Contents
Get a Personalized Demo
See how Torq harnesses AI in your SOC to detect, prioritize, and respond to threats faster.
Still obsessing over compliance certifications and data volumes when choosing your AI SOC analyst? You might as well be that guy at the dealership kicking tires and demanding V8 specs while ignoring the self-driving capabilities.
Today’s CISO battlefield isn’t won with yesterday’s metrics. While AI security vendors sell you on training corpus size and customization options, you should be demanding zero-day detection without signatures and unified threat visibility.
Let’s be brutally honest: the blistering pace of AI innovation means your current AI SOC evaluation checklist is obsolete. GenAI marked an inflection point; now, agentic AI is completely disrupting SecOps. This means the real competitive edge lies in capabilities your procurement team isn’t even asking about.
So, what should CISOs look for in an AI SOC analyst? Below, we break down 8 key capabilities that you might not have considered but are crucial to ensure AI trust and effectiveness in your SOC.
What to Look for in an AI SOC Analyst Evaluation
1. AI That Simplifies and Communicates Context
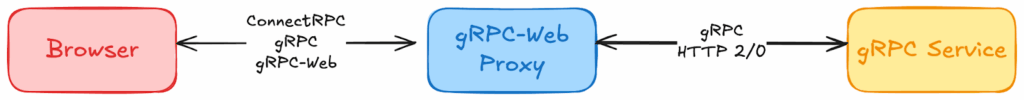
Look for: Next-gen AI for the SOC that shows sophistication beyond query-response models, demonstrating a nuanced understanding and delightful communication of organizational context, ongoing security incidents, and specific scenarios.
Rather than summarizing in a generic “TL;DR” format, the AI should communicate about logs, case artifacts, and indicators of compromise (IOCs) through a cybersecurity-oriented UI that highlights key information for the specific security context.
Ask:
- Can the AI maintain contextual continuity across analyst shifts and SOC handoffs?
- How does the chat UI maintain context for the user when referencing information-heavy items like logs and cases?
- Does the AI have different user views for summarizing actions, IOCs, and alerts?
- Where can I embed our knowledge and policies to guide the AI’s interactions?
General example:
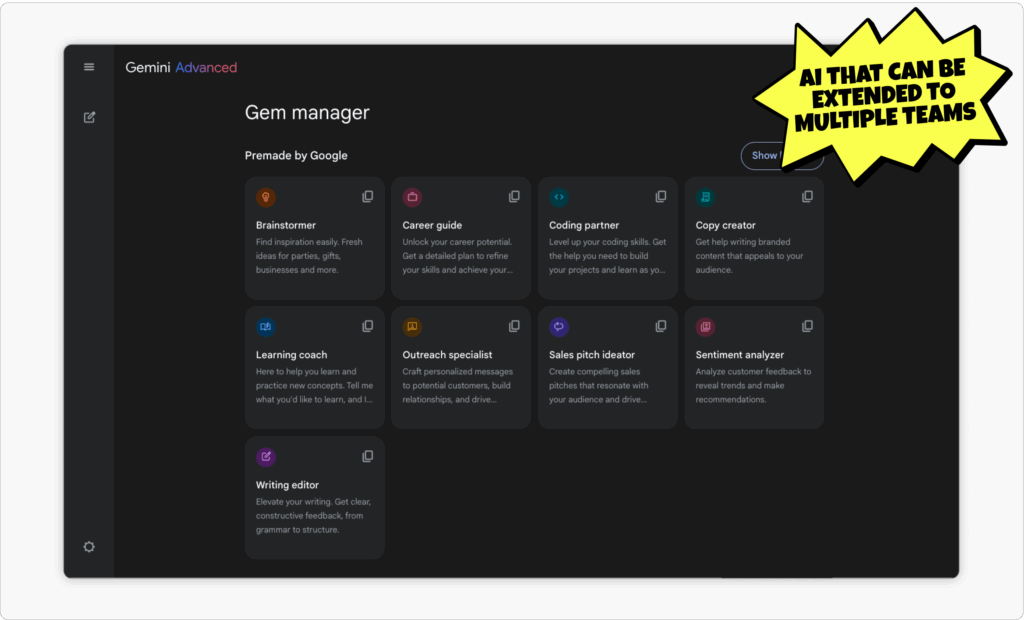
2. AI for the Entire Team
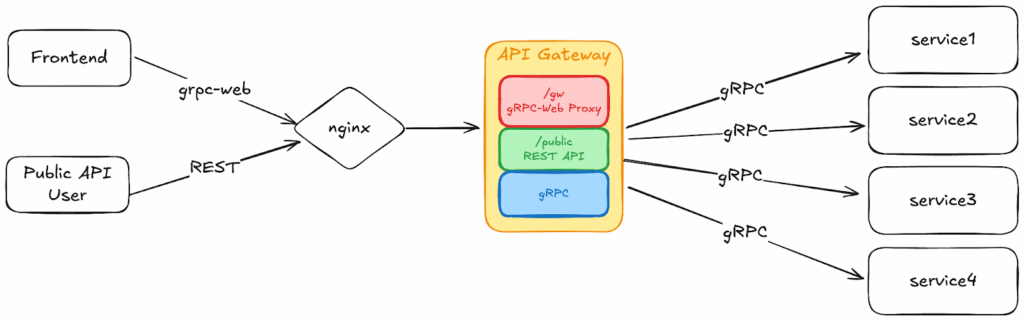
Look for: Practical AI capabilities mapped explicitly to real-world SOC workflows and use cases.
The AI SOC analyst should do the actual, gritty tasks your SOC team performs daily — from initial triage to investigating alerts, hunting for threats, and remediating problems. This isn’t about general intelligence; it’s about directly supporting actual analyst workflows from end to end. If you use a multi-agent system (MAS), the AI SOC analyst should act as an OmniAgent to coordinate and collaborate with multiple specialized AI agents to accomplish these complex security goals.
Ask:
- What analyst-level jobs does the AI accelerate (e.g. query writing, unstructured enrichment, and response recommendations)?
- How does the AI SOC agent accelerate threat hunting and detection engineering through intelligent hypothesis generation?
- Is the system capable of auto-healing errors in security workflows the way a good security engineer can?
General example:
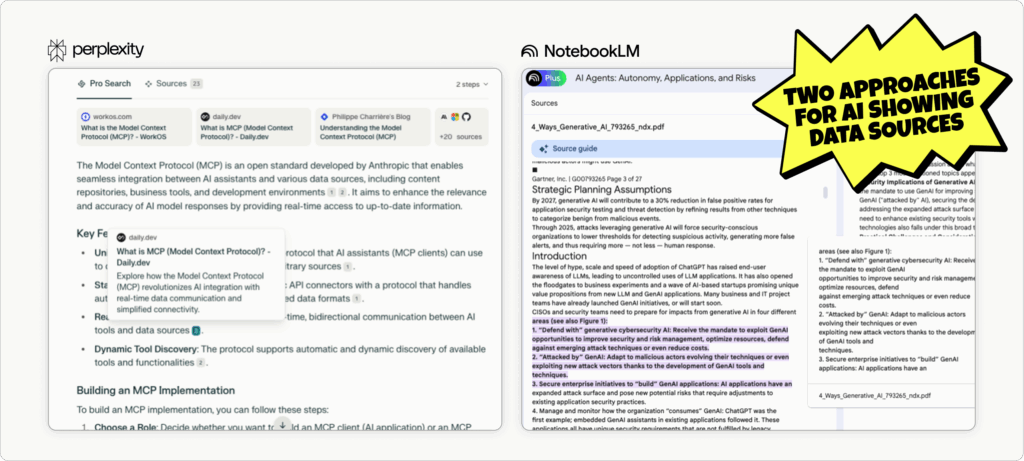
3. AI That Explains What It’s Doing
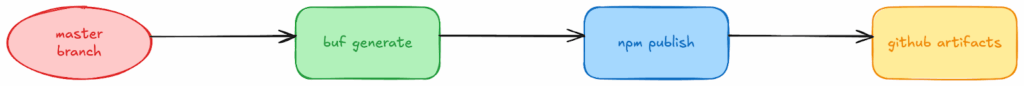
Look for: AI that grounds its findings and recommendations in clear, structured explanations showing its sources.
CISOs increasingly prioritize “explainability” in AI decisions as a pragmatic imperative for achieving cognitive alignment between the AI SOC analyst and the human security team. To foster trust, adoption, and effective action, your security team must have a line of sight into the AI’s reasoning, not just its conclusions.
Ask:
- Does the AI SOC analyst clearly explain why particular security events are flagged or escalated?
- How easily can human analysts validate or challenge the AI’s recommendations? For instance, can they request source links, exact quotes, or highlighting?
- Do we have visibility into the AI agent’s self-critique step?
- What validation guardrails does the AI implement?
General examples:
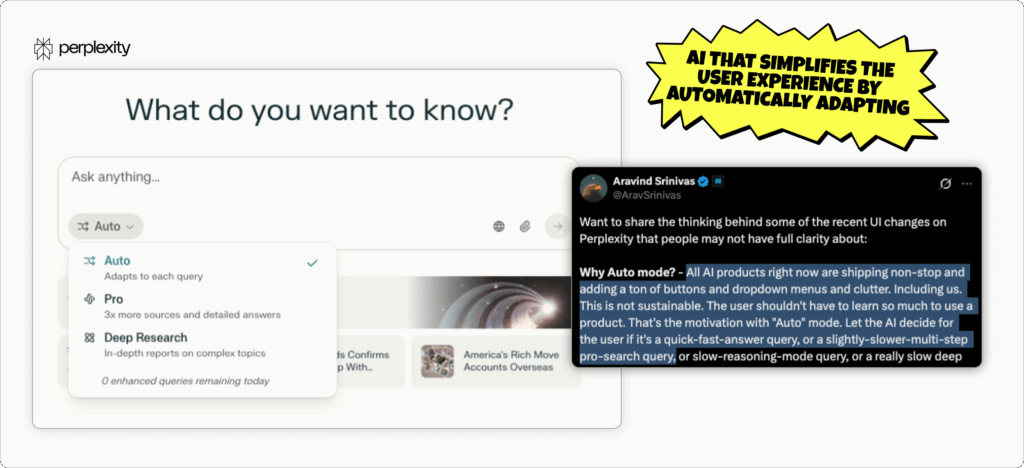
4. AI That’s Easy to Interact With — Without Training
Look for: A SOC-specific user interface that is genuinely intuitive, innovative, and frictionless and that directly enhances analyst productivity, retention, and job satisfaction.
Even the most powerful AI can be hampered by a clunky or difficult interface, undermining your team’s effectiveness and morale and discouraging AI adoption. A truly innovative interface should feel natural to use and streamline workflows, not add complexity or friction to processes. An intuitive design enables analysts of any level to quickly access insights and take action without specialized skills or knowledge.
Ask:
- How much do our human analysts need to be familiar with AI hacks and general prompt engineering, such as knowing when to use deep search options, ask for a specific data format, or open a new conversation thread?
- Does the AI SOC analyst support conversational SIEM queries and natural-language threat exploration?
- How does the AI communicate its planning and thinking process?
- In autopiloting, can I interrupt the investigation before the AI is done?
General example:
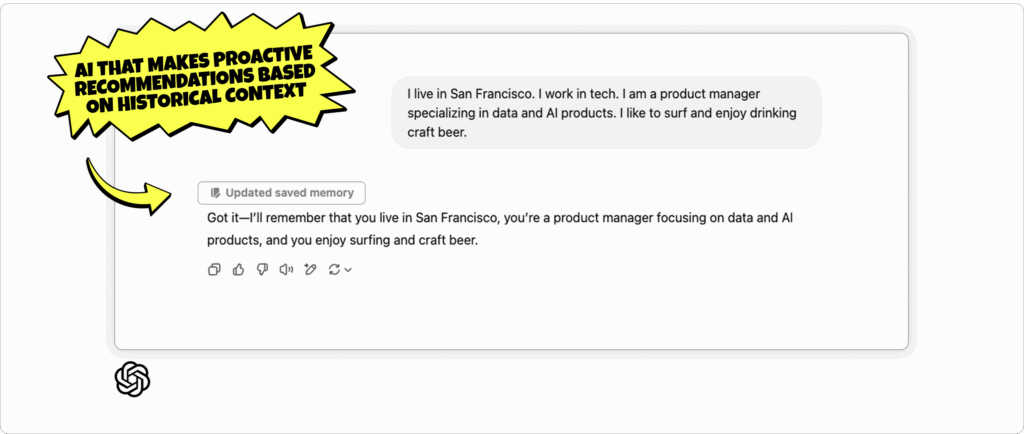
5. AI That Helps You Get Ahead
Look for: An AI SOC analyst that doesn’t only react to known threats but proactively guides SOC teams towards improving security posture and operational effectiveness.
Think of your top analysts — the ones who are always one step ahead, anticipating your team’s needs and suggesting improvements without being asked. Agentic AI that performs at this advanced level can act as a virtual extension of your team, identifying weaknesses and suggesting optimizations to elevate your security operations.
Ask:
- Can the AI SOC analyst proactively detect and suggest SOC operational improvements, such as recommending repetitive manual processes that are ripe for automation?
- Can it automatically correlate cases with incident history and recommend improvements?
- Has your AI ever caught a missing step in its instructions and fixed it (or asked about it) before executing?
- Can the AI automatically tag and store important information from your interactions that can help in future cases?
- Will the AI suggest changes to the detection rules, workflows, or playbooks? How often does your AI flag inefficiencies in workflows?
General example:
6. AI That Understands What You Really Want (and Can Figure Out How to Do It)
Look for: Deterministic, agentic AI that understands how to break a user intent into multiple tasks, which may require different execution plans.
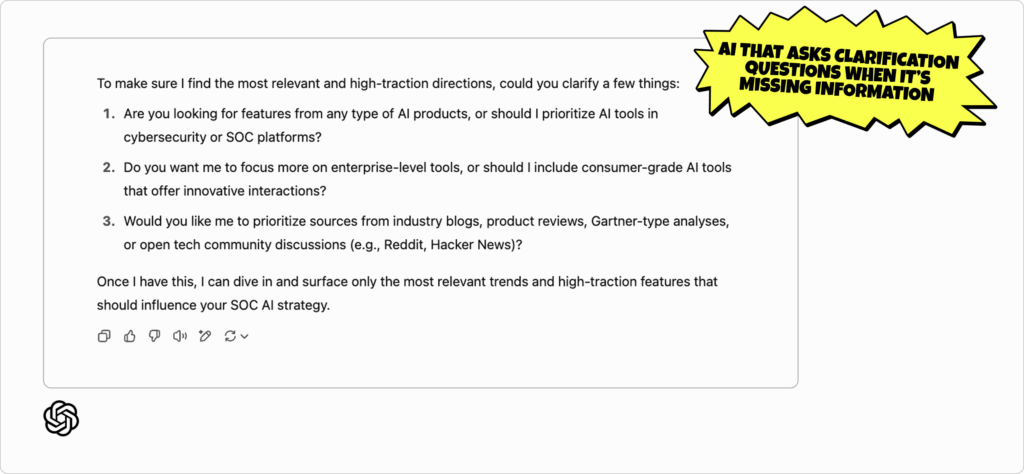
Good AI gets a task and starts working. Great AI first looks for communication gaps, understands the goal, and asks for more instructions when needed. Ideally, the user shouldn’t have to think like the AI to ensure the AI grasps their intent — the AI should understand how the user thinks and ask clarifying questions when needed.
A structured execution scheme reduces ambiguity and improves the accuracy of the AI’s planning and orchestration, eliminating the likelihood of the AI agent skipping steps, going out of order, selecting incorrect tools, or misinterpreting instructions.
Ask:
- When I give the AI a vague or complex instruction, does it ask clarifying questions — or just charge ahead?
- How does it use screens, user information, and past sessions to better understand the user’s specific intent?
- Can your AI break down a high-level goal (‘Investigate this alert’) into a sequence of logically ordered tasks — and tell you why?
- Can your AI explain its execution plan in plain language before it starts and adjust if you push back?
General example:
7. An AI Assistant That You Don’t Need to Babysit
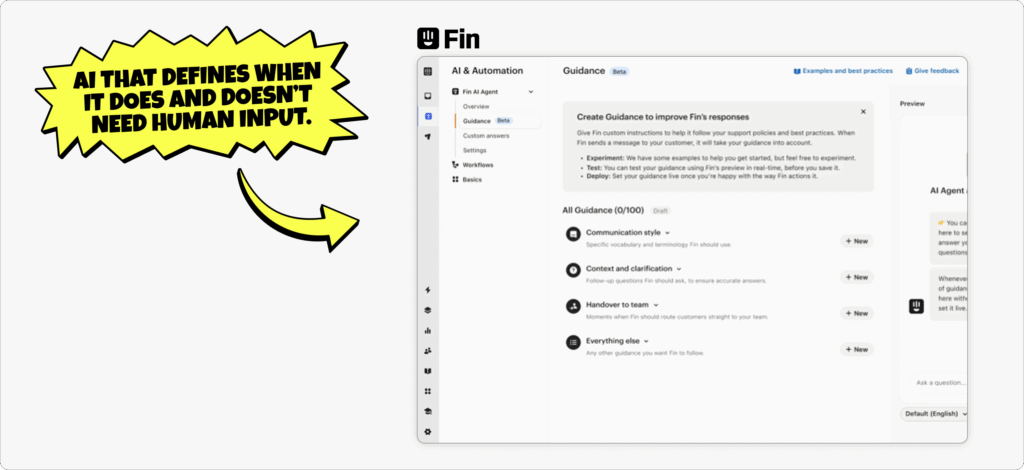
Look for: Agentic AI capable of autonomously chaining together multiple actions without constant human prompts.
Your human analysts don’t want to click through 10 steps every time they need the AI to take action. While human oversight of critical decisions is important, to efficiently investigate an alert end-to-end and even initiate containment, an AI SOC analyst must be capable of independently stringing together a sequence of relevant subtasks — like log collection, enrichment, reverse engineering, and containment suggestions — in pursuit of a high-level goal.
Ask:
- Can the AI SOC analyst complete a multi-step investigation with one high-level instruction?
- Can the AI write and execute deterministic workflows when needed?
- Does it pause and check with human analysts before executing sensitive tasks (e.g., blocking users or IPs)?
- When given a high-level goal or non-playbook scenario, does the AI independently decide which steps to take and in what order?
- How does the AI identify when not to act — and escalate to a human when it hits a confidence or authority threshold?
General example:
8. AI That Gets More Helpful Through Human Feedback
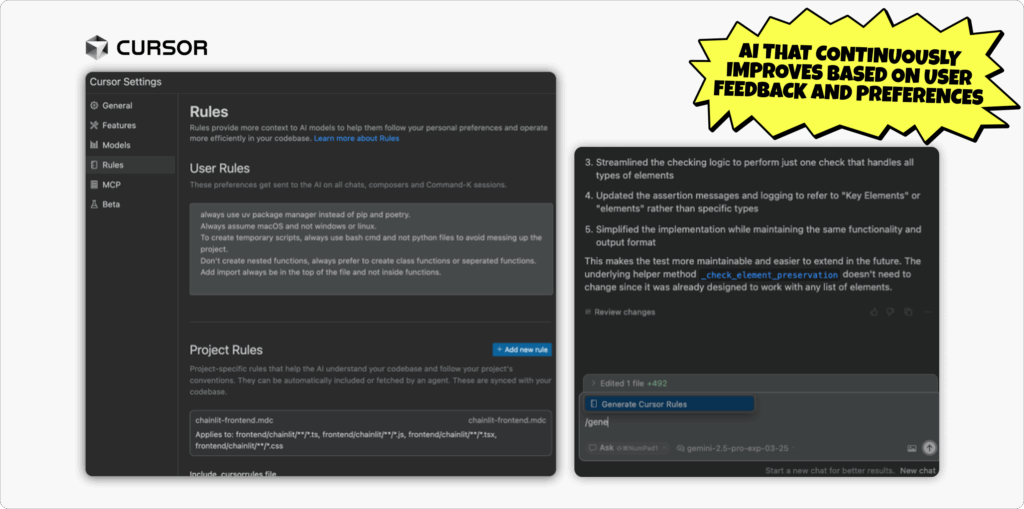
Look for: An AI SOC analyst that continuously learns and improves by observing and incorporating feedback from human analyst behavior.
The best AI SOC analysts learn from human analyst behavior to become more effective and accurate over time. Think of it as shaping the ideal analyst that shadows your team, watches how they triage alerts, write queries, and handle false positives — and gets smarter with every interaction.
Human analysts should be able to fine-tune and correct AI as threats evolve rather than treating it as a black box. In practice, features like thumbs-up/down ratings, interactive retraining, or the ability to override AI decisions make the human–AI loop tighter and more effective.
Ask:
- How does the AI SOC analyst adapt based on human analysts’ corrections or preferences over time?
- Can I adjust the AI’s prioritization or response style via feedback?
- How can the user flag a successful conversation with the AI to make future sessions easier and more effective?
- Can you review and audit what the AI has learned from your team?
General example:
Next-Gen AI for the SOC is Here — Are You Ready?
Don’t be the security leader who marvels at a shiny paint job while ignoring the revolutionary engine. When evaluating AI SOC analysts, focus on explainable intelligence, seamless integration into your team’s workflow, and deterministic AI that can independently plan and orchestrate all of the actions required to complete a high-level goal from end to end.
Finding an AI SOC analyst that truly understands context, empowers your analysts, and acts with proactive autonomy will ensure you’re not just keeping up with the latest tech but investing in a force multiplier for your security team.
Get the AI or Die Manifesto to learn strategic considerations, get insights from a CISO, and learn red flags and more questions to ask for an AI SOC evaluation.