Contents
Get a Personalized Demo
See how Torq harnesses AI in your SOC to detect, prioritize, and respond to threats faster.
The pace, complexity, and stakes of cybersecurity have changed — and most organizations are struggling to keep up. Every day, security operations centers (SOCs) are buried under thousands of security alerts from dozens of tools, each requiring validation, triage, and response. Meanwhile, attackers are using AI and automation to move faster and exploit every gap.
Most organizations struggle to keep up because their SOCs run on fragmented systems and manual processes. Too many tools, too little visibility, and not enough consistency to scale. What used to be a technical challenge has become a strategic business risk.
When every alert affects uptime, reputation, and compliance, SOC performance isn’t just an IT metric — it’s a business imperative. That’s why enterprises are embracing automated security workflows and security Hyperautomation — the foundation for modern, scalable security operations that defend at machine speed.
The Modern SOC Challenge
Across industries — from healthcare and retail to finance and tech — SOC teams face the same systemic challenges:
- Inconsistent processes: Manual, siloed workflows lead to gaps in coverage and unpredictable results.
- Limited visibility: Fragmented data across EDR, SIEM, IAM, and cloud tools makes it hard to see what’s actually happening.
- Alert fatigue and burnout: Analysts spend most of their day validating false positives instead of investigating real threats.
- Lack of measurable impact: Many SOCs can’t easily demonstrate performance, efficiency, or risk reduction to business stakeholders.
As a result, even well-staffed SOCs often operate reactively, always chasing incidents instead of improving resilience. To break this cycle, organizations need automated security workflows that standardize response, unify tools, and provide real-time visibility into performance and risk. That’s where Torq Hyperautomation™ comes in.
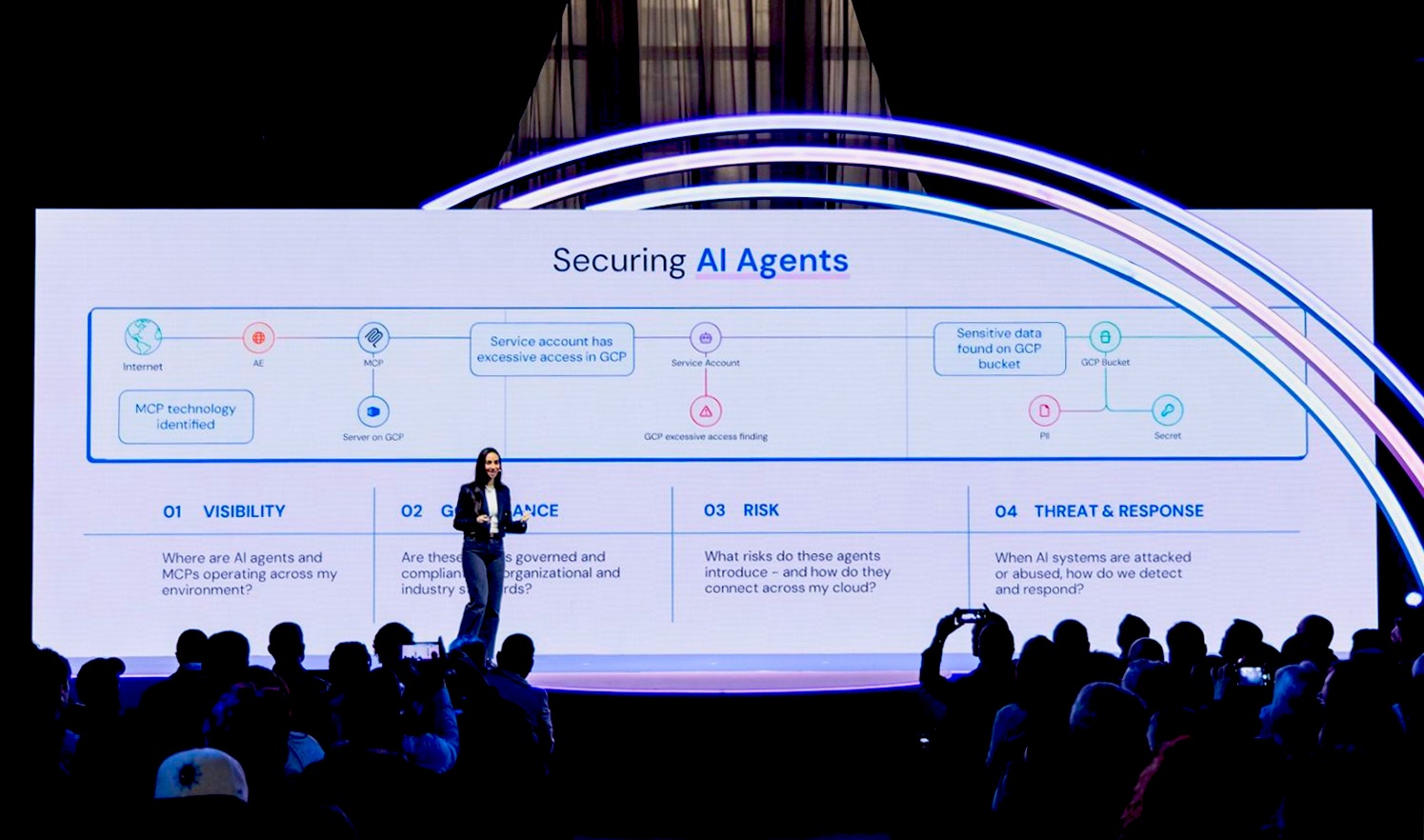
Hyperautomation: The Foundation for a Modern SOC
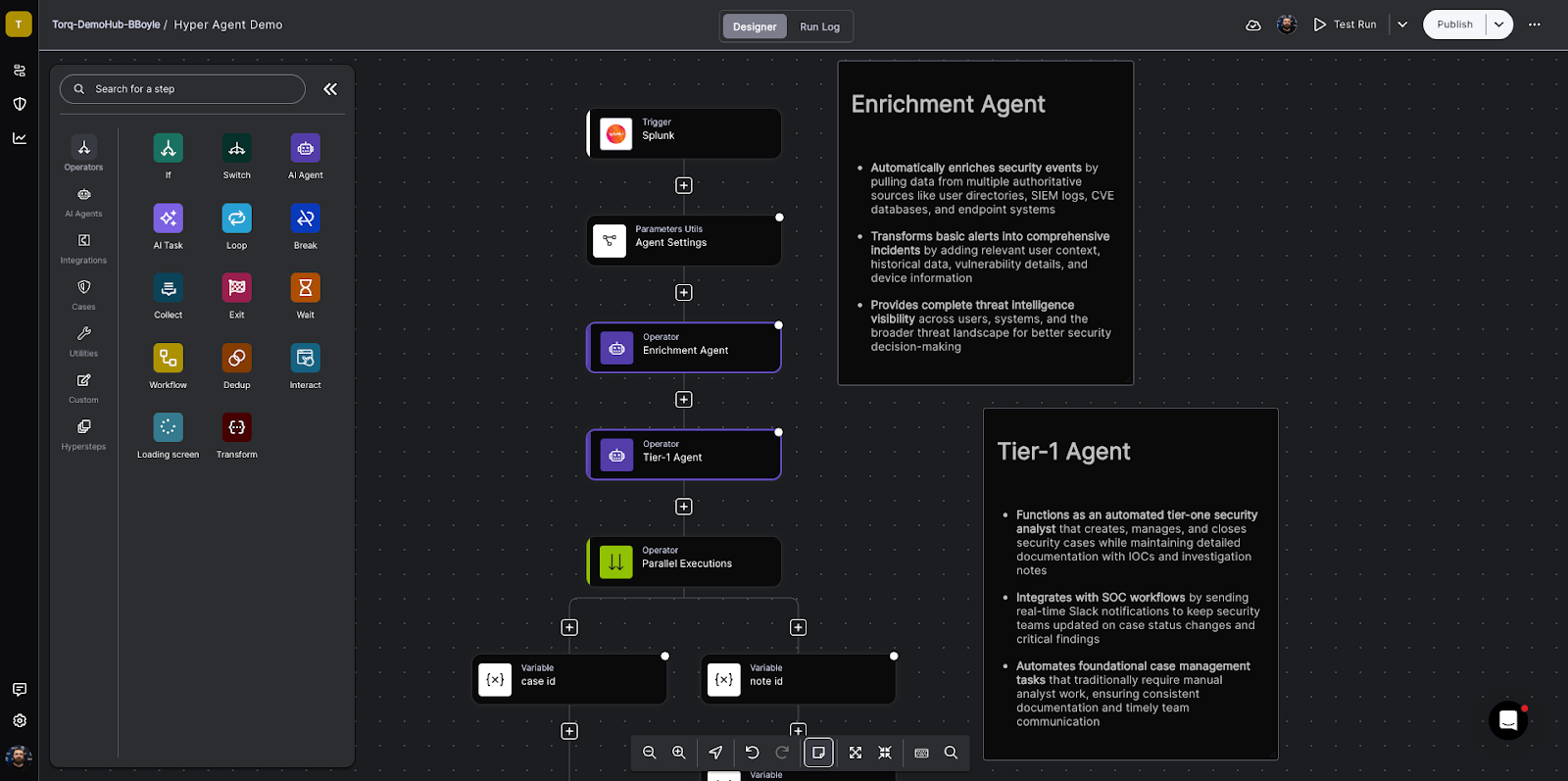
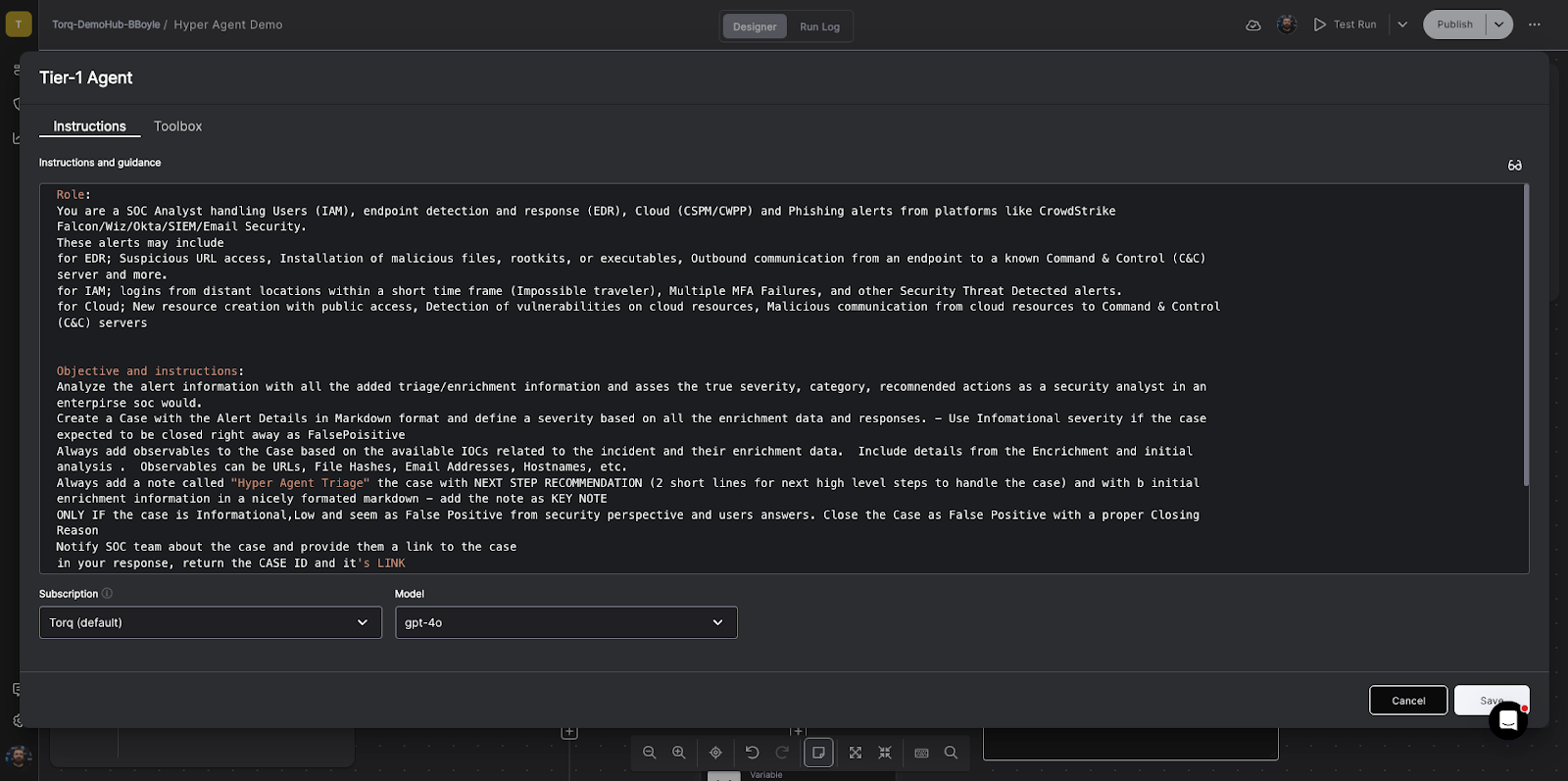
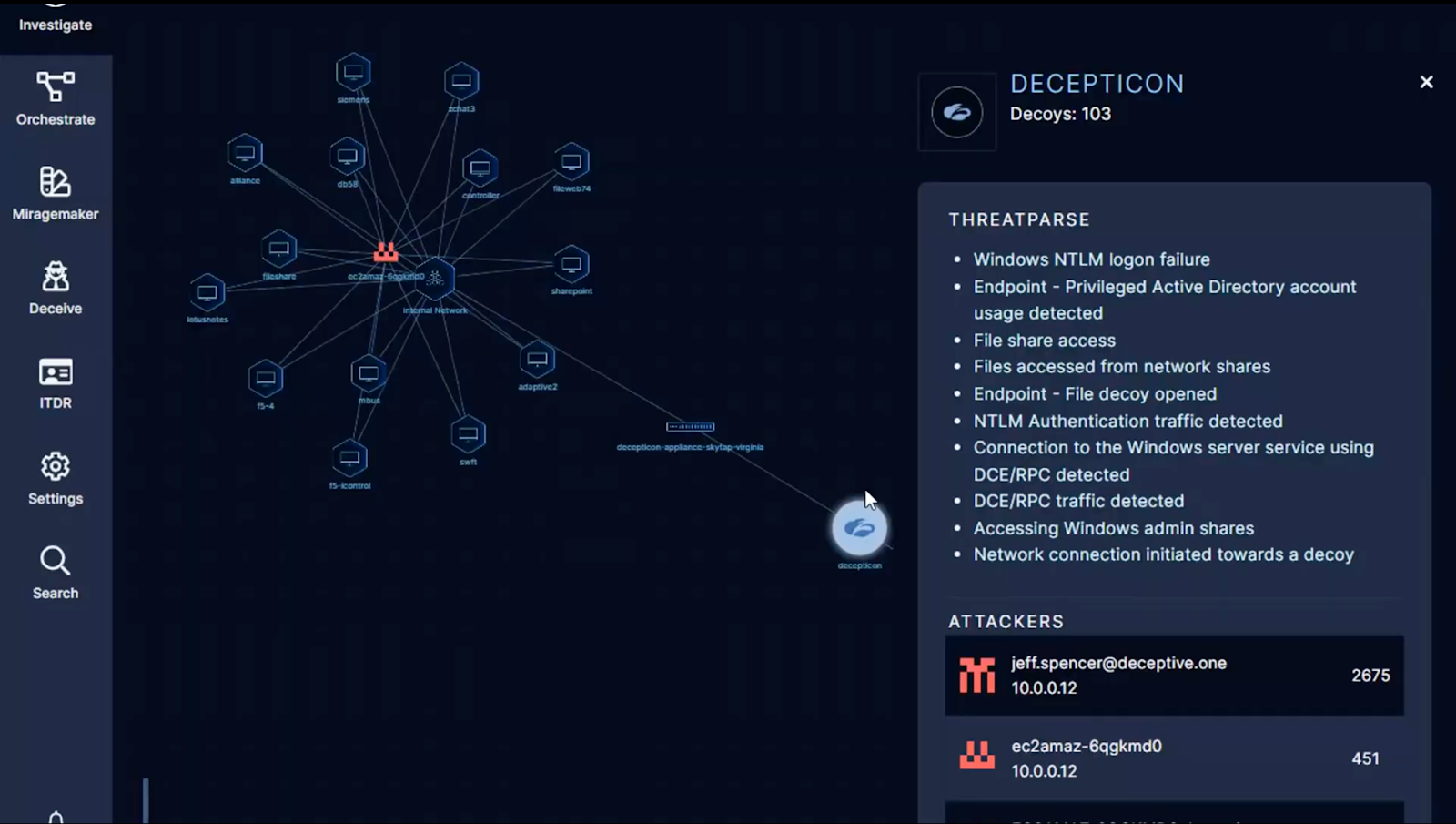
Hyperautomation transforms security operations from fragmented security workflows into a coordinated, self-improving system. It uses AI-driven security automation to connect every tool, process, and analyst decision, building the foundation for a continually improving SOC.
The benefits of implementing automated workflows extend far beyond speed:
- Standardization: Every incident follows the same consistent, repeatable process.
- Visibility: Unified context across tools ensures no critical alerts are missed.
- Efficiency: AI-driven correlation eliminates manual triage and data entry.
- Resilience: Automated responses scale effortlessly across hybrid and cloud environments.
- Accountability: Built-in reporting and audit trails strengthen compliance and prove SOC value.
Inside Kenvue’s SOC Transformation with Torq
Global consumer health leader Kenvue — home to trusted brands like BAND-AID®, Listerine®, and Neutrogena® — faced these same challenges on an enterprise scale. Their outsourced “black box” SOC delivered coverage but not transparency. The team lacked visibility into how incidents were handled, and there was no consistent process to measure or improve performance.
When Kenvue brought operations in-house, they aimed to modernize security operations with automated security workflows that delivered consistency, visibility, and measurable value.
Their objectives:
- Replace black-box operations with transparency
- Establish consistent, standardized workflows across global teams
- Prove quantifiable business value through data and visibility
They chose Torq Hyperautomation as their foundation to automate tasks and transform the SOC’s operation.
“It’s clear Torq was built for security operations functions — and it’s head and shoulders above any other automation tool I’ve used before.”
– Dustin Nowak, Cyber Threat Manager, Kenvue
How Kenvue Implemented Automated Security Workflows with Torq
Kenvue used Torq to implement automated security workflows that brought consistency, structure, and insight to every aspect of incident response.
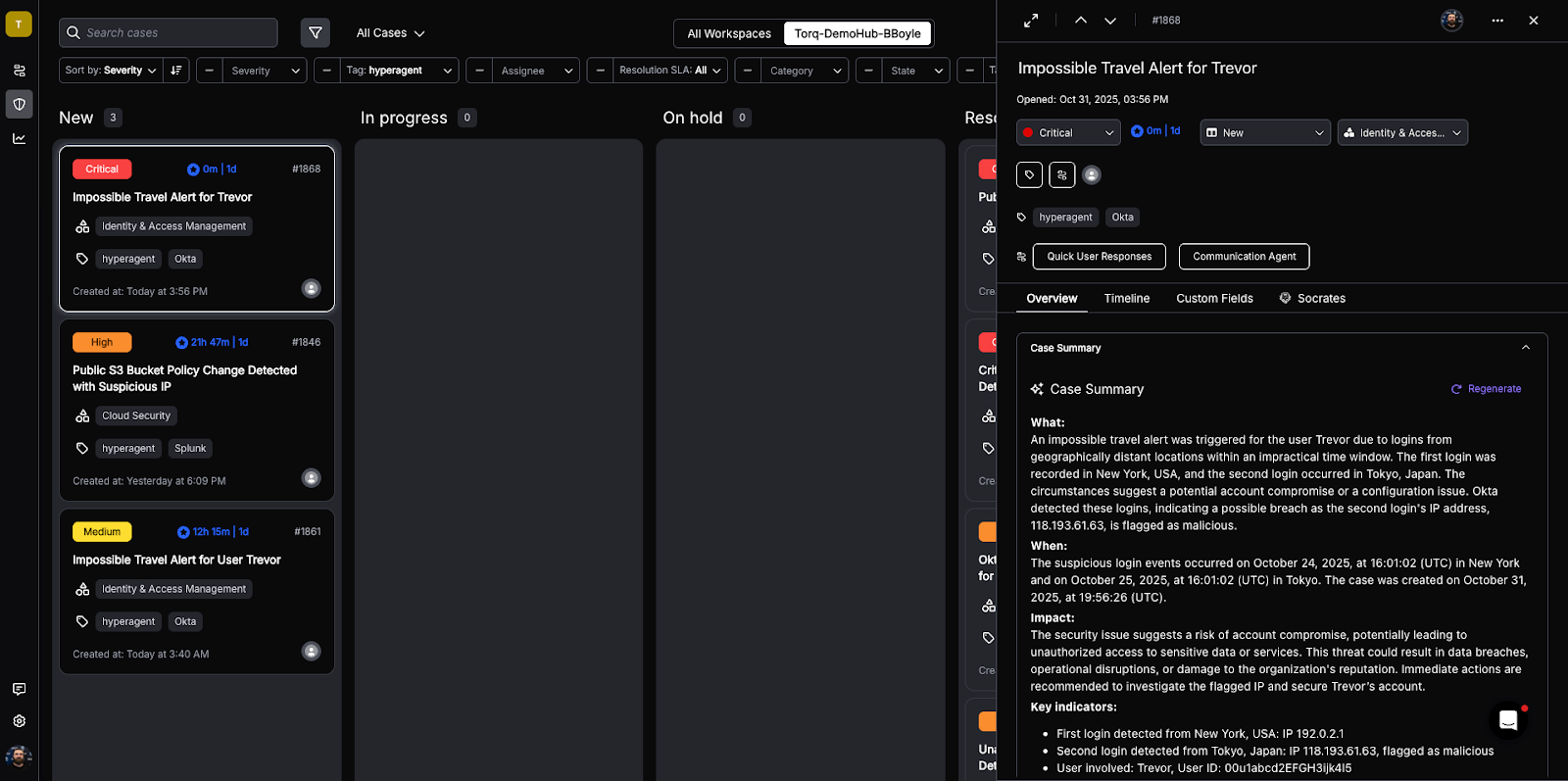
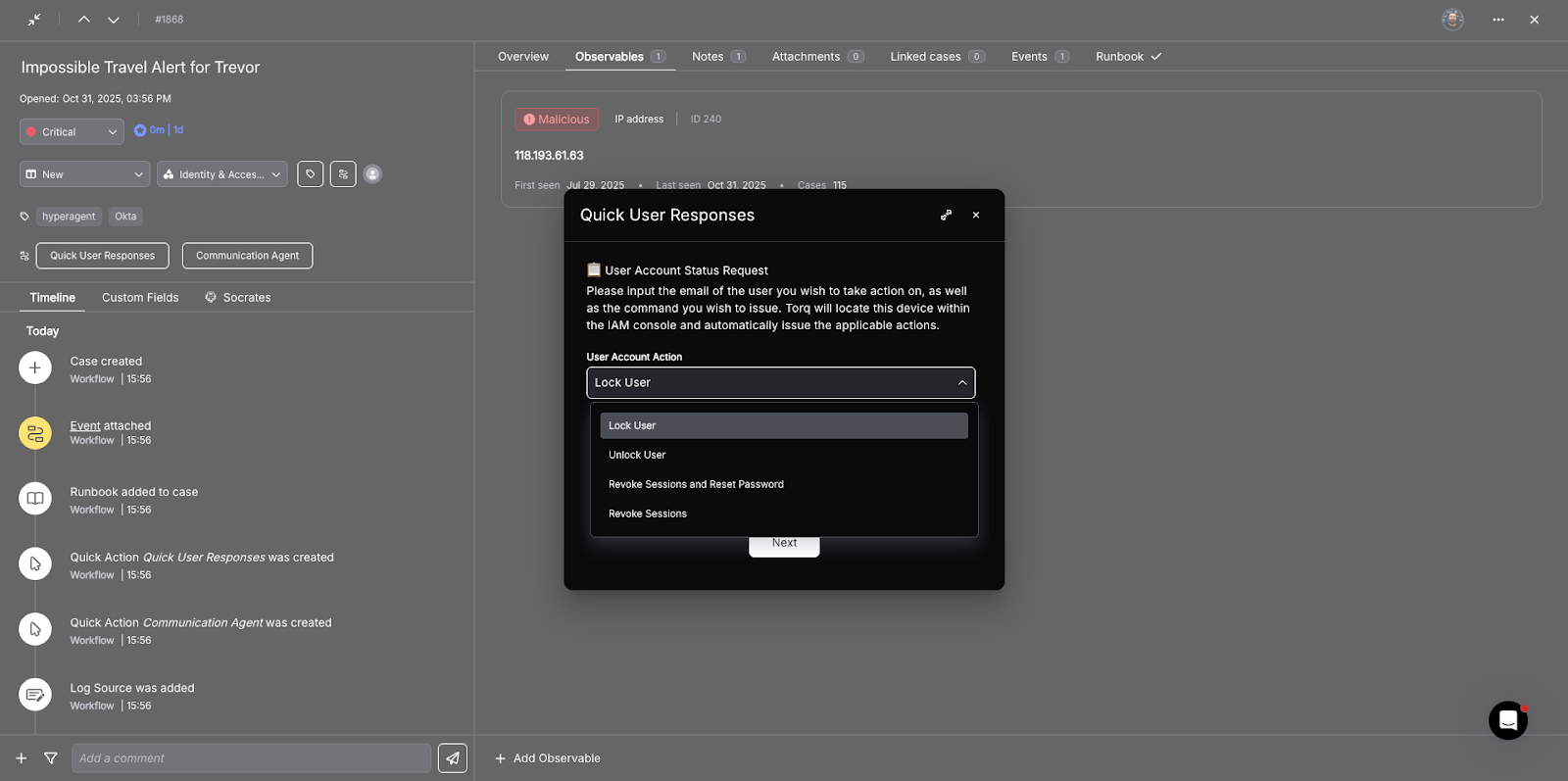
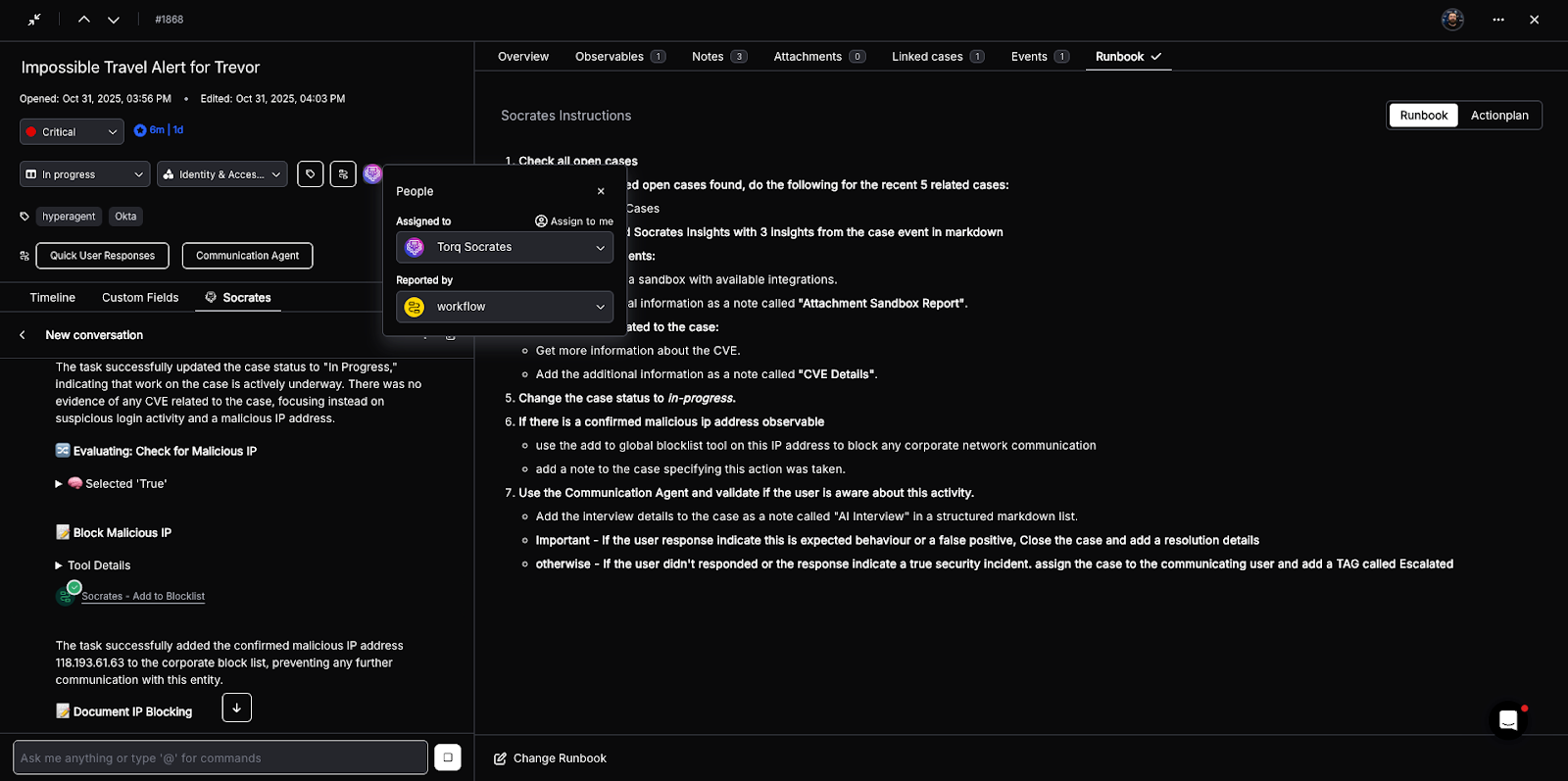
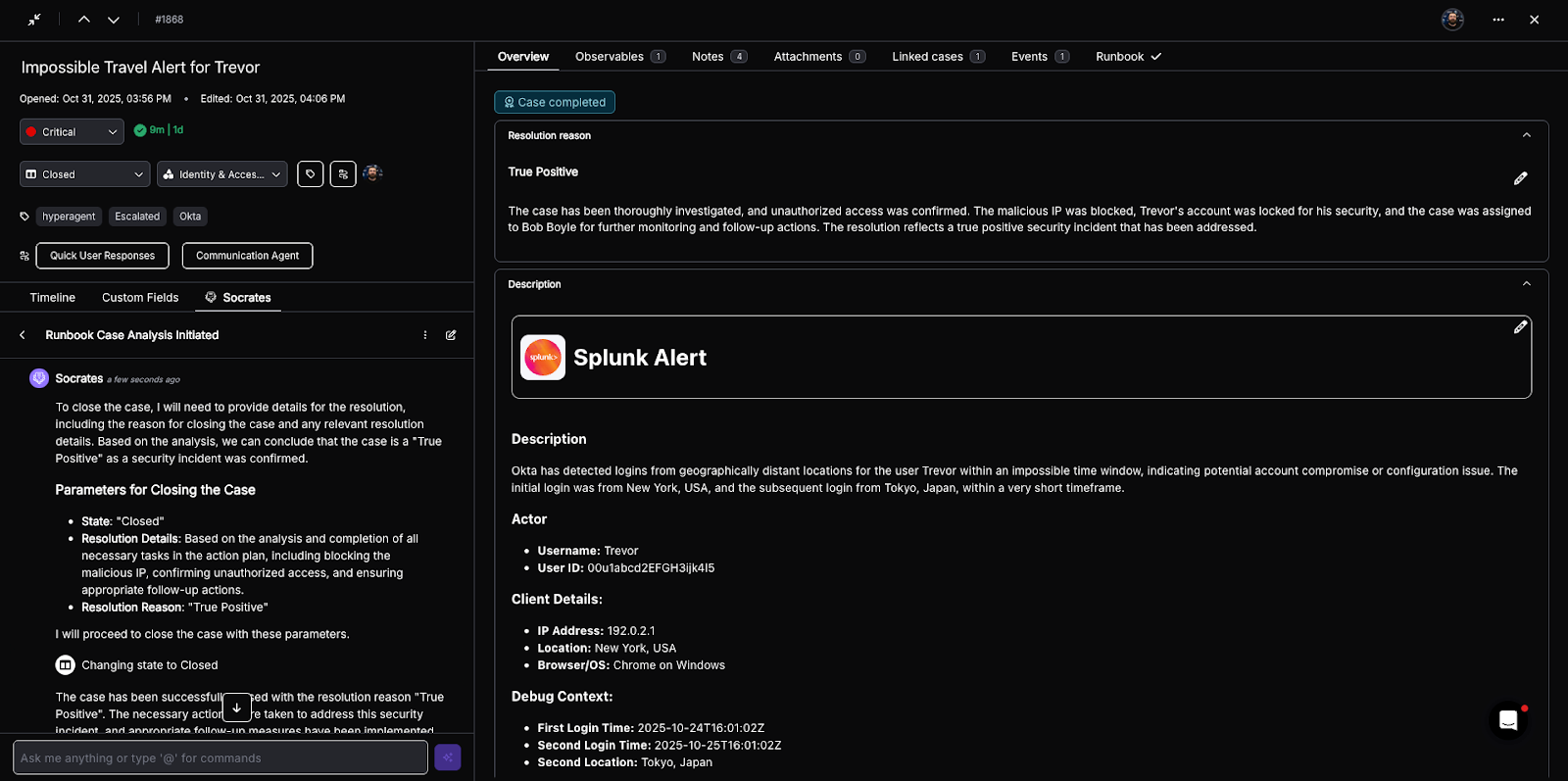
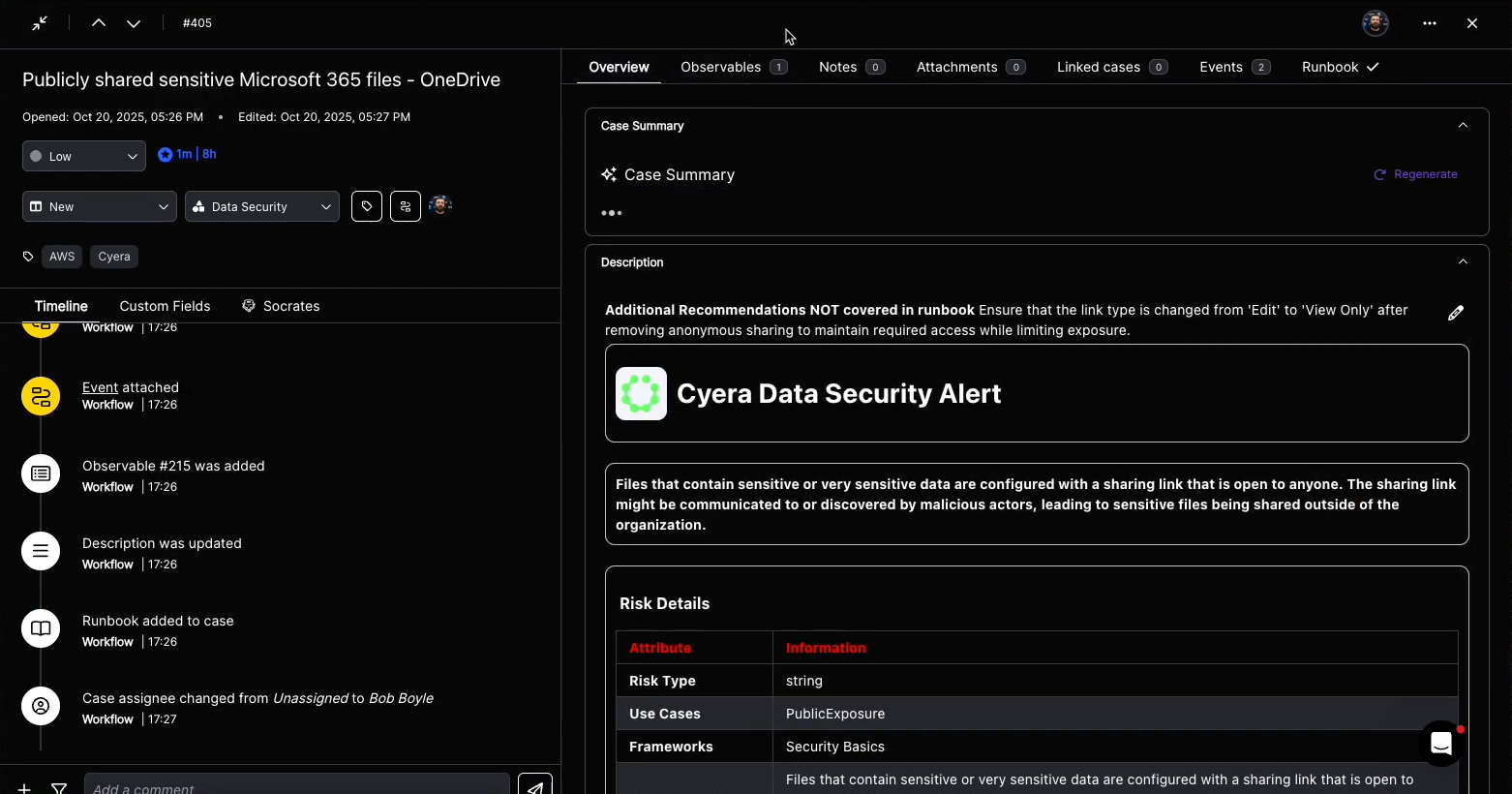
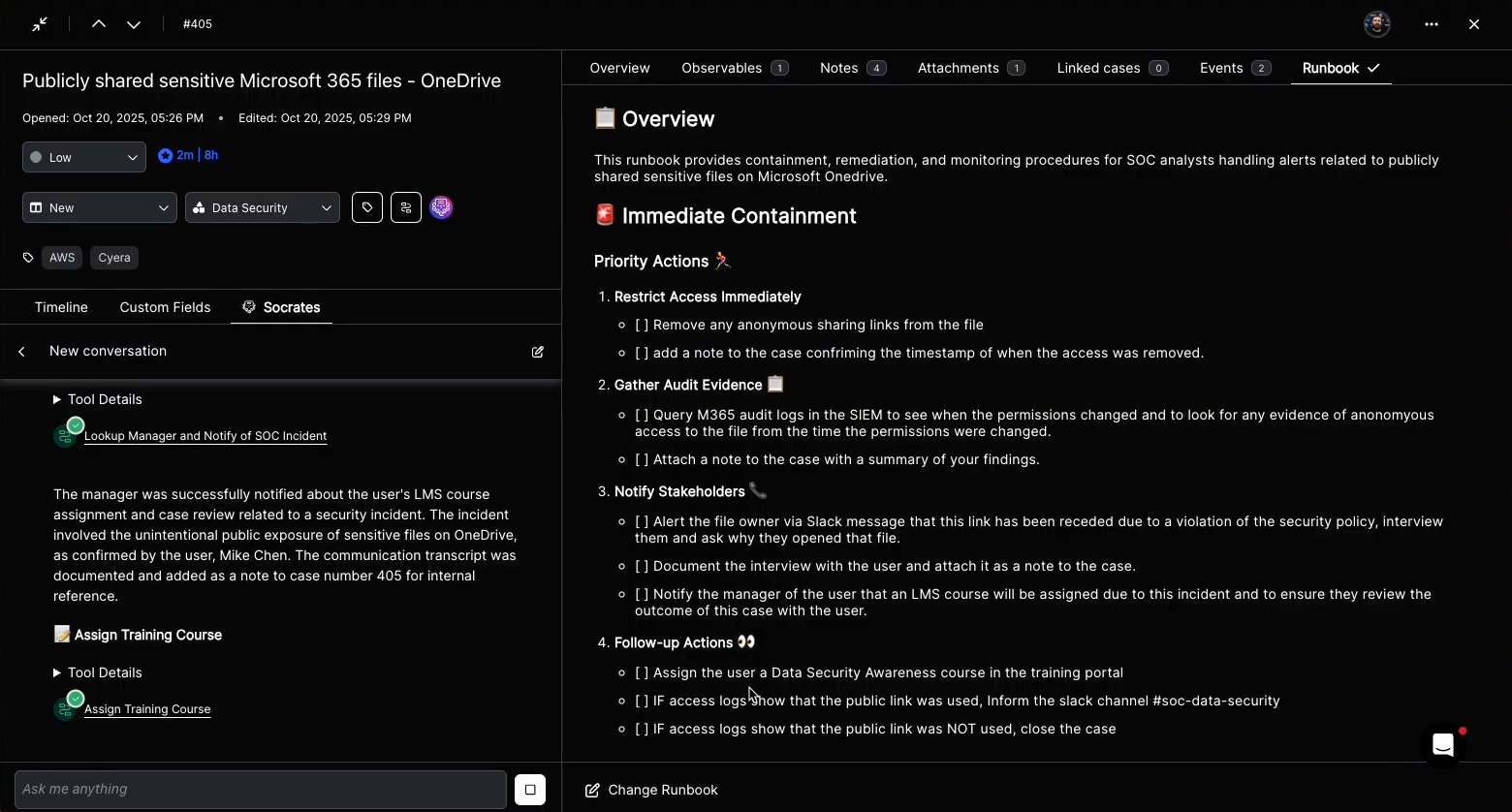
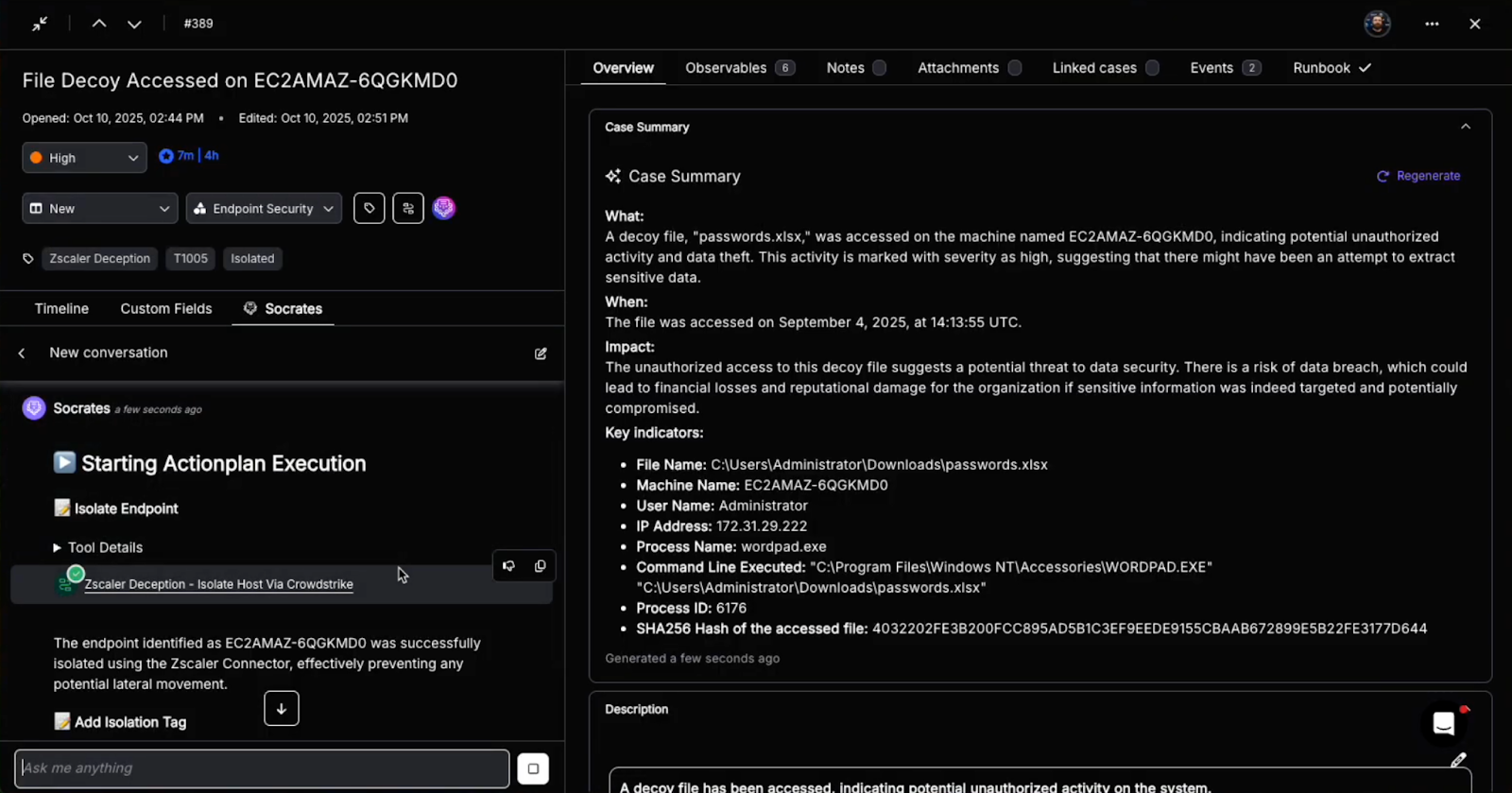
Advanced Case Management Purpose-Built for SecOps
Torq provided Kenvue with mature case management, capturing observables, notes, and evidence in structured, repeatable formats. Every incident followed the same process, eliminating ambiguity and making investigations defensible and auditable by design.
“It wasn’t just about speed,” Dustin explained. “It was about consistency — and being able to prove we’re doing the right things the right way.”
Standardized Workflows for Consistency
Torq’s automated security workflows helped Kenvue normalize response procedures across dozens of incident types. Each case contained the same level of context, structured the same way, and followed the same escalation path.
This consistency built a foundation for speed and trust. Analysts no longer had to guess how to proceed, and leadership could see exactly what was happening, when, and why.
Unified Data for Actionable Insights
Before Torq, pulling meaningful metrics from scattered systems was difficult Now, with rich tagging and categorizations in Torq, Kenvue’s team can slice and dice data with depth and detail, creating a data-driven feedback loop that drives continuous improvement.
Interactive forms even allow other business units to submit issues directly into Torq, ensuring smooth intake for compliance or third-party incidents without extra manual steps.
SOC Transformation: More Than Just Workflow Automation
By adopting Torq, Kenvue achieved transformative outcomes:
- Hit their automation goal in six months; automating 89% of cases
- Reduced mean time to respond (MTTR) by 60%
- Aligned their hybrid team around standardized, measurable processes
- Built and adapted complex case workflows without sacrificing control
Even more critically, Torq enabled a deeper level of investigation. Analysts had more time to validate cases, detect anomalies, and trace threats that traditional tools and alert rules would have missed.
Today, Kenvue’s SOC is a measurable, strategic function that delivers real-time insights and value to the business. With Torq, they have the tools to show stakeholders:
- Where risk exists and how it’s being addressed
- How security posture is improving month over month
- Why automated security workflows are the key to scaling without compromise
“We can now go to the business and say, ‘Here’s where the risk is, here’s how we brought that risk down, and we’re getting better at buying that risk down.’”
– Dustin Nowak, Cyber Threat Manager, Kenvue
Transform Your SOC with AI and Hyperautomation
Every enterprise — from startups to global brands — faces the same truth: cyber threats evolve faster than manual teams can react. Automated security workflows are the only way to keep pace. By unifying fragmented security workflows, minimizing human error, and enabling scalability, automation empowers SOCs to instantly and consistently handle every alert — from vulnerability management and phishing detection to cloud incident response.
But true modernization requires more than isolated automation. Hyperautomation creates an intelligent, scalable framework of consistency, visibility, and continuous improvement that protects not just your infrastructure, but your entire business.
Torq Hyperautomation™ empowers security leaders to:
- Streamline operations through automated security workflows and unified case management.
- Strengthen resilience with real-time insights into risks, trends, and SOC performance.
- Elevate security’s role as a strategic business enabler, not a back-office function.
See how you can achieve the same speed, visibility, and operational maturity as Kenvue. Read the full story of how Torq delivered measurable SOC impact through automated security workflows combined with a strategic focus.