Contents
Get a Personalized Demo
See how Torq harnesses AI in your SOC to detect, prioritize, and respond to threats faster.
In an era where cyber threats are constantly evolving, and security teams are overwhelmed by an ever-expanding flood of alerts, tech sprawl, and an ongoing talent shortage, modernizing the SOC is no longer optional — it’s imperative. AI for security operations offers the speed, intelligence, and resilience that today’s SOCs need to survive.
According to Gartner and IDC, automation and AI for security operations are the keys to unlocking new levels of efficiency, accuracy, and resilience in the fight against cyber threats. Learn how SecOps automation has evolved way (way) past SOAR and how SOC teams are putting agentic AI into action to elevate their teams and achieve machine-speed response times.
From Legacy SOAR to Hyperautomation + AI
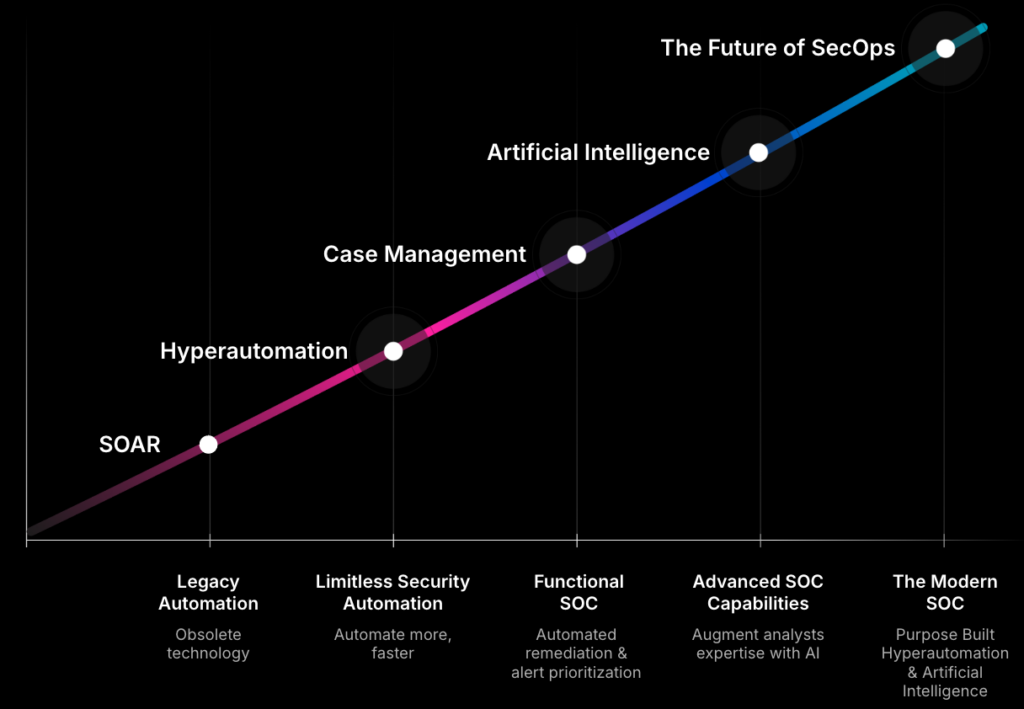
- Legacy SOAR came — and went. The security operations automation journey began with Security Orchestration, Automation, and Response (SOAR) as the primary automation and orchestration option for SecOps teams. However, as the cybersecurity landscape grew more complex and the volume of threats increased, SOAR’s limitations became glaringly evident. Gartner even went as far as to say “SOAR is Obsolete” in their latest ITSM Hype Cycle (2024), placing SOAR at the bottom of their “Trough of Disillusionment”.
- Hyperautomation unleashed limitless potential. Unlike SOAR, Hyperautomation offered unlimited security integrations, simple-to-build automations, and cloud-native scalability. The incorporation of case management into a Hyperautomation engine helped mitigate alert fatigue by enabling automated remediation of false positives and other low-risk threats while more intelligently prioritizing comprehensive security cases in a meaningful way.
- AI for security operations sped up the SOC. The next evolution of security automation involved leveraging generative AI to augment human expertise, enabling SOC teams to achieve machine-speed detection and response.
- Agentic AI takes the wheel: Agentic AI is the next logical evolution of AI for security operations, delivering autonomous decision-making capabilities that can reason, plan, and execute goals without constant human supervision. It’s the brain behind the autonomous SOC, freeing up analysts to do the strategic work. IDC’s report highlights that agentic AI can solve problems, adapt to its environment, and make complex decisions without human intervention. This shift moves SOCs from human-in-the-loop to human-on-the-loop supervision.
The modern SOC has arrived. As Gartner recently highlighted, to overcome the existential challenges that continue to plague SOC teams, security operations must continue to adapt. This brings us to the future of SecOps, where the gold standard for the modern SOC is a purpose-built combination of Hyperautomation and agentic AI to achieve the autonomous SOC.
Benefits of Adopting Automation and AI for Security Operations
AI for security operations is critical not just for efficiency but for survival. It’s about alleviating the pressure on SOC teams, helping to avoid burnout and reducing the four million+ talent shortage gap that exists in the cybersecurity industry today.
Gartner predicts that “by 2028, AI in threat detection and incident response will rise from 5% to 70%, primarily augmenting — not replacing — human analysts.”
As Gartner highlights, while the growth of AI continues to expand, its primary aim should be to augment the existing staff operating the SOC, not replace them entirely. This is good to keep in mind, as many organizations are hesitant to fully entrust AI with their security operations. However, with the rise of AI used in targeted attack campaigns, most organizations do recognize that it is near impossible for humans alone to keep pace with today’s quantity and complexity of threats.
When implementing AI for security operations, the most successful benchmarks to strive for are:
- Eliminating alert fatigue
- Improving SOC analyst morale
- Getting time back to focus on critical threats
- Mitigating threats more quickly and efficiently
- Increasing the accuracy of results
The benefits of automation and AI for security operations are not in removing human decision-making altogether but rather in upskilling the most junior SOC analysts while preventing the most experienced analysts from burning out in their role.
To fully realize the potential of AI for security operations, organizations need a solution that combines context awareness and autonomous action. That solution is Socrates.
Introducing Socrates: Your AI SOC Analyst
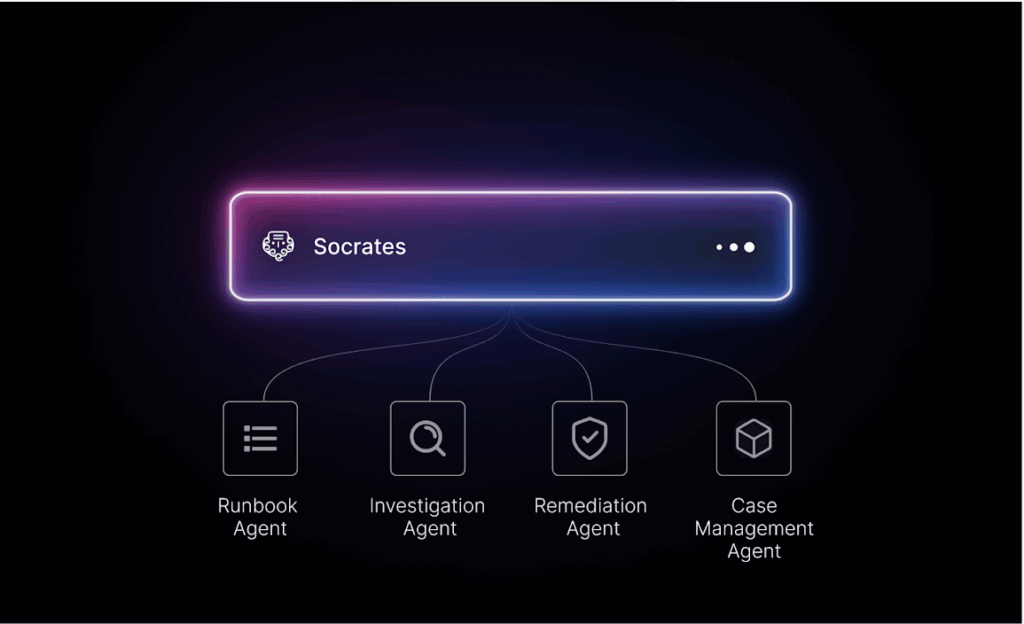
Torq Socrates is our AI SOC Analyst capable of deep research, planning, and autonomous execution of end-to-end security case management. Socrates acts as an OmniAgent, coordinating multiple specialized AI Agents for contextual alert triage, incident investigation, and auto-remediation of Tier-1 tasks.
For critical threats, Socrates augments your team’s expertise — enabling them to take action faster thanks to natural-language, human-AI collaboration.
There are two primary ways SOC teams are using Socrates to handle security cases today:
- Assigning cases to Socrates for end-to-end autonomous remediation
- Faster human-on-the-loop remediation with AI augmentation
1. Autonomous Remediation
First, SOC teams can assign specific cases to Socrates for auto-remediation without requiring any human intervention.
In traditional analyst remediation, when a case is assigned, the analyst typically consults a runbook to guide them through the response required to contain the specific event (or events) that appear within the case.
From start to finish, the triage, investigation, and remediation of a single case can take a human analyst 30 minutes or more, depending on the experience level of the analyst. In larger enterprises, there may even be multiple analysts with varying responsibilities involved in the lifecycle of a case — one for the initial triage, one for the Tier-2 investigation, and another for the incident response.
Socrates follows the same runbook planning and execution process but instead leverages a team of AI agents to craft, plan, and execute highly customized incident response strategies — at machine speed. Socrates’ leverages agentic AI to analyze SOC-defined runbooks written in natural language, learn from past outcomes, identify attack patterns, and continuously refine response plans to adapt to new threat vectors — resulting in complete auto-remediation of 95% of cases in mere minutes.
For cases that increase in severity based on Socrates’ agentic investigation or as new case data is added, raising the threat to a critical level, SOC teams can build off-ramps into each runbook that tell Socrates when to escalate cases to a human analyst for intervention.
2. Faster Human-on-the-Loop Remediation
Which brings us to the second use case: leveraging Socrates to help SOC teams investigate and take action on the cases that do require human decision making — faster.
Analysts who are assigned critical cases for human-guided remediation can take advantage of Torq’s Multi-Agent System (MAS) by using natural language to chat with Socrates and ask for:
- AI-generated case summaries: Faster access to real-time and historical case observables, attachments, associated indicators of compromise (IOCs), or current case status enables streamlined decision-making by eliminating irrelevant noise.
- Deep research investigations: Enrich cases by uncovering hidden attack patterns across diverse data sources and third-party threat intelligence to help precisely assess the threat impact and improve strategic threat prioritization.
- Agentic AI-augmented remediation: Take action across the security stack using AI agents to trigger complex remediation workflows through Torq’s Hyperautomation platform, significantly reducing the amount of time from case assignment to case resolution.
With Socrates, even a brand new analyst who hasn’t been trained on how to leverage the full functionality of every security solution in their stack can easily ask Socrates to deploy AI agents that can quickly quarantine devices, isolate hosts, or kick off a password reset — without the risk of human error.
In its simplest form, Socrates was built to do what Torq has set out to do from the very beginning: Hyperautomate SecOps. By coordinating a team of AI agents, Socrates can automate the most repetitive tasks and reduce Tier-1 triage and investigation by 90% — helping humans respond to threats faster.
Embracing Hyperautomation and AI for Security Operations
In an era where cyber threats are constantly evolving, the modernization of the SOC is no longer optional — it’s imperative. The inclusion of AI for security operations — like Torq Socrates — marks a pivotal shift in how SOC teams can combat alert fatigue, tech sprawl, and talent shortage.
By integrating Hyperautomation and AI, Torq HyperSOC exemplifies how AI for security operations drives faster detection, smarter decisions, and machine-speed remediation, achieving:
- Up to 90% reduction in investigation times
- 3-5x increase in SOC alert capacity without additional headcount
- Autonomous remediation of over 95% of security threats
AI for security operations lets teams regain significant amounts of time, allowing human analysts to focus on more strategic tasks while maintaining control over critical operations. The future of the SOC lies in this harmonious blend of human expertise and intelligent automation, setting a new standard for operational efficiency in security operations.
Want to learn more about the SOC’s evolution from automation to autonomy? IDC’s Spotlight Report explores why agentic AI for security operations is the next leap in the autonomous SOC.
FAQs
AI in security operations enables SOC teams to detect, investigate, and respond to threats at machine speed — faster than any human analyst can work alone. Modern AI SOC platforms like Torq use agentic AI to autonomously triage alerts, enrich cases with threat intelligence, and execute remediation workflows end-to-end. The goal isn’t to replace analysts but to eliminate the repetitive Tier-1 work that causes burnout, freeing teams to focus on the threats that actually require human judgment.
Traditional SOAR automation follows rigid, pre-scripted playbooks — if X happens, do Y. It breaks when conditions change and requires constant maintenance to keep integrations working. Torq Hyperautomation™ replaces that model with cloud-native, no-code workflows that integrate with unlimited security tools, scale automatically, and adapt without a dedicated engineering team to maintain them. Gartner placed SOAR at the bottom of its Trough of Disillusionment in 2024 for precisely these limitations.
The most measurable benefits are a 90% reduction in Tier-1 investigation time, autonomous remediation of over 95% of security threats, and a 3–5x increase in alert capacity without adding headcount. Beyond the metrics, the operational benefits matter just as much: reduced analyst burnout, less alert fatigue, and the ability for junior analysts to take meaningful action without deep tool expertise — using natural language to direct AI agents across the security stack.
Yes — and it’s one of the most compelling reasons to deploy AI SOC automation now. The cybersecurity industry faces a shortage of over four million professionals globally. AI doesn’t solve the hiring problem, but it fundamentally changes the math. A four-person team running Torq can cover 24/7 operations without burning out, because AI handles the high-volume, repetitive work that would otherwise require a much larger staff. Gartner predicts AI in threat detection and incident response will rise from 5% to 70% by 2028, primarily by augmenting existing analysts rather than replacing them.
The three challenges that surface most consistently are tool fragmentation, trust in AI decisions, and governance readiness. Most SOCs run 7 or more AI-powered tools that don’t share context — meaning analysts still manually stitch together a complete picture of each incident. Trust is the next barrier: teams are confident AI can help but won’t let it act autonomously without transparency into how it reaches its conclusions. And governance — defining what AI can do, what requires human approval, and how decisions are audited — is the piece most organizations address too late. The platforms that resolve all three simultaneously are the ones delivering the outcomes security leaders are actually looking for.