpoints. Reach out to learn more about the exciting combination of multi-data platform SIEM and hyperautomation.