Contents
Get a Personalized Demo
See how Torq harnesses AI in your SOC to detect, prioritize, and respond to threats faster.
TL;DR
- SOAR was security automation’s first draft. But static playbooks, custom scripting, and 12–18 month implementations couldn’t keep pace with a threat landscape that moves at machine speed.
- The numbers tell the story. Most SOAR deployments cover 30–40% of alerts. 40% of alerts are never investigated. And the engineering hours required to keep playbooks running keep climbing every quarter.
- AI SOC changes everything. Agentic AI investigates every alert — including scenarios for which no playbook exists. It reasons through problems, adapts to context, and executes a response within guardrails.
- Migration isn’t starting over. Your existing workflows run on Torq’s Hyperautomation layer at 10x the speed. The AI SOC layer adds what SOAR never could: autonomous investigation, adaptive triage, full case management, and real remediation actions. RSM migrated 200+ customers in three weeks. Valvoline was live in 48 hours.
If you’ve been in security operations for more than a few years, you’ve lived through the automation hype cycle at least twice. First, it was SIEM that was going to solve everything. Then SOAR was supposed to fix what SIEM couldn’t. Now, AI SOC platforms are delivering what SOAR always promised but never actually could.
Each wave solved real problems. But SOAR’s issues have become bigger than its solutions. Static playbooks that break when APIs change. Custom scripting that only two people on the team understand. Implementations that take 12–18 months before showing ROI. A coverage ceiling that tops out at 30–40% of your alert volume, no matter how many engineering hours you throw at it.
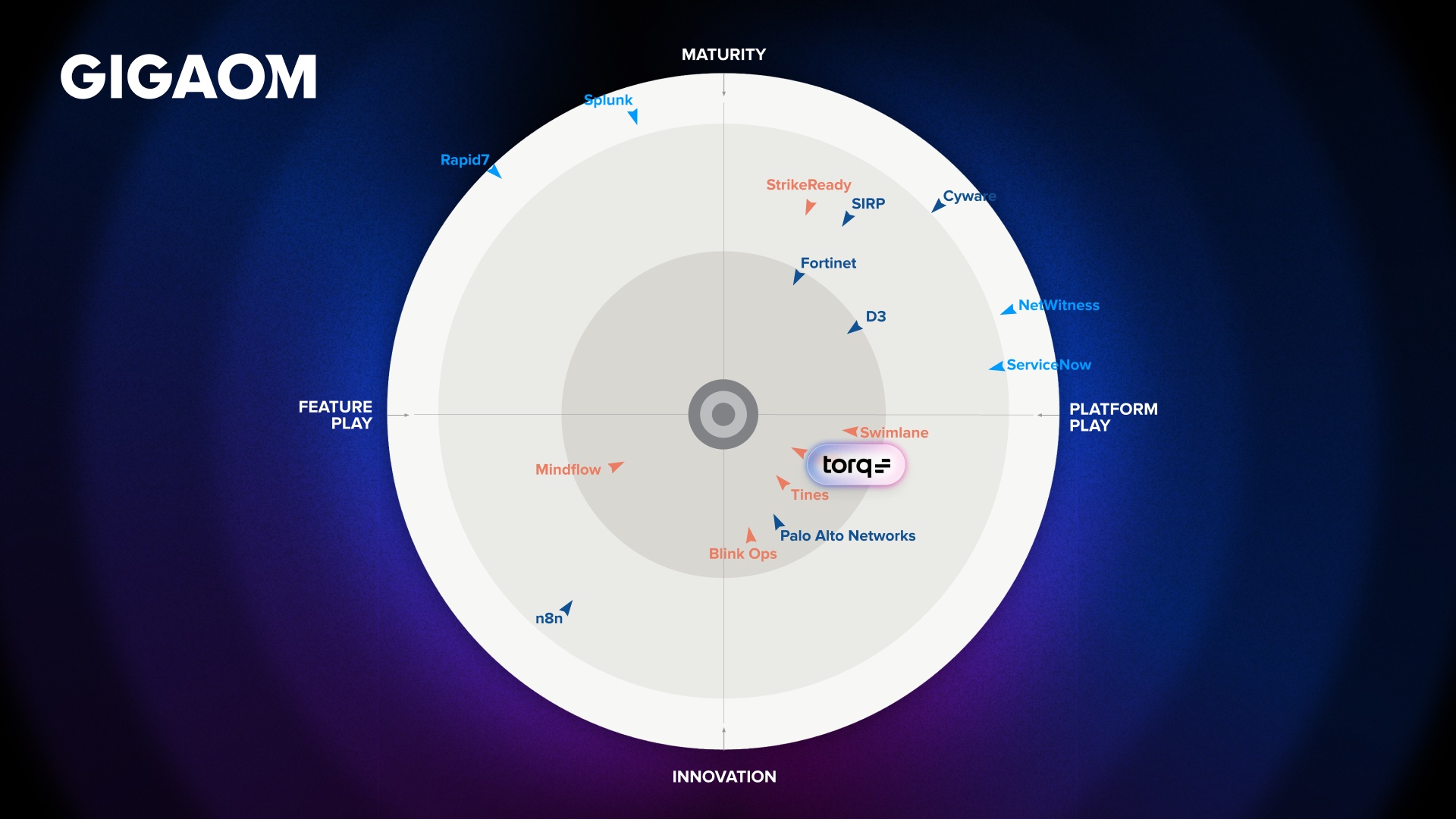
GigaOm recognized this shift when it renamed its SOAR Radar to the SecOps Automation Radar in 2025 — because the category itself has evolved past SOAR. Torq has been named a leader and outperformer in that report for three consecutive years, specifically for Hyperautomation capabilities that legacy SOAR can’t touch.
This piece breaks down what SOAR and AI SOC actually are, where SOAR falls short, and why AI-native Hyperautomation is the clear path forward.
What is SOAR?
SOAR (Security Orchestration, Automation, and Response) emerged around 2015 to solve a specific problem: SOC analysts were drowning in manual, repetitive tasks across disconnected tools. SOAR platforms promised to connect those tools and automate the workflows between them.
At its core, SOAR does three things. It orchestrates actions across your security stack (e.g., fire an API call to your EDR, update a ServiceNow ticket, send an email notification). It automates predefined response playbooks (e.g., if a phishing alert, extract IOCs, check reputation, quarantine the email). And it collects and organizes investigation data.
That model worked when the threat landscape moved slowly enough for playbooks to keep up. It doesn’t anymore.
Every playbook has to be built, tested, and maintained by someone — usually a security engineer with scripting skills your team can’t afford to lose. When vendor APIs change, playbooks break. When a new threat type emerges that doesn’t match an existing workflow, the alert sits in the queue until a human gets to it. SOAR platforms are code-heavy, rigid, and expensive to scale, so most organizations end up automating only a fraction of their workflows and manually handling the rest.
As highlighted in GigaOm’s SecOps Automation Radar, legacy SOAR’s inherent complexity, management overhead, and high costs have made it increasingly unsustainable. The SANS 2024 SOC Survey found that automation itself had become the top barrier to effective SOC operations — ranked higher than staffing — reflecting just how badly the SOAR generation of tools has failed to deliver on its promise.
What is an AI SOC?
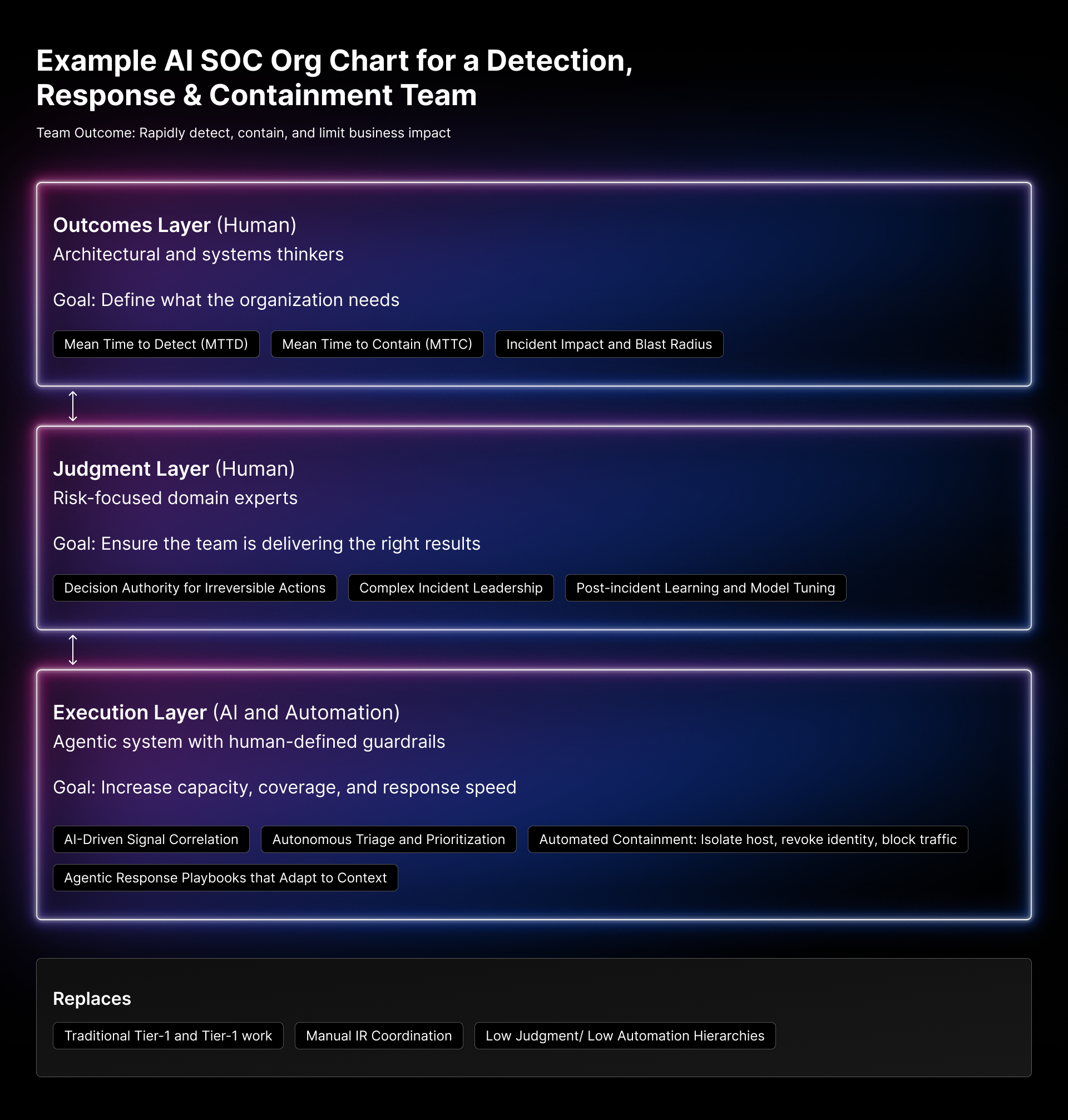
A true AI SOC model isn’t just bolted-on “AI in the SOC.” It’s an operating model — a fundamentally different way of structuring how your SOC detects, investigates, and responds to threats.
An AI SOC must include:
- Complete threat lifecycle coverage. The Security Operations Center is responsible for every action surrounding a threat to the organization — the work doesn’t end when a threat is detected, and the “this is real!” verdict is made. An AI SOC must accelerate not only mean-time-to-detection or investigation, but also mean-time-to-response.
- Agentic operations: AI that plans, reasons, and executes end-to-end security tasks like determining real threats from false positives, extracting key attack details across disparate systems, or coordinating case management autonomously. And in successful deployments, AI can fully remediate alerts on its own.
- Automation modernization: Teams replace playbook-heavy systems with platforms designed for AI-speed workflow creation, better reuse, and stronger governance.
- More consistent execution: The SOC shifts from “people clicking buttons” to “processes that run consistently,” with humans approving sensitive actions.
Three principles define it:
- Agents drive execution. In a legacy SOC, execution depends on whoever is on shift and what they remember to do. In an AI SOC, every alert passes an AI Agent — not a static playbook that breaks when the threat deviates, but an adaptive process in which agentic AI reasons through the situation, selects the right tools to query, gathers evidence, and executes response actions within guardrails. The agent documents an immutable system of record for what happened and why each decision was made. Analysts don’t drive execution manually; they supervise it, intervene on escalations, and refine the logic over time.
- Cases centralize accountability. In most SOCs today, accountability is scattered across ticketing systems, Slack threads, email chains, and analyst memory. Nobody can see the full picture of a given incident without manually assembling it from five different tools. In an AI SOC, the case is the single source of truth — automatically created from correlated alerts, enriched with evidence from across the stack, prioritized by business impact, and tracked from detection through resolution. Every automated action, every AI decision, every human intervention is logged in one place. When leadership asks “what happened and how did we respond?” the answer lives in the case, not in someone’s head.
- Governance keeps automation from becoming a liability. Automation without governance accelerates risk. An AI SOC builds governance into the operating model itself: approval gates for high-impact actions, immutable audit trails for every decision, scope boundaries that limit what agents can touch, and regular validation cycles where the team reviews AI-closed cases to ensure accuracy. This isn’t a compliance checkbox bolted on after deployment. It’s the architecture that makes autonomy safe enough to trust at scale, and explainable enough to defend to auditors, insurers, and the board.
The shift from SOAR to AI SOC isn’t a tool swap. It’s a fundamental move from “we have some automation” to “AI-driven automation is how we operate” — with the structure, accountability, and controls to make that sustainable.
SOAR vs AI SOC: Key Differences
| Capability | Legacy SOAR | The Torq AI SOC Platform |
| How it works | Executes predefined playbooks built by engineers | Agentic AI reasons through alerts dynamically |
| Playbook dependency | Every scenario needs a playbook; no playbook = no automation | Investigates and responds without predefined workflows |
| Maintenance burden | High: Playbooks break when APIs change, or new threats emerge | Low: AI adapts to new patterns and learns from feedback |
| Alert coverage | Covers only the scenarios you’ve built playbooks for (typically 30–40%) | Investigates every alert, including novel and unknown threat types |
| Investigation depth | Enrichment and triage based on static logic | Contextual reasoning across the full stack, like an experienced analyst |
| Integration model | Custom scripting per tool; brittle at scale | 300+ native integrations, 4,000+ actions, AI-generated connectors |
| Time-to-value | 12–18 months for meaningful ROI (typical) | Days to weeks (Valvoline achieved ROI within 48 hours) |
| Human-in-the-loop | Binary: Fully automated or fully manual per playbook | Configurable guardrails: Autonomy calibrated by action type and risk |
| Scalability | Degrades under volume spikes; serial execution queues | Elastic, cloud-native; processes millions of events without bottlenecks |
| Skill requirement | Requires dedicated security engineers for playbook development | No-code builder + natural language interface accessible to any analyst |
This isn’t a matter of preference or maturity level. Legacy SOAR solutions fall short across every dimension that matters to a modern SOC: coverage, speed, maintenance costs, scalability, and accessibility. The only column where SOAR holds up is deterministic playbook execution for known scenarios… and Hyperautomation does that too, 10x faster.
The Case Against Keeping SOAR
The most common argument for staying on SOAR is sunk cost: “We’ve already invested in playbooks, and they work for what they cover.”
Consider what that actually means. Your team has spent years building automation that covers a third of your alerts. The other two-thirds sit in the queue or remain uninvestigated. SACR’s 2025 AI SOC Market Landscape research, based on a survey of 300+ CISOs, found that 40% of alerts are never investigated — and of those that are, 90% turn out to be false positives. That’s the reality of your SOAR investment.
Meanwhile, the engineering hours required to keep those playbooks functional keep climbing. Every vendor API update is a maintenance cycle. Every new tool in the stack needs custom integration work. Every novel threat type requires a new playbook that takes weeks to build and test. You’re running on a treadmill that speeds up every quarter.
And the talent math makes it worse. The engineers who built your SOAR playbooks are the same engineers every company in your industry is trying to hire. When one leaves, they take the tribal knowledge encoded in your automation with them. Legacy SOAR’s reliance on custom scripting and constant maintenance creates a dependency on scarce, expensive talent that most organizations can’t sustain.
SOAR’s deterministic model made sense when attack patterns were slower and more predictable. That era is over. Attackers use AI. They move at machine speed. They don’t wait for your team to write a new playbook.
Why AI SOC Is the Clear Path Forward
For organizations evaluating automation in 2026, AI SOC solves the problems SOAR created and the problems SOAR was never designed to address.
Coverage, not just speed. SOAR makes workflows faster. AI SOC investigates everything — 100% of alerts that hit your queue, not just the 30–40% with matching playbooks. That’s the difference between automating tasks and automating outcomes.
Adaptability over rigidity. Novel attack techniques, evolving TTPs, and multi-stage campaigns don’t wait for someone to write a playbook. Agentic AI investigates unfamiliar scenarios by reasoning through them — correlating signals, enriching context, making policy-aware decisions — not by pattern-matching against a static ruleset.
Accessible to your whole team, not just your engineers. Torq’s agentic workflow builder and natural language interface mean any analyst can build, modify, and trigger automations. You stop being dependent on two senior engineers who understand the Python scripts holding your playbooks together.
Time-to-value is measured in days. Valvoline was live on top-priority use cases within a week. A stalled Rapid7 integration that had been blocked for months under their legacy SOAR was delivered in days. They were saving 6 to 7 hours of analyst time every day from the start. Legacy SOAR implementations typically take 12–18 months to show meaningful ROI. That gap is 12–18 months of risk.
Scale without degradation. Legacy SOAR platforms queue work serially during volume spikes. When alert volume surges — exactly when you need your automation most — response times slip, pipelines back up, and containment gets delayed. Torq’s cloud-native architecture processes millions of daily security automations without bottlenecks because it was built for elastic scale from the start.
“But What About My Existing Playbooks?”
This is the question that keeps teams on legacy SOAR longer than they should be. It’s also the question Torq was designed to answer. Migrating to Torq Hyperautomation doesn’t mean burning down what you’ve built. It means running it better — and adding capabilities your SOAR platform could never deliver.
Your proven workflows run on Torq’s Hyperautomation layer, executing 10x faster than they did on legacy SOAR. Your integrations stay intact through 300+ native connectors. And on top of that orchestration layer, Torq’s multi-agent system handles the agentic investigation, autonomous triage, and adaptive response that your playbooks never covered.
Deepwatch standardized its entire global security infrastructure on Torq after leaving legacy SOAR, recreating years’ worth of automations in weeks. RSM migrated 200+ managed customers in three weeks. Lennar Corp. replaced XSOAR and cut phishing response from hours to minutes. None of them started from scratch. All of them got more from Torq in weeks than they got from SOAR in years.
The migration path is straightforward. Torq’s team helps you audit your current SOAR workflows, integrations, and pain points — prioritize key use cases, and define measurable success metrics before you start. The JumpStart implementation program gets priority use cases live fast, and Torq Academy, plus 24/7 access to the Knowledge Base, ensures long-term adoption.
Staying on legacy SOAR to protect an existing investment is like keeping a pager because you already paid for the service plan. The cost of staying is higher than the cost of switching.
Decision Framework: How to Know It’s Time to Move
Be honest about where your SOC is today. These five questions will tell you whether your SOAR investment is still working — or whether it’s holding you back.
1. What percentage of your alerts are actually investigated? If the answer is under 80%, you have a coverage gap that playbooks can’t close. AI SOC investigates everything. SOAR only covers what someone built a workflow for.
2. How many full-time engineers maintain your automation? If you need dedicated security engineers just to keep playbooks running, your automation has become a cost center and your talent is being underutilized. Modern platforms reduce engineering dependency; they don’t require it.
3. How long does it take to operationalize a new use case? If the answer is weeks or months, your automation can’t keep pace with your threat landscape. Torq customers operationalize new workflows in minutes using natural language or the no-code builder.
4. What happens when an alert doesn’t match an existing playbook? If it sits in the queue, your automation gap grows every time a new attack technique emerges. Agentic AI investigates novel scenarios without waiting for someone to write the logic.
5. How does your platform perform during alert volume spikes? If response time degrades when you need it most, your architecture has a structural problem that more playbooks won’t fix.
If you answered honestly and two or more of these points to problems, your SOAR isn’t serving you anymore. It’s time to evaluate what replaces it.
SOAR Promised Automation. AI SOC Delivers It.
SOAR was an important step. It proved that security operations could benefit from automation and orchestration. But it also proved that static playbooks, custom scripting, and code-heavy platforms can’t keep pace with a threat landscape that moves at machine speed.
AI SOC — powered by agentic AI and Hyperautomation — delivers what SOAR always promised: every alert investigated, every response executed fast, every action auditable, and your analysts focused on work that actually requires human judgment. Not 30% of alerts. All of them.
The organizations that have already made the switch aren’t looking back. Carvana. Valvoline. Deepwatch. RSM. Kenvue. They didn’t settle for incremental improvements to a broken model. They replaced it.
Your SOAR had its run. See what comes next.
FAQs
SOAR automates predefined workflows through static playbooks that require engineering resources to build and maintain. AI SOC platforms use agentic AI to investigate, reason through, and respond to alerts autonomously — including threat scenarios no playbook exists. SOAR handles a subset of known, repeatable processes. AI SOC handles the full spectrum at machine speed.
Yes. AI-native Hyperautomation platforms like Torq do everything SOAR does — orchestration, automation, case management — but faster, with less maintenance, and without the playbook ceiling that limits SOAR’s coverage. Torq also adds agentic AI investigation and autonomous response that SOAR architectures can’t deliver. GigaOm has named Torq a leader and outperformer for three consecutive years for exactly this reason.
Torq is the leading SOAR alternative. It combines the orchestration capabilities of SOAR with agentic AI that reasons, adapts, and responds without rigid playbooks — executing workflows 10x faster than legacy SOAR with 300+ native integrations and a no-code builder accessible to any analyst. Customers such as Valvoline, Carvana, Deepwatch, and RSM have migrated from legacy SOAR solutions and achieved measurable results within days.
With Torq, migration happens in days or weeks. RSM migrated 200+ managed customers in three weeks. Valvoline replaced its legacy SOAR and was live on priority use cases within one week, achieving ROI in 48 hours. Compare that to the 12–18 months of legacy SOAR that typically require before delivering meaningful value.
They don’t disappear. Torq’s orchestration layer runs existing workflows 10x faster than legacy SOAR, while the AI SOC layer adds agentic investigation, autonomous triage, and adaptive response on top. Organizations like Deepwatch recreated years’ worth of legacy automations in weeks on Torq — and immediately started building capabilities their SOAR could never deliver.