Contents
Get a Personalized Demo
See how Torq harnesses AI in your SOC to detect, prioritize, and respond to threats faster.
TL;DR
- BOAT (business orchestration and automation technologies) unifies automation tools like RPA, BPA, and iPaaS to coordinate enterprise workflows end-to-end.
- BOAT has delivered real results across finance, HR, IT, and supply chain. The question is whether that same model works for a SOC operating in adversarial conditions, under time pressure, across dozens of security tools.
- General-purpose BOAT platforms lack the security-specific integration depth, threat intelligence context, and adversarial-condition adaptability that SOC workflows demand.
- The Torq AI SOC Platform combines security Hyperautomation and agentic AI to investigate, enrich, and resolve threats autonomously — at machine speed.
Business automation has transformed enterprise operations. Finance teams close books faster. HR teams onboard employees without touching a spreadsheet. Supply chains self-correct in real time. Across the enterprise, automation is delivering on its promise.
So why is the security operations center (SOC) still drowning?
The answer isn’t a lack of automation. Most SOCs have plenty of it. The problem is that automation without orchestration is just a collection of isolated tasks — and isolated tasks don’t stop threats. Business orchestration and automation technologies (BOAT) offer a more generic answer for the enterprise at large, but the SOC isn’t the enterprise at large. It’s a fundamentally different operating environment — adversarial, time-critical, and deeply tool-fragmented.
This article evaluates whether BOAT can handle security operations, where it falls short, and what SOC teams actually need instead.
What Are Business Orchestration and Automation Technologies?
Business orchestration and automation technologies (BOAT) is a Gartner-defined category of consolidated software platforms that deliver enterprise process automation through orchestration of business processes, enterprise connectivity, low-code development, and agentic automation.
BOAT platforms typically bring together several underlying technologies under one roof, including robotic process automation (RPA), business process automation (BPA), integration platform as a service (iPaaS), and workflow management tools. The goal is a single, coherent layer that manages complexity across the enterprise — not just one corner of it.
In a hybrid, multi-cloud enterprise environment, that kind of coordination is no longer optional. Fragmented systems mean fragmented visibility. Manual handoffs mean slower outcomes. BOAT addresses both by creating a connected operational fabric.
For security teams, that framing is instructive. But the SOC stress-tests it in ways the rest of the enterprise doesn’t.
What Is the Difference Between Automation and Orchestration?
The terms “automation” and “orchestration” are often used interchangeably. They shouldn’t be.
Automation is the execution of a specific, repeatable task without human intervention. Blocking an IP address. Sending an alert notification. Pulling a log file. These are valuable actions, but they are inherently narrow. They don’t know what happened before the task or what needs to happen after it.
Orchestration is the coordination of multiple automated tasks and tools into a cohesive, end-to-end workflow. It’s the intelligence layer that decides what runs, when, in what order, and based on what conditions. Orchestration takes inputs from across your environment, routes them through the right tools, and produces outcomes — not just outputs.
In a security context, blocking an IP is automation. Detecting a suspicious login, pulling threat intel, cross-referencing identity data, notifying the analyst, containing the endpoint, and closing the ticket are all part of orchestration. One is a step. The other is a resolved incident.
Security operations live and die by orchestration. The threats are too dynamic and the workflows too complex for task automation alone to carry the load. This is also why IT operations teams in adjacent environments increasingly need the same end-to-end thinking, but the adversarial nature of security makes the requirement more urgent.
Where Does BOAT Work Well — and Where Does It Break Down?
Process automation technologies have delivered real efficiency gains across the enterprise. In finance, automated invoice processing eliminates manual data entry. In legal, contract review workflows auto-route documents based on risk tier. In IT operations, ticketing systems auto-assign and escalate based on SLA thresholds.
These are legitimate wins. But notice what they have in common: they operate in relatively stable, well-defined environments with predictable inputs and outputs.
Security operations are not in that environment.
A phishing campaign can arrive in dozens of variants. A cloud misconfiguration surfaces differently across providers. An insider threat doesn’t follow a playbook. When process automation tools encounter edge cases, novel attack patterns, or logic that wasn’t anticipated at build time, they stall. They require human intervention. And in a SOC, human intervention at scale is exactly what you were trying to avoid.
Process automation is a necessary foundation. But without orchestration layered on top — and without the intelligence to adapt — it can’t carry the full weight of security operations.
Why Can’t General-Purpose BOAT Platforms Handle the SOC?
This is the central question, and the answer comes down to four structural gaps.
Gartner’s evolving BOAT definition now includes agentic automation as a core capability — a recognition that the market is moving toward AI that can reason and act, not just execute scripts. But there’s a critical distinction between agentic automation built for business processes (approving purchase orders, routing support tickets) and agentic AI built for adversarial environments (investigating a credential compromise across your SIEM, EDR, and IAM stack in real time while an attacker moves laterally).
General-purpose BOAT platforms weren’t designed for the second scenario. Here’s where the gaps show up.
Tool silos kill context. Most SOCs rely on dozens of security tools, including SIEMs, EDRs, threat intelligence platforms, identity systems, cloud security tools, ticketing platforms, and more. BOAT automation that operates within individual tools can’t easily pass security-specific context between them. Analysts end up pivoting between consoles, manually connecting dots that a security-native platform would connect automatically.
Alert volume outpaces what BOAT was designed to handle. According to IBM’s 2025 Cost of a Data Breach Report, organizations that do not use AI and automation extensively average $5.52 million per breach — compared to $3.62 million for those that do. SOC alert volumes are measured in thousands per day. BOAT platforms built for invoice processing and HR workflows weren’t architected for that velocity, and when critical signals get buried, response slows, and breach costs climb.
MTTR requires end-to-end security orchestration. Mean time to respond (MTTR) is the KPI that matters most in security operations. Every minute between detection and containment is an attacker spending time in your environment. Task-level automation — even well-orchestrated task-level automation — doesn’t meaningfully compress MTTR, because MTTR isn’t about individual tasks. It’s about the full detection-to-resolution workflow running without friction, and that workflow needs security-specific logic at every step.
Manual intervention creates compliance exposure. When automation gaps require analysts to step in and complete processes by hand, you introduce human variability into workflows that should be deterministic. Two analysts handling the same alert type may triage, escalate, and document differently. In a SOC, that inconsistency is a compliance problem as much as an efficiency problem — and BOAT platforms don’t have the security-specific guardrails to prevent it.
What Does the SOC Actually Need Instead?
General-purpose BOAT platforms can connect systems and automate tasks. What they can’t do is handle the full complexity of a SOC environment — across dozens of tools, thousands of daily alerts, and workflows that must adapt in real time to evolving threat conditions.
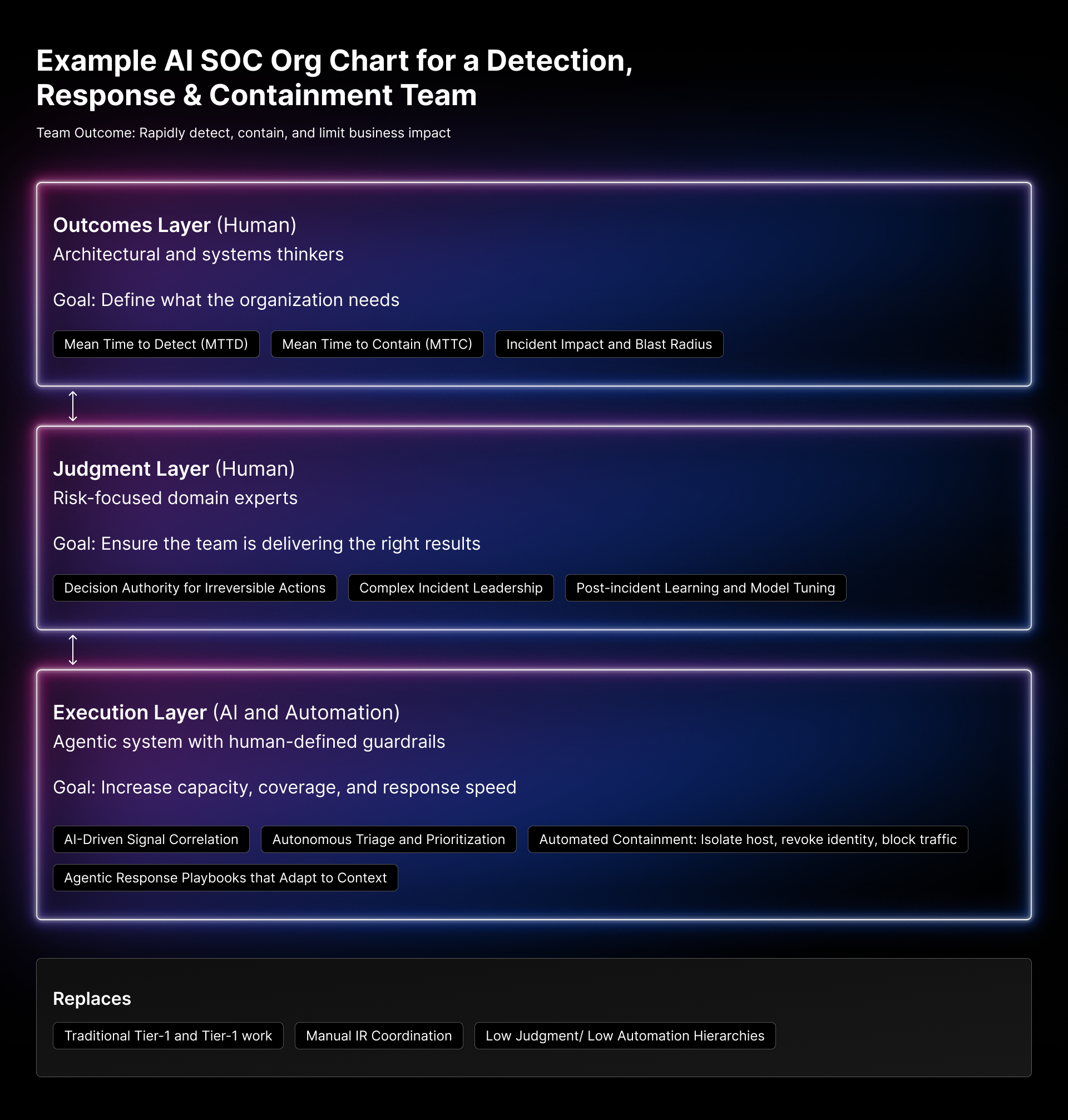
Security automation and orchestration in a SOC is different. A modern SOC framework powered by security Hyperautomation doesn’t just pass data between tools. It applies logic, context, and prioritization to every step of the workflow, so the right action happens at the right time with the right level of analyst involvement.
That means fewer manual handoffs. Faster triage. Consistent, auditable response workflows that hold up to compliance scrutiny. And security teams that spend their time on meaningful investigation instead of repetitive tasks.
The integration flexibility matters just as much. A platform built for security connects to your existing tools without requiring you to rip and replace — and it scales as your environment grows without accumulating technical debt. For organizations managing multi-SIEM strategies or navigating complex compliance requirements under established cybersecurity frameworks, that flexibility is critical.
How Does Agentic AI Close the Gap BOAT Leaves Open?
Security Hyperautomation is powerful. Pair it with agentic AI, and the SOC starts operating at a fundamentally different level from anything general-purpose BOAT can deliver.
Agentic AI systems don’t execute predefined playbooks and stop there. They reason through problems, gather context autonomously, evaluate options, and take action within defined guardrails — without requiring an analyst to drive every step. Alerts don’t sit in a queue waiting for a human to start the triage process. They get investigated, enriched, and in many cases resolved before an analyst ever opens a console.
Torq Socrates is the agentic AI SOC Analyst inside the Torq AI SOC Platform. It triages, investigates, and resolves alerts — pulling context from across the security stack, applying threat intelligence, and making disposition decisions that would otherwise require analyst hours. It doesn’t eliminate the analyst. It eliminates the work that shouldn’t require one.
The result is measurable: higher autonomous resolution rates, compressed MTTR, and analysts focused on the cases that genuinely need human judgment.
This is the gap BOAT can’t close in the SOC. General-purpose agentic automation can route a support ticket. Security-specific agentic AI can investigate a credential compromise, correlate it with lateral movement across your cloud environment, contain the affected endpoint, and document the entire case… autonomously, in minutes.
What Does This Look Like in Practice? Automated Phishing Response
Here’s what an automated phishing response looks like inside the Torq AI SOC Platform, from first signal to full resolution, and why general-purpose BOAT workflows can’t replicate it.
- A user reports a suspicious email. The platform ingests the report and immediately begins enrichment — pulling the sender domain, URLs, and attachments into threat intelligence tools.
- Simultaneously, the platform queries the email gateway to identify whether the same message was delivered to other users.
- URL and file reputation checks run in parallel. If indicators of compromise are confirmed, the platform automatically quarantines the email across all affected inboxes.
- The user’s endpoint is checked for any signs of interaction — clicks, downloads, or execution. If the endpoint shows activity, containment actions trigger automatically.
- A case is opened, all investigation steps are documented automatically, and the analyst receives a complete summary with recommended next steps — rather than a raw alert that requires them to start from scratch.
- If no compromise is found, the case closes automatically. If escalation is warranted, it routes to the right analyst with full context already assembled.
What used to take an analyst 45 minutes of manual investigation runs autonomously in minutes. A general-purpose BOAT platform could automate individual steps in this chain. What it can’t do is orchestrate the security-specific reasoning, threat intelligence enrichment, cross-tool correlation, and autonomous containment decisions that make the workflow actually work.
How Does the Torq AI SOC Platform Go Beyond BOAT?
General-purpose BOAT platforms solve enterprise process problems. The Torq AI SOC Platform solves security operations problems — and the distinction matters.
Torq was purpose-built for the SOC, which means every architectural decision reflects the realities of security Hyperautomation: high-velocity alert environments, adversarial threat conditions, deep tool sprawl, and response timelines measured in minutes, not days.
What that looks like in practice:
No-code workflow customization. Security teams can build, modify, and deploy complex orchestration workflows without writing code. That means faster time to value and no engineering dependency for every new use case.
4,000+ OOTB integrations and actions. The Torq AI SOC Platform connects natively to the tools already in your stack — SIEM, EDR, identity, cloud, ticketing, threat intel, and beyond — giving AI agents the tools they need to act autonomously. Connectivity is out of the box, not a project.
Torq HyperAgents™ and agentic AI. The multi-agent system that powers autonomous investigation, enrichment, and resolution at scale. It goes beyond playbook execution to handle complex, multi-step workflows with reasoning and adaptability — the kind of agentic capability that general-purpose BOAT platforms don’t have the security context to deliver.
Enterprise-ready architecture. Torq is built for the scale and compliance requirements of Fortune 500 environments — with role-based access controls, full audit logging, and the reliability enterprises demand. The Torq Series D funding reflects the confidence the market has placed in that enterprise-grade approach.
Fast time to value. Teams are automating use cases within days, not months. The platform is designed for adoption, not just capability.
For MSSPs looking to move beyond legacy SOAR, and for enterprise SOC teams building for the future, the Torq AI SOC Platform transforms automation investment into measurable security outcomes.
The SOC Needs More Than BOAT
Business orchestration and automation technologies represent a genuine evolution in how enterprises manage complexity. BOAT platforms are doing important work across finance, HR, IT operations, and supply chain.
But security operations demand more than general-purpose BOAT can offer. The threats are too dynamic, the tool environments too complex, and the stakes too high. General-purpose BOAT can’t close that gap — no matter how much agentic automation Gartner adds to the definition.
Security-specific orchestration — backed by agentic AI and Hyperautomation — is what turns dozens of automation tools into a coordinated defense. It compresses MTTR from hours to minutes, reduces manual analyst workload, and gives security teams the ability to scale without scaling headcount.
The Torq AI SOC Platform was built for exactly this. Get the Don’t Die, Get Torq manifesto to learn more.
FAQs
Business orchestration and automation technologies (BOAT) is a Gartner-defined category of consolidated software platforms that deliver enterprise process automation through orchestration of business processes, enterprise connectivity, low-code development, and agentic automation. BOAT platforms unify tools like RPA, BPA, LCAP, and iPaaS into a single system for managing workflows across departments and data sources, replacing fragmented manual processes with connected, automated operations.
Automation handles individual, repeatable tasks without human intervention — blocking an IP address, sending a notification, or pulling a log file. Orchestration coordinates multiple automated tasks and tools into a complete, end-to-end workflow. In a security context, automation is a single step. Orchestration is a fully resolved incident — from detection through investigation, containment, and closure.
BOAT software refers to platforms in Gartner’s business orchestration and automation technologies category. These tools combine automation capabilities like RPA and BPA with workflow orchestration, low-code development, and integration features, giving enterprises a unified layer for managing complex, multi-system processes. While effective for general enterprise operations, security teams typically require platforms built for adversarial inputs, dynamic threat conditions, and real-time response requirements that general-purpose BOAT tools weren’t designed for.
General-purpose BOAT platforms can automate individual steps in security workflows, but they lack the security-specific integration depth, threat intelligence context, and adversarial-condition adaptability that SOC operations demand. SOCs face thousands of daily alerts across dozens of specialized tools, with response timelines measured in minutes and inputs that are actively adversarial. This is why security teams need purpose-built platforms that combine security Hyperautomation with agentic AI — not general-purpose enterprise automation extended into the SOC.
Yes. Gartner’s updated BOAT definition includes agentic automation as a core capability. However, agentic automation built for general business processes (routing approvals, managing workflows) operates in fundamentally different conditions from agentic AI built for security operations — where adversarial inputs, real-time threat response, and cross-stack investigation depth are requirements. This distinction is why security teams need purpose-built platforms even as BOAT evolves.
Agentic AI goes beyond executing predefined playbooks or routing business processes. In a SOC environment, it reasons through problems, gathers context autonomously from across SIEM, EDR, IAM, and cloud tools, evaluates options, and takes action within defined guardrails — without requiring an analyst to drive every step. The result is alerts triaged, investigated, and resolved autonomously, with faster response times, higher resolution rates, and analysts focused on work that genuinely requires human judgment. General-purpose BOAT platforms don’t have the security-specific context to deliver this.