Contents
Get a Personalized Demo
See how Torq harnesses AI in your SOC to detect, prioritize, and respond to threats faster.
Last Updated December 2025
The security operations center (SOC) is the heart of modern cybersecurity, but as threats scale, so must your ability to respond. That’s where SOC automation comes in.
SOC automation transforms how security teams detect, investigate, and remediate threats by eliminating repetitive manual work. Automated SOCs boost speed, efficiency, and accuracy, helping analysts focus on what matters most.
This guide explains SOC automation, how it works, why it matters, and why it’s now an essential part of every cybersecurity strategy.
What Is a SOC, Exactly?
A SOC (pronounced “sock”) is the part of a business that is responsible for managing and mitigating security threats.
A SOC is made up of the people and tools that handle:
- Threat intelligence: Gathering data about emerging threats, vulnerabilities, and attack patterns that could impact the organization.
- Monitoring and alerting: Continuously scanning systems for signs of malicious activity to detect risks and trigger alerts in real time.
- Analysis: Investigating detected threats to uncover their root cause and assess their potential impact.
- Response: Executing containment, mitigation, and remediation strategies to neutralize active threats.
- Recovery: Restoring affected systems and services to a secure, operational state after an incident.
- Reporting: Reviewing the incident to understand what happened, why it occurred, and how to prevent it from recurring.
A SOC doesn’t have to be a physical room — it’s an operational function. Whether your team is remote or in-house, if they handle the tasks above, you’ve got a SOC. But traditional SOCs are drowning in alerts and overrun with manual processes. That’s where automation comes in.
What Is Security Operations Automation?
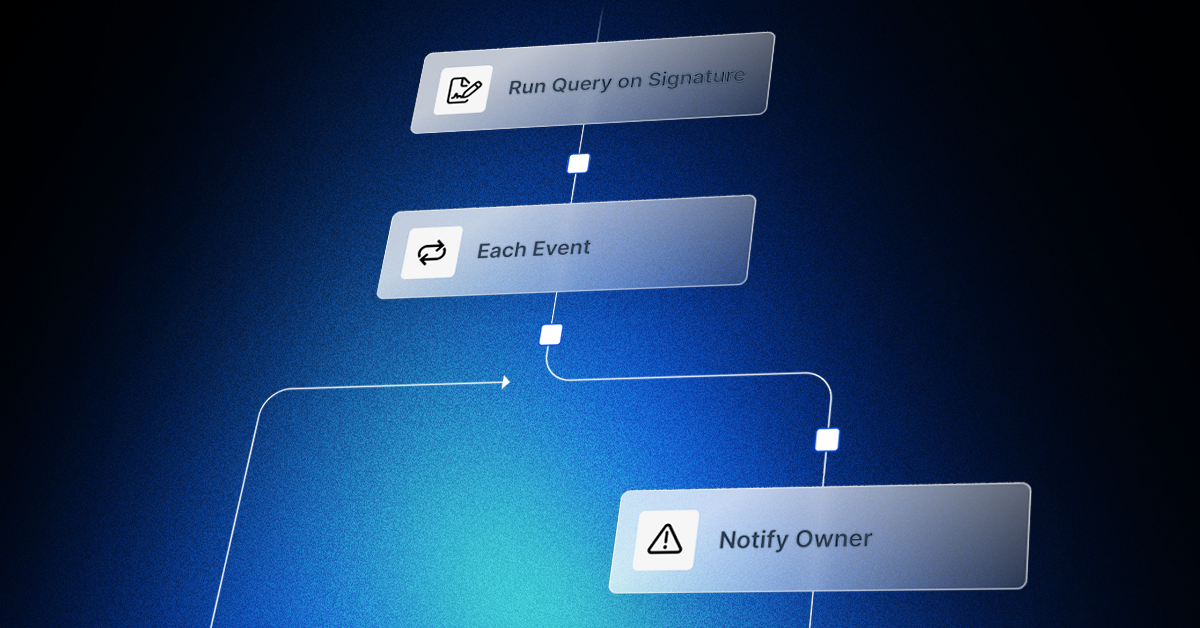
SOC automation replaces manual security tasks with technology-driven workflows.
Instead of relying solely on human analysts, SOC automation tools handle tasks like:
- Parsing and prioritizing threat intel
- Detecting anomalies in real time
- Running initial triage and investigations
- Automating incident response playbooks
- Generating compliance and incident reports
At its core, security operations automation is the process of using AI and automated workflows to streamline and accelerate SOC tasks. Instead of analysts manually reviewing every alert or running every investigation step, SOC automation tools handle routine tasks automatically — from alert triage to threat containment — freeing human analysts to focus on strategic, high-value work.
An automated SOC integrates all the moving parts of your security ecosystem — SIEM, EDR, IAM, CSPM, and more — into a unified, intelligent system that detects, investigates, and remediates threats with minimal human intervention. This allows security teams to act faster, reduce their workload, and free up time for strategic, higher-value activities.
How Automation Transforms the SOC
In a traditional SOC, analysts juggle endless alerts from disconnected tools. Each alert requires manual correlation, validation, and response — a process that’s slow, error-prone, and unsustainable at scale. SOC automation replaces that manual grind with automated workflows and AI-driven orchestration.
Here’s how SOC automation works:
- Data ingestion and normalization: Automation platforms continuously pull data from every tool — SIEMs, firewalls, EDR, and cloud platforms — and normalize it into a single, unified view.
- Alert triage: Automated playbooks instantly sort, classify, and prioritize alerts based on severity, risk level, and context.
- Data enrichment: AI and threat intelligence integrations add context (such as IP reputation, geolocation, and behavioral data) so analysts see the full picture.
- Incident response: Predefined workflows automatically execute containment steps, like isolating endpoints or blocking malicious IPs, in real time.
- Reporting and documentation: Every action is logged and reported automatically, ensuring accuracy and compliance without manual effort.
Isn’t Every SOC Already Automated?
Sort of. Most SOCs today use basic automation — for example, tools that scan logs or monitor systems for anomalies. But complex, context-rich actions like investigation and response are still mostly manual.
SOC automation takes things further, bringing intelligence and orchestration to processes that traditionally required human action and judgment. This is especially true when using tools like Torq HyperSOC™, which leverages agentic AI to drive autonomous SOC operations.
Why SOC Automation is Critical Now
Cybersecurity teams are being asked to do more with less. That’s why automated SOC platforms are becoming a must-have for modern security to deal with:
- Alert overload. Analysts receive thousands of daily alerts, most of which are noise, which can lead to SOC alert fatigue.
- Manual investigation is too slow. Threat actors can move laterally within minutes.
- Staffing shortages. The cybersecurity talent gap continues to widen, with a global shortage of 4 million cybersecurity professionals.
- Cloud complexity is growing. Hybrid, multi-cloud, and SaaS environments require faster, scalable SecOps.
Compliance pressure is increasing. Automation helps meet standards like NIST, ISO, SOC 2, and GDPR with less overhead.
12 SOC Automation Use Cases
- Identity and Access Management (IAM): SOC automation streamlines IAM by automating user lifecycle tasks, access approvals, and credential management. This reduces manual errors, prevents unauthorized access, and simplifies compliance.
- Threat Hunting: Automated threat hunting continuously scans for suspicious activity, enriches alerts with context, and accelerates investigations, helping teams proactively detect and respond to threats faster.
- Cloud Security Posture Management (CSPM): SOC automation monitors multi-cloud environments for misconfigurations and policy drift, triggering remediation workflows to maintain consistent security and compliance.
- Email Security: An automated SOC can detect and respond to phishing and malware threats by correlating data across email and endpoint systems, removing malicious messages, and adjusting protections in real time.
- Chatbots: Self-service chatbots handle routine IT and security tasks, like password resets and access revocations, directly in messaging platforms, reducing SOC workload and improving user response time.
- Incident Response: Accelerates incident response by automatically triaging alerts, containing threats, executing remediation steps, and notifying stakeholders, all while preserving evidence and logging actions.
- Application Security: Integrates with integration and delivery pipelines to automate vulnerability detection and response, enabling secure development without slowing down releases or requiring manual review.
- Phishing Response: SOC automation can help with phishing detection, email and attachment analysis, and user account protection.
- Continuous Vulnerability Management: With automation, SOCs can scan, prioritize, and remediate vulnerabilities using contextual insights, enabling teams to quickly resolve issues without needing to sift through raw data.
- Threat Intelligence Enrichment: Automation enriches raw threat data with external context, like geolocation, known malware links, or infrastructure details, to enhance detection accuracy and inform response decisions.
- Suspicious User Activity Response: Automatically detect and instantly respond to risky user behavior instantly by alerting users to verify their actions or locking accounts if malicious activity is confirmed.
- Secure Access to Sensitive Data: SOCs can automate access controls, enforce authentication policies, and monitor for anomalies, ensuring only authorized users access specific systems and data.
The Benefits of SOC Automation
SOC automation delivers measurable benefits that extend far beyond efficiency. It improves detection, reduces burnout, and creates a repeatable, reliable foundation for continuous improvement.
- Enhanced threat detection and response: Automated SOC workflows correlate data across sources, identify real-time anomalies, and execute responses immediately. This shortens the mean time to detect (MTTD) and mean time to respond (MTTR), minimizing attacker dwell time.
- Reduced analyst fatigue and burnout: Automation filters noise and handles repetitive triage, freeing analysts from alert fatigue. Teams can focus on more engaging work like proactive defense and threat hunting, improving morale and retention.
- Improved scalability and cost efficiency: With automation, SOCs can process thousands of security alerts without increasing headcount. Teams achieve greater coverage with fewer resources, optimizing ROI and operational cost.
- Consistent security responses: Standardized, automated playbooks ensure every alert or incident receives a consistent, policy-aligned response. This eliminates guesswork, reduces error rates, and supports compliance efforts.
How Torq Revolutionizes SOC Automation
Torq HyperSOC™ is the first agentic, AI-powered SOC automation platform built to transform your SecOps from reactive to truly autonomous. That means the majority of threats are detected, triaged, investigated, and remediated without human intervention — no bottlenecks, no burnout, no babysitting. Only the most critical events are escalated to human analysts, alongside full case context so they can get up to speed quickly.
So, how does it work?
- Integrates with everything: From SIEMs to EDRs, CSPMs to IAM, SaaS apps to custom tools — Torq connects your entire security stack instantly.
- AI Agents: At the core of HyperSOC is Socrates, our AI SOC Analyst. It coordinates a squad of specialized AI Agents that handle everything from threat detection to response.
- Natural language human-AI collaboration: Build and trigger powerful automations using plain English commands. Just tell Torq what you want, and it gets done.
- Automate at scale: Whether you’re securing cloud, hybrid, or on-prem environments, Torq can run thousands of workflows simultaneously, automatically scaling to match your environment and threat landscape.
- Customize: Torq’s open architecture and rich API make it easy to tailor automations to your exact needs.
12 Ways Torq Delivers Next-Level SOC Automation
1. Identity Access and Management
With Torq, security teams can automate the entire IAM lifecycle, from access approvals and permission adjustments to proactive policy enforcement and investigations of suspicious activity. Self-service chatbots let users resolve access issues in seconds. AI-driven workflows ensure only the right people have the proper access at the right time.
2. Threat Hunting
Torq’s AI-powered threat hunting automation scans massive datasets, correlates anomalies, and surfaces real threats fast. GPT-backed agents enrich alerts with context, cut through noise, and help analysts uncover hidden indicators of compromise (IOCs) across fragmented stacks.
3. Cloud Security Posture Management
Torq continuously scans for cloud misconfigurations, policy drift, and compliance gaps, then auto-remediates before they become problems. Integrated with AWS, Azure, GCP, and Kubernetes, Torq enforces policies, rolls back unauthorized changes, and triggers response workflows across teams and tools.
4. Email Security
Email is the #1 attack vector. Torq automates email phishing detection, triages alerts, removes malicious emails post-delivery, and hardens security controls on the fly. It connects with SEGs, EDR, and threat intel to shut down campaigns before they spread.
5. Chatbots
Torq’s always-on self-service chatbots bring intelligent support directly into tools like Slack, Microsoft Teams, and Discord. These chatbots let users report phishing, reset passwords, revoke access, or run malware scans instantly. They notify users about threats, deliver trainings, and keep everyone engaged.
6. Incident Response
Enabling always-on, automated threat containment and remediation that slashes response time and minimizes risk without burning out your SOC team, Torq uses generative AI to intelligently triage alerts by severity and potential impact, ensuring high-priority threats are addressed first.
Once detected, Torq immediately executes containment procedures, such as isolating systems or blocking malicious IP addresses, followed by automated remediation steps, including patching, firewall updates, and malware removal. It alerts all relevant stakeholders in real-time, updating threat intelligence feeds with new IoCs. It preserves key evidence for investigations, all while maintaining a detailed, auditable log of every action.
7. Application Security
Torq embeds automation into the CI/CD pipeline to detect and fix issues in code, containers, and APIs before they reach production. It connects to SAST, DAST, RASP, WAFs, and more to auto-prioritize vulnerabilities and trigger remediations — without bogging down devs.
8. Phishing Response
Torq handles phishing from inbox to endpoint. Our platform orchestrates across SEGs, EDR, CASBs, IAM, and chatbots to detect, isolate, and respond to phishing campaigns. Users can report suspicious emails via chatbot, triggering instant investigations, credential resets, and threat removal automatically.
9. Continuous Vulnerability Management
Torq turns vulnerability management into a zero-touch, closed-loop system. It orchestrates scans, prioritizes based on real risk, and kicks off remediations — all autonomously. Agentic AI ensures critical issues get fixed fast, tracks SLAs, and handles compliance reporting without constant analyst babysitting.
10. Threat Intelligence Enrichment
Torq enhances threat intelligence by integrating with threat intelligence feeds and security tools to automatically enrich alerts with relevant context. It reduces false positives, accelerates investigations, and empowers SOC teams to act with precision, launching cross-platform searches, syncing with case management, and eliminating manual work.
11. Suspicious User Activity Response
Let Socrates, Torq’s AI Omniagent, take cases involving suspicious user behavior. Whether it’s failed MFA attempts or impossible travel logins, Socrates analyzes the full context, enriches identities, escalates when needed, and even reaches out to users via Slack. Analysts can guide the process or let Socrates handle it entirely. Socrates logs every action so no detail is missed.
12. Secure Access to Sensitive Data
By integrating with IAM and ticketing tools, Torq validates access requests based on role, location, time, and context. It approves or escalates access, logs the session, revokes it when done, and creates compliance-ready audit trails.
Real-World Use Cases: Automation in Action
To understand the true impact of SOC automation, let’s look at real-world scenarios where automation solved critical operational challenges.
Use Case 1: Slashing Phishing Response Time
- Problem: Lennar Corp. was overwhelmed by phishing alerts. Their legacy SOAR tool (XSOAR) had limited integrations and rigid playbooks, forcing their 8-person SOC team to spend “hours and hours” manually investigating suspicious emails.
- Solution: Lennar deployed Torq to Hyperautomate the entire phishing lifecycle. Workflows now autonomously parse emails, analyze attachments in a sandbox, correlate indicators across EDR and threat intel, and execute remediation without human intervention.
- Result: Phishing incident response time dropped from hours to minutes. Analysts were freed from repetitive remediation tasks to focus on proactive threat hunting and research.
Use Case 2: Eliminating Ticket Backlogs with Chatbots
- Problem: A Global Fashion Retailer faced a massive backlog of end-user IT security requests (password resets, access approvals), with resolution times taking up to a week due to unclear tickets and manual processing.
- Solution: The team deployed Torq-powered self-service chatbots directly in Microsoft Teams. Users now interact with a bot to request access or report issues, triggering automated approval workflows in the background.
- Result: Resolution time dropped from one week to 1–2 minutes. The backlog vanished, and the security team automated Just-in-Time (JIT) access for workstations, reducing risk while improving the user experience.
The Torq SOC Automation Advantage
Today’s security teams are overwhelmed by alerts, battling increasingly sophisticated threats, and struggling to scale with limited personnel. The only way to stay ahead is to move faster, work smarter, and offload everything that doesn’t require human creativity or judgment.
Torq enables you to:
- Detect and respond to threats instantly with AI-driven automation
- Reduce analyst burnout through intelligent alert triage and enrichment
- Scale SOC operations efficiently across global, multi-cloud environments
- Maintain full visibility and compliance with automated audit logs
That’s the power of SOC automation. And with platforms like Torq HyperSOC™, it’s not just about doing more with less; it’s about transforming your entire SOC into an autonomous, AI-orchestrated powerhouse.
Your adversaries are using automation. Now it’s your turn to fight smarter.
Kill your SOAR with Torq.
FAQs
An automated SOC uses artificial intelligence and workflow automation to detect, analyze, and respond to cyber threats with minimal human input. Instead of relying on manual processes, an automated SOC connects your SIEM, EDR, IAM, and cloud tools into one unified system that continuously triages alerts, enriches data, and executes response actions at machine speed. The goal is to handle the majority of routine security work autonomously so analysts can focus on complex investigations and strategic decisions.
SOC automation improves speed, consistency, and scalability across security operations. It filters noise to reduce analyst fatigue, accelerates incident detection and response, enforces standardized workflows for compliance, and allows teams to manage more alerts with fewer resources. The result is a stronger, more proactive security posture that scales with your organization.
ROI depends on your current SOC maturity and the platform you choose, but organizations using AI-native Hyperautomation see returns significantly faster than those on legacy SOAR. Valvoline achieved ROI within 48 hours of deploying Torq, cutting six to seven hours of daily analyst triage work immediately. At enterprise scale, Carvana’s agentic AI now handles 100% of Tier-1 and Tier-2 alerts autonomously, giving their team the effective capacity of a SOC five times its size — without adding headcount.
AI SOC automation brings intelligence and adaptability to traditional playbooks. AI models analyze vast telemetry data to identify anomalies and automatically recommend or execute next-step actions. In platforms like Torq HyperSOC™, AI agents such as Socrates coordinate these automated workflows, ensuring every alert is validated, prioritized, and remediated faster and more accurately than manual methods.
The most widely adopted SOC automation use cases are phishing response, alert triage, identity and access management, incident response, and threat intelligence enrichment. Phishing response is often the starting point — Lennar Corp. reduced phishing investigation time from hours to minutes after deploying Torq, and Valvoline cut seven hours of daily phishing triage in their first week. From there, teams typically expand into cloud security posture management, vulnerability management, and suspicious user activity response as automation maturity grows.
With modern AI-native platforms, implementation is measured in days and weeks, not months. Valvoline was live on its top-priority use cases — phishing response and EDR alert handling — within one week of deploying Torq, and a stalled Rapid7 integration that had been blocked for months under their legacy SOAR was delivered in days. Torq’s 90-day roadmap takes organizations from initial deployment to full SOC autonomy, with mature customers reaching approximately 90% automation coverage by day 90. Legacy SOAR platforms, by contrast, typically require 12–18 months before delivering meaningful value.
The three most common hurdles are integration complexity, organizational change management, and defining the right level of autonomy.
Integration complexity is often overestimated. Legacy SOAR platforms earned a reputation for painful, months-long integration projects — but that reflects the limitations of static, code-heavy architectures, not a fundamental challenge with automation itself. Modern Hyperautomation platforms connect to your existing stack through native integrations and AI-generated connectors. RSM migrated 200+ customers to Torq in three weeks; Valvoline replaced a stalled SOAR implementation and was live within a week.
Change management is the real friction point for most teams. Analysts accustomed to manual workflows need to trust that automation will handle cases correctly — and that trust is earned through transparency, not mandates. Platforms that provide full audit trails, explainable AI decisions, and configurable human-in-the-loop controls make this transition easier. Carvana took a deliberate “crawl-walk-run” approach: starting with AI-assisted triage, validating outcomes, and then expanding to full autonomous remediation once the team was confident.
Defining autonomy boundaries — deciding what the platform handles end-to-end versus what gets escalated to a human — requires alignment between SOC leadership, compliance, and the security engineering team. The right answer varies by organization, risk appetite, and regulatory environment. The most effective approach is to start with high-volume, low-complexity use cases (phishing triage, Tier-1 alerts, password resets) where automation delivers immediate, visible value — then expand scope as confidence and coverage data accumulate.