It’s difficult for even the most advanced security teams to stay on top of evolving incursions and ensure their processes effectively map to prevent them. That’s where pre-built templates come into the conversation. No-code, security automation templates can handle the considerable burden of having to maintain and update processes that integrate with a company’s security stack.
Having the right systems, tools, and people in place are essential for effective cybersecurity postures. But while templates may sound unsexy, they’re the critical connective tissue that helps enable all three to significantly mitigate the hundreds of thousands of daily cyberthreats the typical enterprise encounters. They also ensure modern compliance requirements are proactively and accurately addressed.
Comprehensive Templates for Comprehensive Security
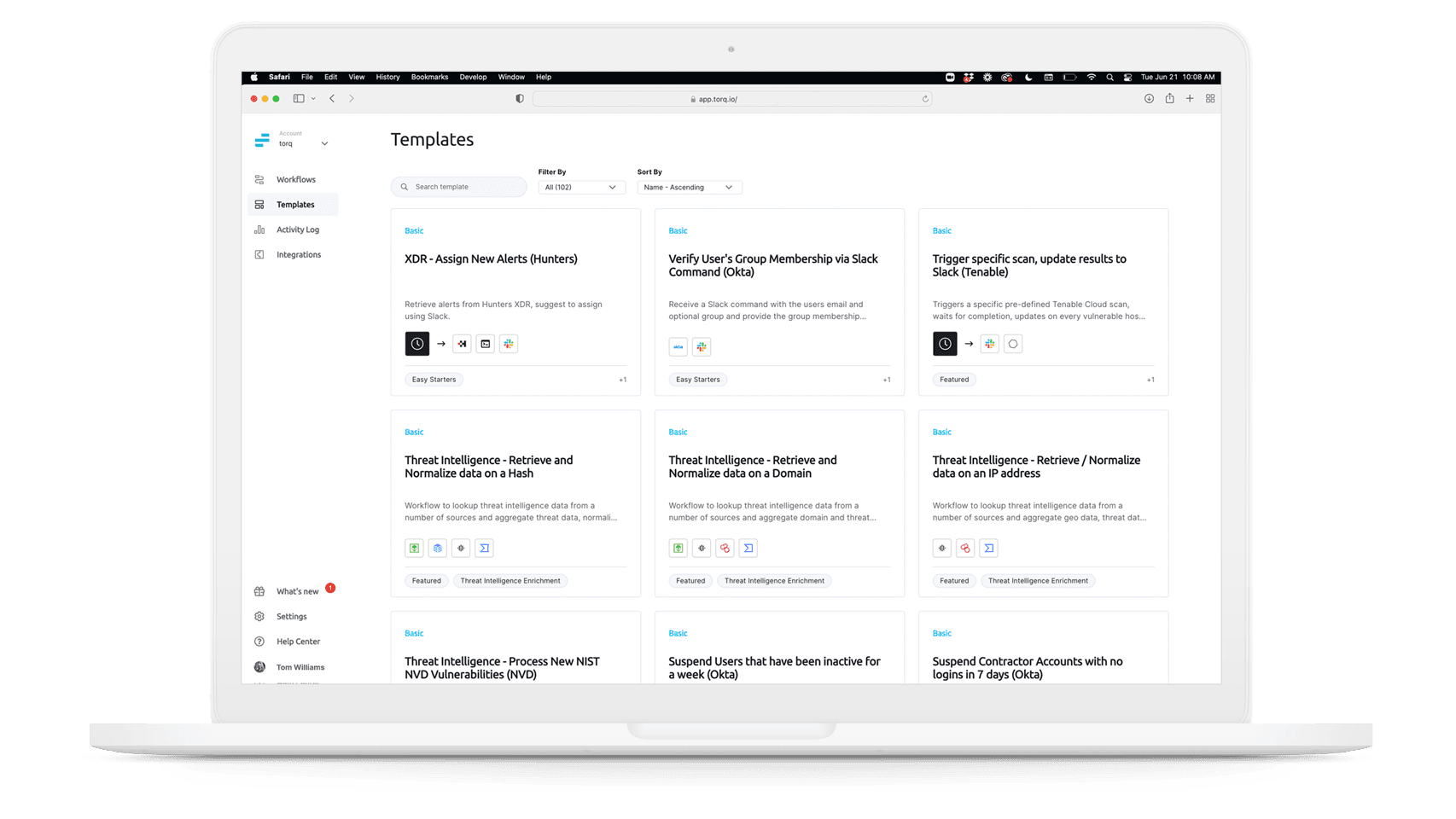
Torq now offers hundreds of security workflow automation templates aligned to MITRE, NIST, and Defense-in-Depth standards. Security teams of all sizes can easily use these templates to rapidly boost incident response speed. They all deliver impressive time to value and ease of use for security teams of all sizes.
Available at no extra cost to Torq customers, these templates are entirely ready to deploy, with minimal configuration. They’re specifically designed to enable security teams of all levels to instantly deploy workflows across their infrastructure and third-party app ecosystem to identify and block cyberthreats before they have a chance to make a significant impact.
Torq templates can be deployed with a single click across thousands of security integrations and vendors. Torq developed its templates in conjunction with its 100+ ecosystem partners, including Orca, Wiz, Armis, and SentinelOne, to ensure customers can build out and standardize their security processes at cloud scale. They enable large security teams to focus on bigger-picture security management. And they dramatically reduce the workload for smaller teams overwhelmed by parsing endless security alerts, rather than focusing on critical threats.
How Torq Templates Mitigate Critical Security Events
Our expansive template library addresses hundreds of critical security scenarios, including:
- Third-Party Identity Lifecycle Management—Workflows can vet all external network access, ensuring contractors and partners are approved, current, and can only engage with systems and data they are authorized for. Torq templates cross-check identity against IdM and SSO systems such as Okta. If a potential incursion is identified, Torq automatically shuts down the account, and alerts the security team to take further action.
- Contextual Threat Hunting—Integrates with services like SentinelOne endpoint security to harness its alerts, and automatically enrich its findings. Torq’s template infuses reports with additional critical data from threat intelligence services such as VirusTotal, to detect suspicious files, domains, IPs, and URLs, as well as to identify potential malware and other breaches. The enriched data delivers a comprehensive contextual view into the alert for security teams to rapidly understand and mitigate the situation, as well as prevent further related attacks.
- Cloud Security Monitoring and Remediation—Ensures storage classes like AWS S3 are protected with advanced encryption, or are appropriately publicly accessible, according to company policies. If a service such as Wiz or Orca detect that a storage class is improperly classified, Torq automatically collects the relevant data, and sends a critical alert to a security analyst to rapidly remediate the issue.
Get Access to Torq Templates Now
Already a Torq customer? You can find our comprehensive Template Library here, or by clicking ‘templates’ on the left-hand menu in the app, just below your existing workflows.
Get Started with Torq, Today
Not using Torq yet? Explore some of our most popular templates and see how Torq’s no-code automation accelerates security operations to deliver unparalleled protection.