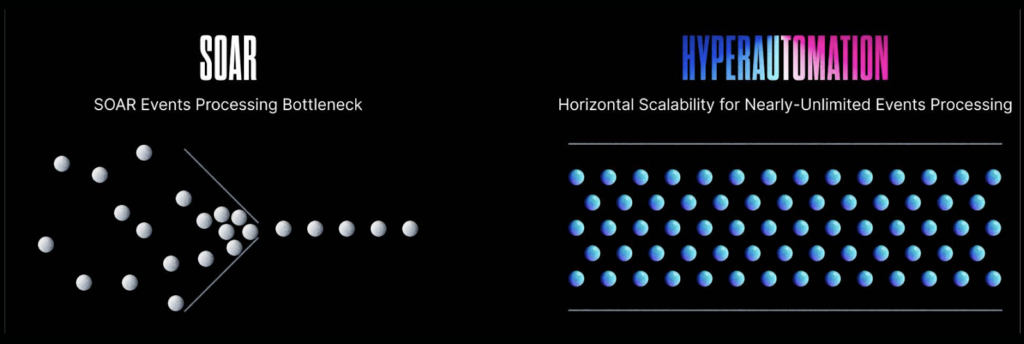
Legacy SOAR offers limited events processing. That’s just the way it was built. SOAR is a standard monolithic architecture in which the entire application is deployed as a single entity, which typically runs on a single server or cluster of services. This dramatically restricts SOAR’s processing capacity, and it’s time-consuming and costly to try and extend SOAR beyond these restrictive configurations – it typically would require an entire rebuild and redeploy to upscale.
The only ways to deal with that is by either underprovisioning or overprovisioning your legacy SOAR. But that also creates problems. Underprovisioning creates poor performance, slow response times, and reduced availability. This affects the user experience and your solution’s ability to identify and remediate threats effectively. Overprovisioning allocates more resources than are actually needed to ensure there is always enough capacity to meet demand, but that method boosts costs, reduces efficiency, and increases risk with an extended infrastructure footprint.
Where legacy SOAR falls short, however, security hyperautomation shines.
Here are the five major benefits of using hyperautomation to process your security events to overcome the limits of legacy SOAR.
- Hyperautomation provides limitless horizontal scalability that allows individual components and services to be independently scaled based on specific demands.
- Hyperautomation allows you to sift through the noise, prioritize events, close false positives, and more – all at scale and with precision accuracy. Plus, it’s entirely automated.
- Hyperautomatn ensures specific event types are directed to relevant owners and automatically enriched with decision-supporting data.
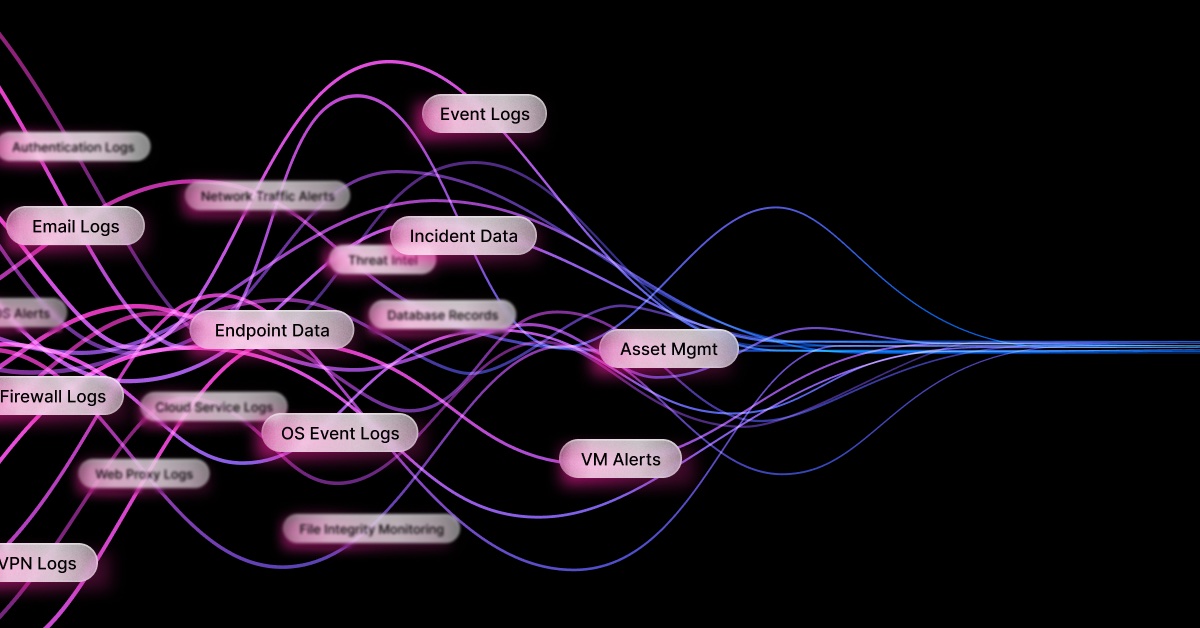
- Hyperautomation empowers you to automate the orchestration and handling of diverse technical solutions that best suit your requirements, including CNAPP, CSPM, CWPP, EDR, XDR, EASM, IAM, SAST, and DAST.
- Hyperautomation enables you to have SLAs for different events to ensure the flood of events from one type or source does not prevent the system from processing other events.
Through dynamic defenses, security hyperautomation allows you to unblock the events processing bottleneck. Read more about how hyperautomation outperforms SOAR in our “SOAR is Dead” manifesto.