Contents
Get a Personalized Demo
See how Torq harnesses AI in your SOC to detect, prioritize, and respond to threats faster.
TL;DR
- Ransomware encrypts in minutes, not hours. The median encryption time is 42 minutes; the fastest strains finish in under 4 minutes.
- Manual response can’t keep pace. 30% of alerts are never addressed, and 83% of SOC analysts struggle with alert volume (IDC).
- Orchestration closes the gap. Automated workflows can isolate endpoints, disable accounts, and segment networks in seconds, not hours.
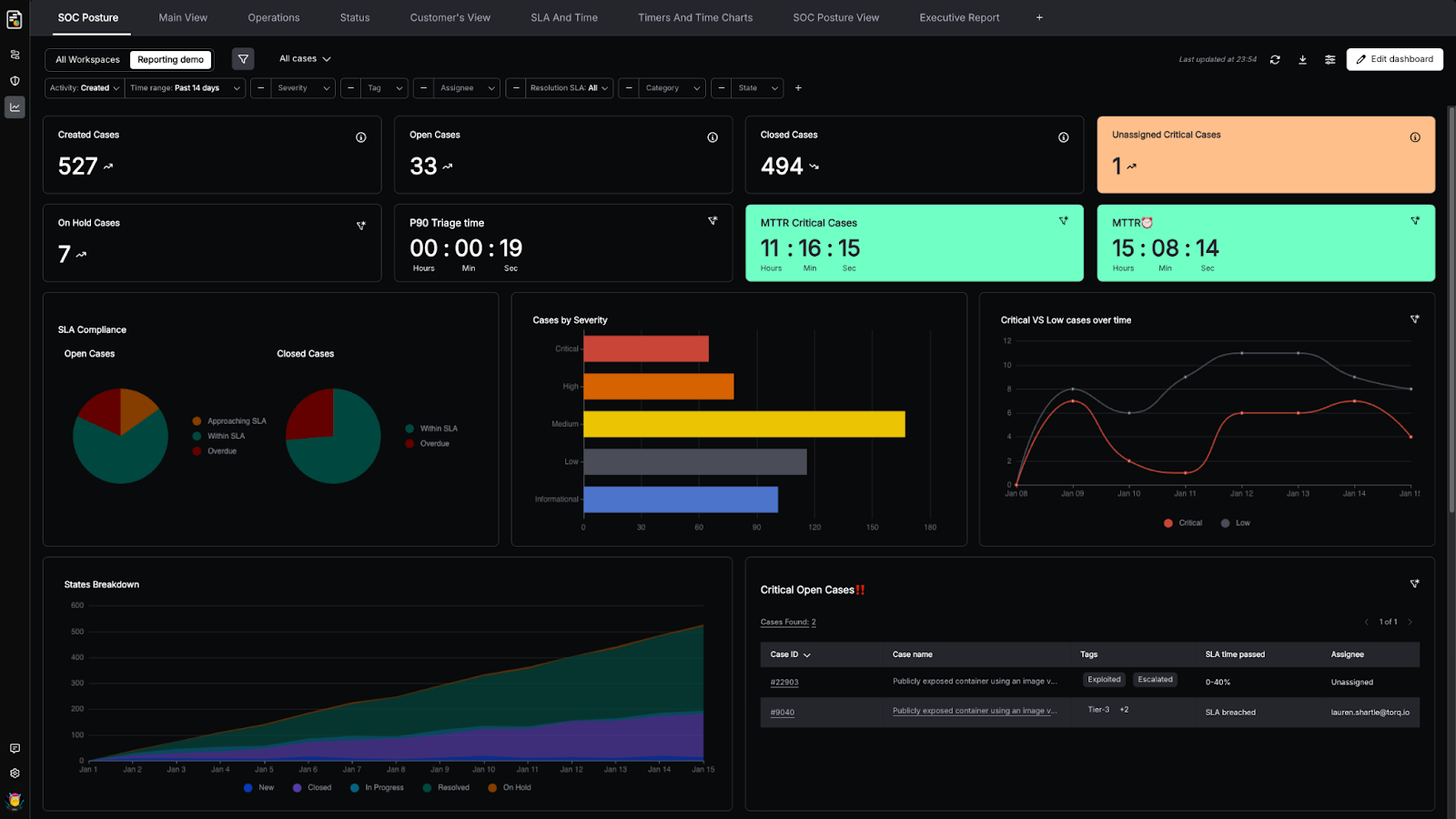
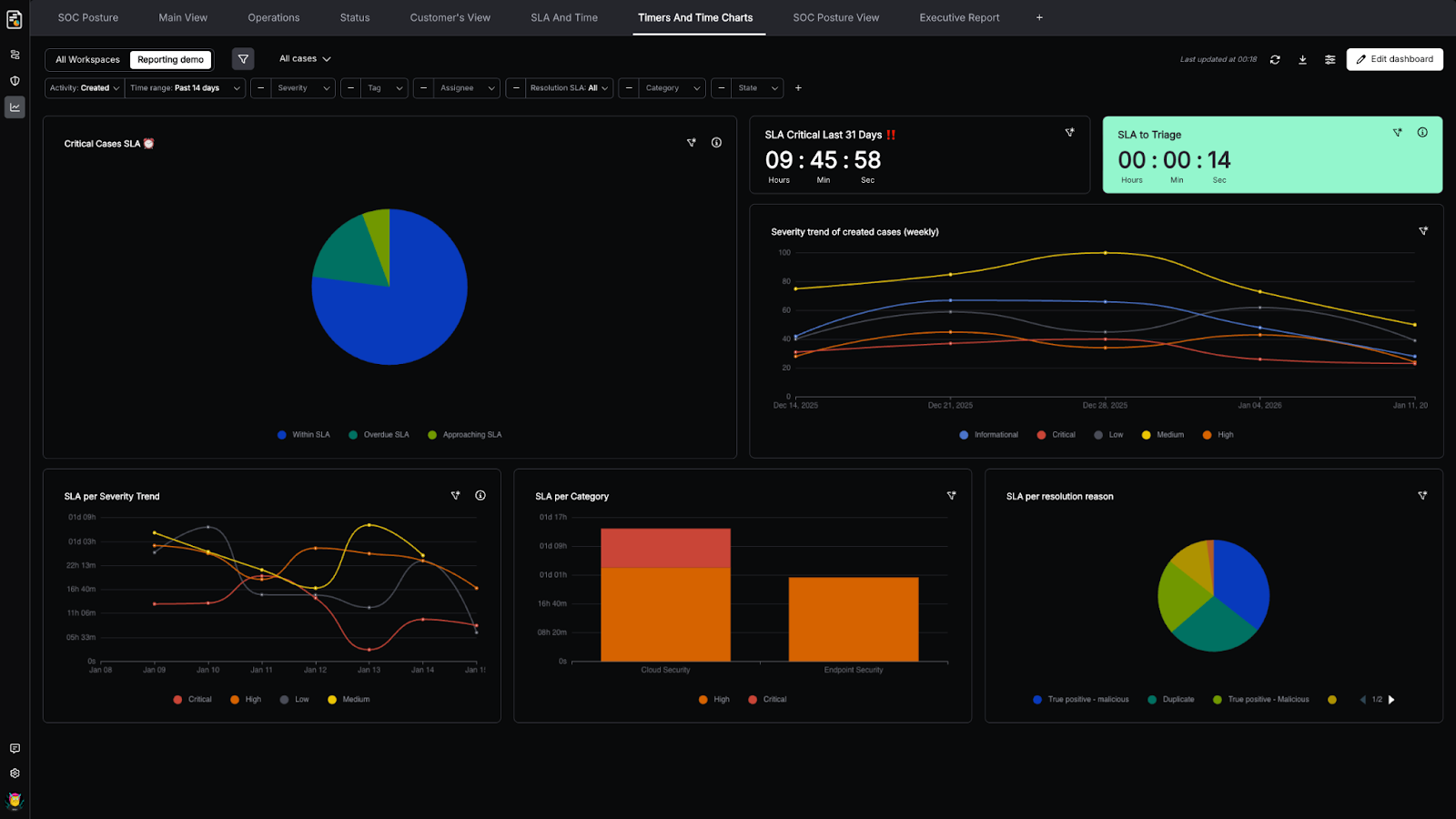
- Speed is the new metric. Mean Time to Contain (MTTC) matters more than detection scores alone.
- Real results: Torq customers achieve up to 95% auto-remediation of Tier-1 cases and cut analyst workload by 7+ hours per day.
Ransomware doesn’t wait for your SOC to finish its morning coffee.
The moment an attacker gains access, the clock starts ticking. Research found that the entire attack chain, from initial access to encryption, now completes in under 30 minutes. Modern ransomware can encrypt nearly 100,000 files before most SOC teams even finish triaging the initial alert.
This timing gap is exactly what attackers exploit. And is exactly why the traditional approach to ransomware protection (prevention checklists, siloed tools, and manual investigation) fails when it matters most.
The enterprises winning the ransomware battle aren’t investing in better detection. They’re rethinking their entire response model through automated security orchestration — replacing reactive scrambling and swivel chairing with autonomous workflows that detect, contain, and remediate threats at machine speed.
Hope isn’t a security strategy. Automation is.
What Is Ransomware Protection and Why Does Manual Response Fall Short?
Ransomware protection is a multilayered security discipline designed to prevent, detect, and respond to ransomware attacks before they encrypt critical data or disrupt operations.
Effective protection spans:
- Email security
- Endpoint detection
- Network monitoring
- Identity management
- Backup verification
- Incident response.
The issue? Most organizations treat these layers as separate silos. Your email security flags a suspicious attachment. Your EDR detects unusual file activity. Your SIEM correlates both events.
But connecting those dots still requires a human analyst to investigate, pivot between tools, and manually execute containment steps. Meanwhile, the ransomware is spreading like wildfire.
Here’s the math that every SOC Director should be aware of: IDC previously reported that 30% of security alerts are never even addressed, while 83% of SOC analysts struggle with alert volume. Add a global cybersecurity workforce gap of 4.8 million professionals — a shortage that grew by 19% in just one year — and you have a perfect storm. Too many alerts, too few analysts, and attackers who move faster than manual processes can keep up.
The window between initial access and encryption is where ransomware attacks succeed or fail. Analysts context-switch between 20+ security tools, manually correlate data, decide on containment actions, and execute them one by one across multiple consoles.
Every minute of delay is a minute ransomware uses to spread laterally, escalate privileges, and encrypt more systems.
However, automation addresses this challenge by collapsing response time from hours to seconds. Automation platforms like Torq Hyperautomation™ connect your entire security stack — EDR, SIEM, identity, network, and backup tools — into unified workflows that execute containment actions the moment indicators are confirmed.
No waiting. No ticket queues. No more “fingers crossed” that an analyst is available.
Preventing Ransomware Attacks With Automated Threat Detection
Prevention still matters. The best ransomware response is the one that never has to execute because the attack was stopped at the door.
Effective ransomware prevention combines three core strategies:
- Automated email security, because phishing remains the primary delivery mechanism. Squish the phish.
- Behavioral analysis to catch threats that evade signature-based detection.
- Continuous vulnerability management to close the gaps that attackers exploit.
The keyword is automated. Prevention at enterprise scale requires continuous monitoring with real-time threat intelligence enrichment across your entire security stack, not periodic scans and manual reviews.
Torq Hyperautomation enables this by connecting prevention tools into workflows that share context automatically. When your email security solution detects a suspicious attachment, Torq Hyperautomation can instantly enrich that indicator with threat intelligence from tools like VirusTotal, Recorded Future, or GreyNoise — then correlate it with signals from your EDR and SIEM to determine if it’s part of a broader attack pattern.
All before a human reviews the alert.
Email Phishing Defense and Behavioral Anomaly Detection
Phishing remains ransomware’s favorite front door. A malicious attachment slips past your email gateway. An employee clicks. And the race against encryption begins.
Automated workflows transform this scenario. Instead of relying on analysts to manually triage suspicious emails, Hyperautomation platforms analyze messages in seconds: extracting IOCs from attachments, detonating files in sandboxes, checking sender reputation, and comparing URLs against known malicious domains.
When indicators confirm a threat, automated containment triggers immediately — quarantining the email, removing it from other inboxes where it may have landed, and alerting the security team. The entire process completes before the employee finishes reading the first paragraph.
Torq Hyperautomation integrates with email security solutions like Abnormal Security and Proofpoint to build these workflows. Lennar, the national homebuilder, reduced phishing remediation from hours to minutes using Torq Hyperautomation for phishing response — freeing analysts to focus on threats that actually require human judgment. Behavioral anomaly detection adds another layer.
Ransomware exhibits predictable patterns:
- Rapid file enumeration
- Mass file modifications
- Shadow copy deletion
- Unusual encryption activity
EDR tools like CrowdStrike and Microsoft Defender detect these behaviors — but detection alone isn’t enough.
Torq Hyperautomation connects behavioral signals from multiple tools to correlate ransomware patterns across your environment. When your EDR detects suspicious encryption activity on one endpoint while your identity tool logs an unusual privilege escalation from the same user, Torq can automatically connect those dots and trigger containment, without waiting for an analyst to investigate.
Learn more about how Torq automates phishing investigation and response.
Stop Ransomware With Automated Response Workflows
Prevention will never be perfect. The question isn’t whether ransomware will breach your perimeter; it’s how fast you can stop it.
This is where automated response workflows become the difference between a contained incident and a crisis.
SOC teams using platforms like Torq build automated workflows that execute the moment indicators are confirmed. The workflow looks something like this:
- Detection: Your SIEM or EDR identifies ransomware indicators, unusual file encryption, known malicious hashes, or behavioral patterns matching ransomware TTPs.
- Enrichment: Torq Hyperautomation automatically enriches the alert with threat intelligence, asset context, and user information. Is this endpoint critical? Is the user a privileged admin? Has this IOC been seen in other ransomware campaigns?
- Containment: Based on enrichment results, Torq executes containment actions across your stack — isolating the endpoint via CrowdStrike or Microsoft Defender, disabling the user account via Okta or Microsoft Entra, and triggering network segmentation via Zscaler or Palo Alto.
- Verification: Torq checks backup status via integrations with Veeam or other backup solutions, confirming recovery options before the situation escalates.
- Notification: Stakeholders receive instant alerts via tools like Slack or Microsoft Teams — complete with AI-generated case summaries that explain what happened and what actions were taken.
This entire sequence executes in seconds.
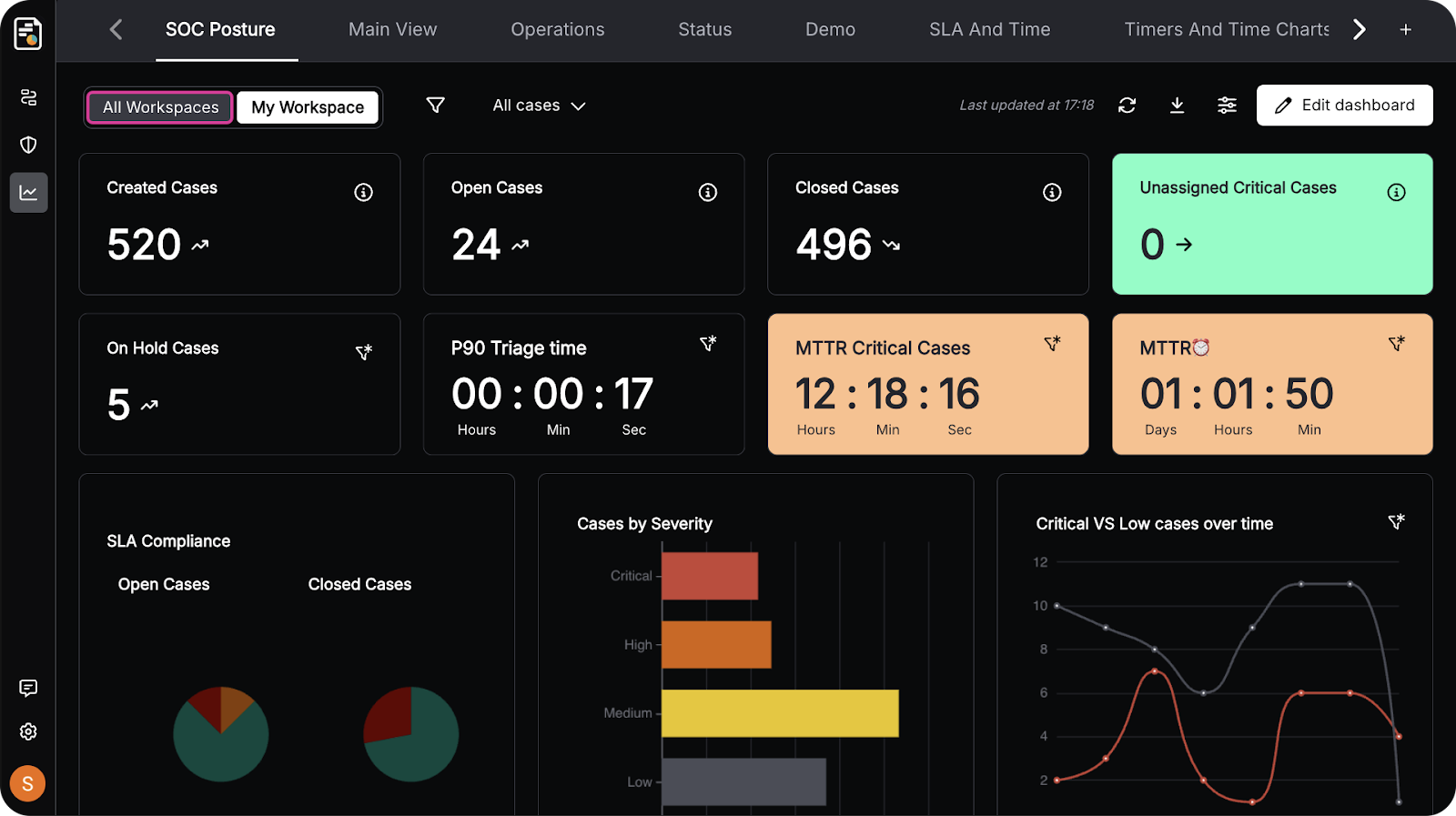
Carvana demonstrated what this looks like at scale: Torq’s agentic AI now handles 100% of their Tier-1 security alerts and automated 41 different runbooks within just one month of deployment. A fundamental transformation of how their SOC operations work.
The orchestrated response model also enables continuous improvement. Every automated workflow generates data on response times, containment effectiveness, and false positive rates.
SOC teams can refine playbooks based on real-world performance, progressively automating more scenarios as confidence grows.
For a deeper look at how automation transforms SOC operations, explore The Multi-Agent System: A New Era for SecOps.
Selecting a Ransomware Solution for Your SOC
Not all Hyperautomation platforms are created equal. When evaluating ransomware protection solutions, SOC Directors should look beyond detection scores and focus on three critical capabilities:
- Integration depth: Your ransomware response workflow is only as strong as its weakest integration. Can the platform connect to your EDR, SIEM, identity provider, network tools, and backup solutions? Torq offers 300+ pre-built integrations with 4,000+ pre-built steps — and AI-powered tools to build custom integrations when needed.
- Workflow flexibility: Ransomware attacks don’t follow scripts. Your response workflows shouldn’t be limited by rigid, pre-built playbooks. Look for platforms that support no-code, low-code, and full-code workflow building — so your team can start with templates and customize based on your environment.
- Autonomous remediation: Detection without response is just expensive alerting. The platform should enable true autonomous remediation — executing containment actions without requiring human approval for well-understood threats. Torq customers like BigID report that “what would normally require 10 security engineers just needs one or two with Torq.”
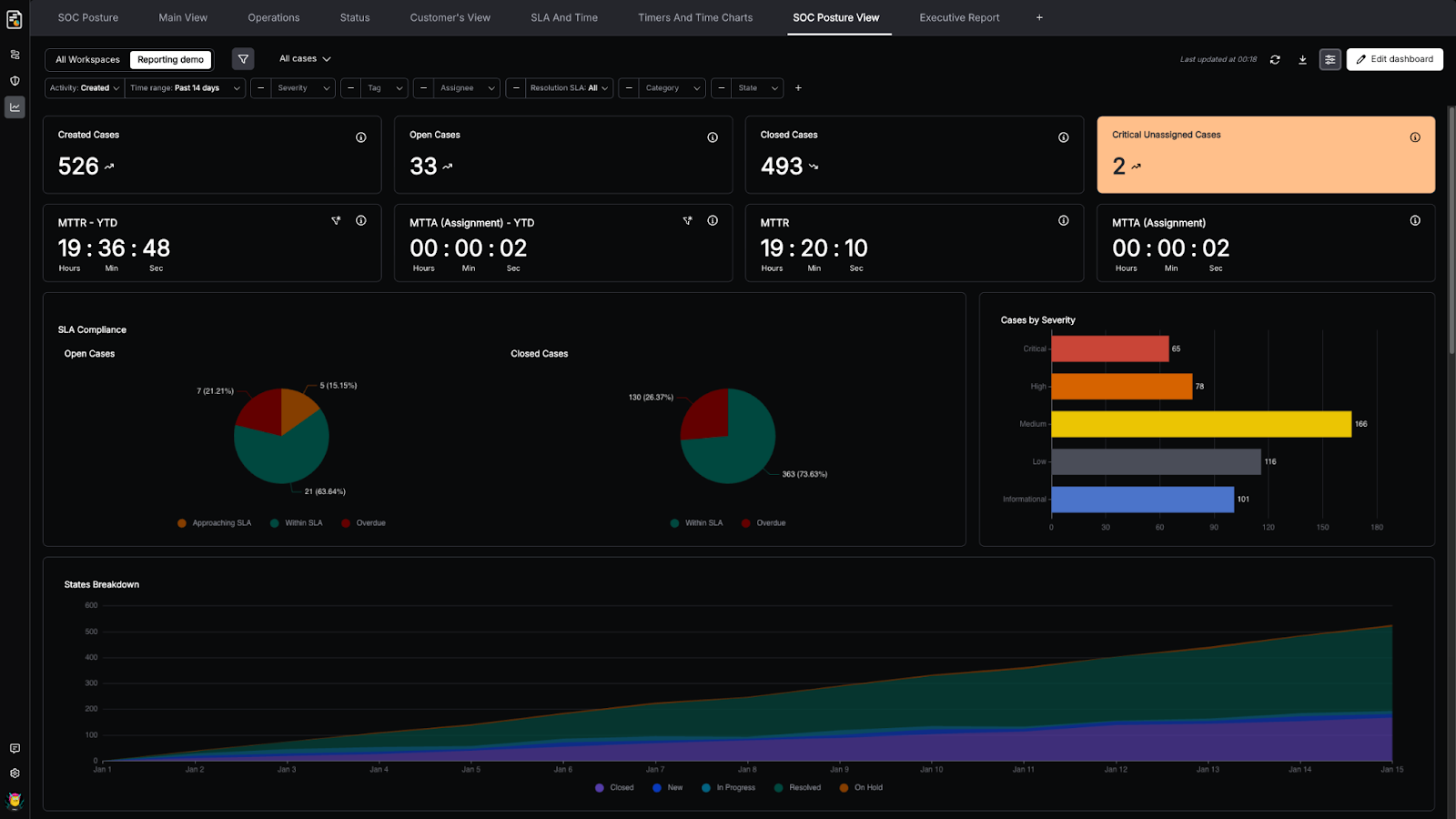
Key metrics to track:
- Mean Time to Contain (MTTC): How fast can you isolate a compromised endpoint? Automated workflows should reduce this from hours to seconds.
- Automation rate: What percentage of Tier-1 alerts are handled without human intervention? Torq customers achieve up to 95% auto-remediation of Tier-1 cases.
- Analyst time saved: Valvoline cut analyst workload by 7 hours per day after implementing Torq. Time that now goes toward threat hunting and security improvement instead of repetitive triage.
Legacy SOAR platforms promised automation but delivered something completely different. Hyperautomation platforms like Torq represent the next evolution, combining AI-powered workflows, agentic reasoning, and deep integrations to enable truly autonomous SOC operations. It’s important to understand why SOAR is dead and what comes next.
Stop Ransomware Before It Stops You
The enterprises successfully defending against ransomware aren’t relying on prevention checklists and manual runbooks. They’re deploying Hyperautomation that detects threats in real time, enriches alerts with contextual intelligence, and executes containment workflows at machine speed.
Torq Hyperautomation and Torq HyperSOC™ give SOC teams the tools to build an autonomous ransomware response — connecting every security tool into unified workflows that stop attacks before encryption completes.
Ready to transform your ransomware protection from reactive to autonomous?
FAQs
Ransomware protection is a multilayered security discipline that prevents, detects, and responds to ransomware attacks before they encrypt critical data or disrupt operations. Effective protection spans email security, endpoint detection and response (EDR), identity management, network monitoring, backup verification, and automated incident response workflows.
The best ransomware protection combines prevention (email security, patching, MFA) with automated response capabilities. Since ransomware can encrypt systems in under 42 minutes, organizations need security automation platforms that can detect, contain, and remediate threats in seconds.
Ransomware detection typically involves EDR solutions (CrowdStrike, Microsoft Defender, Carbon Black), SIEM platforms (Splunk, Microsoft Sentinel), email security tools (Abnormal Security, Proofpoint, Mimecast), and threat intelligence feeds (VirusTotal, Recorded Future). However, detection alone isn’t enough, security automation platforms like Torq connect these tools into automated workflows that respond to threats at machine speed.
Ransomware prevention software includes email security gateways, endpoint protection platforms, vulnerability management tools, and identity security solutions. However, since no prevention is 100% effective, organizations also need Hyperautomation that can execute rapid containment when ransomware is detected, isolating endpoints, disabling compromised accounts, and segmenting networks within seconds.