TL;DR
- Modern security failures are caused by tool sprawl, gaps between platforms, and the manual effort required to bridge those gaps.
- The five essential elements of security in 2026 are: unified visibility, AI-driven execution at speed, built-in AI governance, structured case management, and continuous measurement.
- According to the 2026 AI SOC Leadership Report, 80% of security teams still rely on fragmented point solutions, even though 85% say they’d prefer consolidation.
- Structure without speed creates backlogs. The teams winning in 2026 have both.
- Security in 2026 is an operational discipline — and the teams winning are the ones investing in AI-driven execution, not just adding more tools.
Why “Security” Looks Different in 2026
Ask most security leaders what keeps them up at night, and they’ll probably mention something about alert volume, talent gaps, or the evolution and speed of attacks. What they’re less likely to say — but should — is this: the biggest security failures aren’t happening because organizations lack tools. They’re happening in the gaps between them.
The modern enterprise security environment is genuinely complex. Hybrid infrastructure, multi-cloud deployments, sprawling SaaS ecosystems, third-party APIs — the attack surface has expanded dramatically, and it’s not shrinking. But the response to that complexity has mostly been to add more tools on top of existing tools. The result? An average SOC runs more than a dozen separate platforms, and most of them don’t natively communicate with each other.
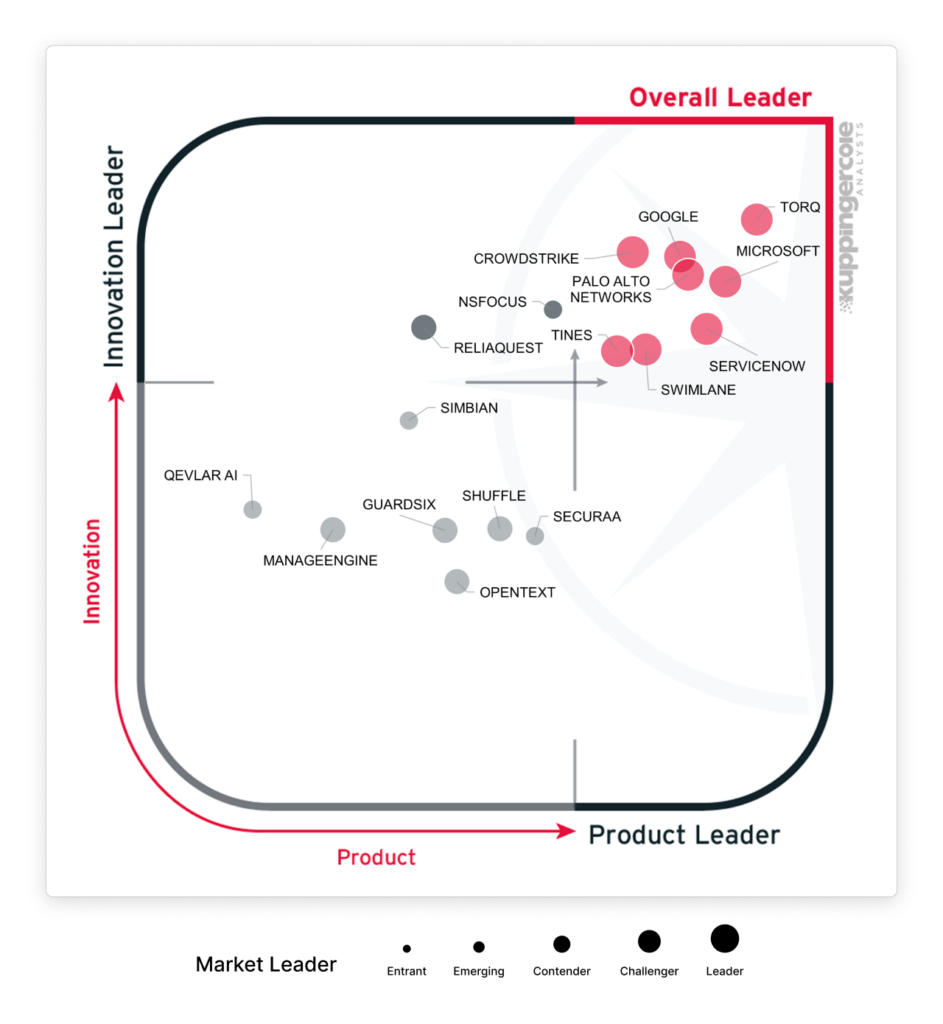
According to the 2026 AI SOC Leadership Report, the average security team is running 7 AI-powered tools alone, and 80% still depend on fragmented point solutions rather than a unified platform. AI is everywhere. Integration is not. That’s the defining security essentials 2026 challenge. Not a shortage of technology but a shortage of execution.
This guide breaks down the five essential elements every modern security program needs to operationalize this year.
1. Unified Visibility Across the Security Stack
Let’s start with the most foundational element, and the one that’s most frequently misunderstood.
Visibility doesn’t just mean having a single pane of glass. And it doesn’t mean consolidating all your data into one SIEM and calling it done. True visibility in 2026 means the ability to see and act on signals across your entire environment — endpoint, identity, cloud, SaaS, network — without those signals living in isolated silos that require manual correlation to be useful.
Here’s why this matters so much right now: modern attacks don’t respect tool boundaries. A threat actor compromises a credential in your identity provider, moves laterally through a cloud environment, and exfiltrates data via a SaaS application. Each of those steps might generate an alert in a different system. If your analysts have to manually connect those dots across three or four separate consoles, the response will be slow — and in security, slow is expensive.
The problem isn’t that organizations lack data. It’s that the data lives in disconnected places, and pulling it together takes time and manual effort that most teams simply don’t have. As Torq’s Field CISO John White writes, the CISO’s job is increasingly about designing human-machine teams that can act on intelligence at the speed the threat environment demands.
Visibility also has to extend across the full security lifecycle. Detection is only one part of it. You need to see what’s happening during investigation, during response, and during post-incident review. If any of those stages is a black box, you can’t improve them.
What operationalizing this actually looks like:
- Connecting signals from SIEM tools, EDR tools, identity, cloud security, and SaaS tools into unified workflows that can trigger responses automatically
- Ensuring that context follows a case from detection through resolution
- Making visibility actionable, not just informational
The Torq AI SOC Platform is built around this premise: it connects to your existing tools and surfaces cross-stack context so your team can see the full picture and respond without toggling between platforms.
2. AI-Driven Execution at Machine Speed — Without Losing Control
Here’s an issue every security leader is navigating right now: the volume and velocity of threats have outpaced human response capacity, but fully autonomous AI makes many teams nervous. Both of those things are true at the same time. And both of them are valid.
Torq Field CISO John White frames it this way in his piece on AI governance in the SOC: the decisions that require human authority are the ones that demand business context — risk appetite, the political environment you’re operating in, the company’s financial situation, and the strategic direction the board is pursuing. That’s the judgment layer. And it’s not an arbitrary line.
The answer isn’t to pick a side. It’s to get smarter about where automation should run fully, where it should support human decision-making, and where humans should always be in the loop.
According to the 2026 AI SOC Leadership Report, 72% of security teams are already comfortable with fully autonomous AI handling incidents of medium severity or lower.
That’s the bulk of SOC volume. The repetitive, high-frequency alerts used to consume hours of analyst time every day. Teams aren’t debating whether to automate that work. They’re figuring out how to do it reliably.
The nuance is in what comes next. Nine in 10 security leaders say they need explainability — the ability to see how AI reached a decision — before they’ll extend autonomy to more complex cases. That’s not AI skepticism. That’s reasonable governance. You wouldn’t sign off on a major business decision without understanding the reasoning behind it.
Security decisions are no different.
The operational takeaway: speed and structure aren’t opposites. The best security automation executes at machine speed on tasks that don’t require human judgment, while surfacing the right context at the right moment for decisions that do. Ad hoc scripts and brittle runbooks can’t do that. AI-driven workflows can.
Torq Hyperautomation™ is designed exactly for this: consistent, auditable execution across your stack, with human oversight built in rather than bolted on. And Torq AI Agents go further — they don’t just plan and reason, they act. They investigate cases, enrich context, and remediate issues across your environment, while your team stays in control of the decisions that matter most.
3. Built-In Governance and Guardrails
Automation without oversight isn’t a security program. It’s a liability.
John White puts it plainly: if AI makes the wrong call and a breach happens, accountability lands with the CISO — not the vendor, not the board. That accountability doesn’t transfer. It sits with you.
Which makes governance not a nice-to-have, but a leadership imperative. And yet it’s genuinely underbuilt in most organizations. Governance in security has traditionally been treated as a compliance function, or something you do before an audit, not something that runs in the background of every security operation, every day. That model doesn’t work when your response workflows are executing hundreds of actions per hour.
The compliance landscape isn’t getting simpler, either. Regulatory requirements continue to expand across industries and geographies. Audit trail requirements are more stringent. Boards want visibility into security operations that most teams aren’t set up to provide. And the consequences of an undocumented, undiscovered automated action taking the wrong step are significant — both operationally and from a liability perspective.
What built-in governance actually means in practice:
- Approval workflows for actions that cross a defined risk threshold, so humans are in the loop on high-stakes decisions without becoming bottlenecks on everything
- Role-based access controls that define who can modify, trigger, or approve which types of actions
- Auditable execution logs that capture not just what happened, but why — what conditions triggered the workflow, what data was used to make the decision, what action was taken, and who reviewed it
This is especially critical as AI agents take on more investigative and response work. The CISO’s role is evolving toward strategic oversight — which means the systems performing operational work need to provide the visibility and accountability that strategic oversight requires.
Governance isn’t a constraint on speed. Done right, it’s what makes speed sustainable.
4. Structured Case and Incident Management
Many organizations don’t have a consistent, structured way to manage security work from detection through resolution. Alerts get triaged. Incidents get worked. But the thread connecting detection to investigation to remediation to post-incident review is loose, manual, and inconsistent.
That’s a problem for a few reasons.
First, it makes it nearly impossible to audit what actually happened during an incident. If the investigation steps aren’t captured in a structured way, reconstructing them after the fact is painful and imprecise — which matters a lot when you’re dealing with regulatory requirements, insurance claims, or executive reporting.
Second, it creates analyst burnout. Without structure, every incident becomes a custom, ad hoc effort. Analysts are reinventing the same processes over and over, context is lost between shifts, and the cognitive load of keeping everything in your head — or in a sprawling Slack thread — is exhausting. Alert fatigue is real, and unstructured case management makes it worse.
Third, it makes improvement nearly impossible. You can’t optimize a process you can’t measure. If you don’t know how long the average investigation takes, where handoffs break down, or which types of incidents consume the most analyst time, you’re flying blind on where to invest.
Torq’s Case Management is built to solve this directly — intelligent case automation and prioritization that gives every security event a predictable lifecycle. Cases are automatically created, enriched, and routed based on incoming signals. AI agents contribute investigation steps and context. Analysts review, decide, and close. The entire thread is captured and auditable.
The principle here is simple: every meaningful security event should follow a structured, repeatable process. Not because process is the goal, but because process is what makes improvement possible.
5. Measurement and Continuous Improvement
If you can’t measure it, you can’t manage it. And if you can’t manage it, you definitely can’t improve it.
This is one of the most consistently underinvested areas in security operations. Most teams have dashboards. Far fewer have metrics that actually tell them whether the program is getting better.
The distinction matters. Alert counts, open ticket totals, and MTTD are popular metrics because they’re easy to measure — not because they’re necessarily the most meaningful. What leaders actually need to understand is whether their security operations are becoming more effective over time: Are we resolving the same types of incidents faster than we were six months ago? Are automated workflows handling a higher percentage of cases without human intervention? Are analysts spending more time on complex investigations and less time on repetitive triage?
According to the 2026 AI SOC Leadership Report, analysts are already spending an average of 8.6 hours per week overseeing AI outputs. That number isn’t inherently good or bad — it depends entirely on whether that oversight is generating better outcomes and shrinking over time as trust in AI execution increases.
Security maturity is not static. Teams that treat their current operating model as the destination rather than a point on a continuum will fall behind. The ones that measure relentlessly, invest in the right areas, and continuously refine their workflows are the ones building programs that scale.
This means building reporting into your workflows from the start, not as an afterthought. It means tracking metrics that reflect execution and outcomes — case closure rates, automation coverage, time to containment. And it means creating a feedback loop where what you learn from incidents drives changes to how you respond to the next ones.
The 5-Point Security Essentials 2026 Checklist
Use this as a quick gut-check on where your program stands:
- Do we have connected visibility across all critical security tools, with context that flows between them?
- Can we execute response actions consistently and at speed, without relying on manual effort for every step?
- Are governance, approvals, and access controls built into our workflows — not reviewed after the fact?
- Do we track security incidents in a structured, auditable way from detection through resolution?
- Can we measure what’s working, what isn’t, and where to improve — with data, not just instinct?
If the honest answer to any of those is “not really,” that’s where to start.
Security in 2026 is an Operational Discipline
This is the most important reframe for security leaders right now: security success in 2026 is not defined by the number of tools in your stack. It’s defined by how well you can execute across that stack — consistently, quickly, and with the governance and measurement to know it’s working.
The organizations pulling ahead are doing it because they’ve built security programs that can actually operate at the speed and scale the threat environment demands. They’ve invested in AI-driven automation that executes reliably. They’ve structured their case management so nothing falls through the cracks. They’ve built governance in, not bolted it on. And they measure everything.
That’s the autonomous SOC.
Torq is the AI SOC platform purpose-built to help security teams operationalize all five of these security essentials across their existing tools and workflows — without ripping and replacing what’s already working. With Torq Hyperautomation™, AI Agents, and Case Management working together, security teams can close over 95% of security cases autonomously, at machine speed, with full audit-ability.
Ready to see how your program stacks up?
FAQs
What are the five essential elements of security in 2026?
The five elements are: (1) unified visibility across your security stack, (2) AI-driven execution at machine speed with human oversight where it matters, (3) built-in governance and guardrails, (4) structured case and incident management, and (5) continuous measurement and improvement. Together, these elements define what it looks like to run security operations effectively in an environment defined by complexity, speed, and scale.
Why do security programs fail despite having many tools?
Tool sprawl is one of the biggest and most underacknowledged security risks in enterprise organizations. According to the 2026 AI SOC Leadership Report, 80% of security teams still depend on fragmented point solutions, even as they add more AI-powered tools to the stack. The failures happen in the gaps between tools: in manual correlation, inconsistent response processes, and the lack of a unified workflow connecting detection to resolution.
How can security teams improve operations without replacing their entire stack?
Start by identifying where execution breaks down, not where coverage is lacking. Most teams have adequate detection capability. The breakdowns happen during investigation, triage, and response — where manual steps, inconsistent processes, and tool-switching slow everything down. AI-driven automation and structured case management can layer on top of your existing stack to close those gaps without a full rip-and-replace. Learn more about how the Torq AI SOC Platform works with your existing tools.
What should security leaders actually be measuring in 2026?
Move beyond just alert counts and MTTD. The metrics that matter are the ones that reflect execution and outcomes: automation coverage (what percentage of cases are handled without manual intervention), time to containment, case closure rates by category, and analyst time spent on complex vs. repetitive work.