Contents
Get a Personalized Demo
See how Torq harnesses AI in your SOC to detect, prioritize, and respond to threats faster.
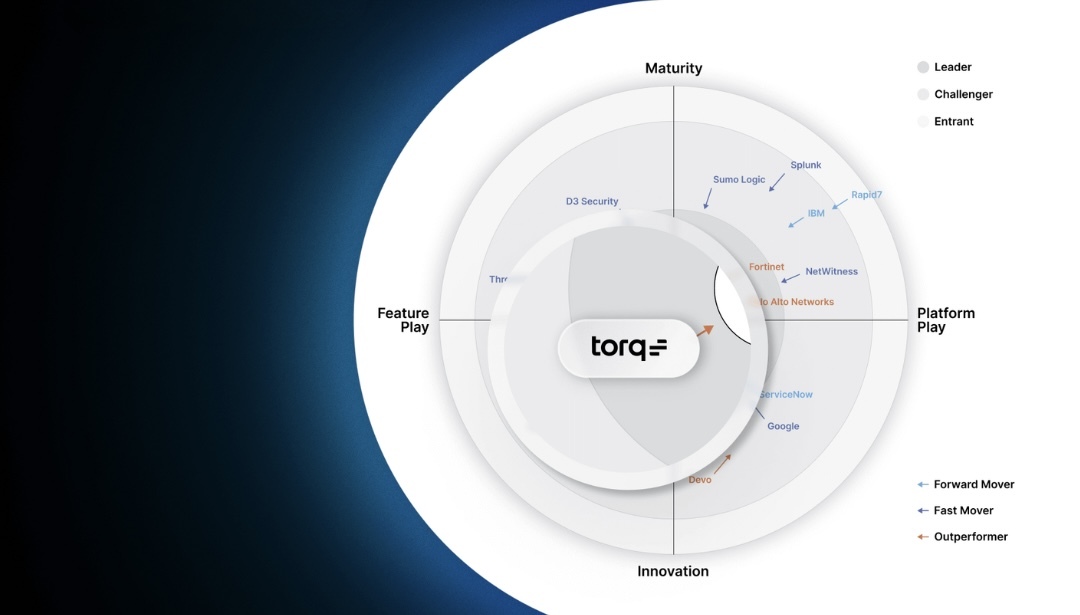
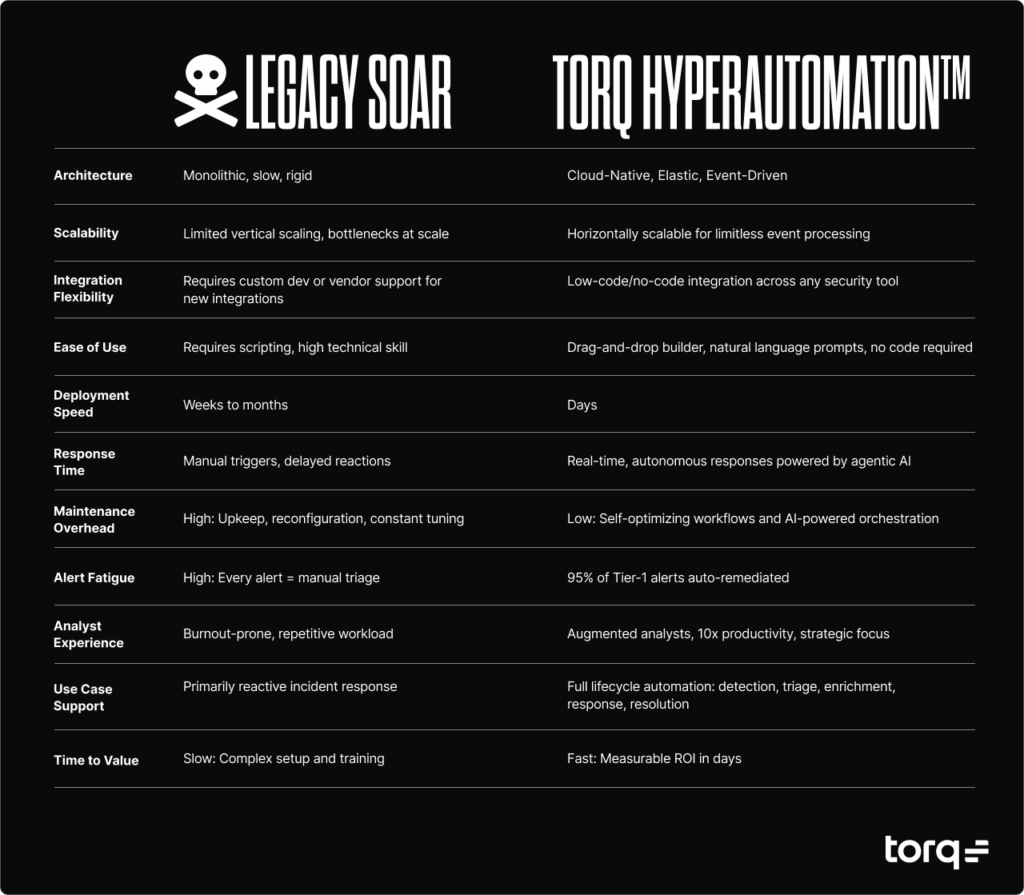
SOAR is dead-dead (too inflexible, too complex, and too limited on integrations) — but it’s not quite buried in some SOCs where it’s only hanging on because migrating can feel daunting when mission-critical workflows are tied to the system.
AI-driven Hyperautomation from Torq is the SOAR killer, and our team has helped major enterprises from every industry make the switch, quickly and easily.
We chatted with Mark Carosella, Sr. Sales Engineer at Torq, to hear firsthand what surprises new Torq customers the most when they pull the plug on their SOAR and learn what it is about Torq that makes migrating from legacy SOAR not just fast, but also transformative.
Why Legacy SOAR Platforms Fall Short and How to Transform Your SOC
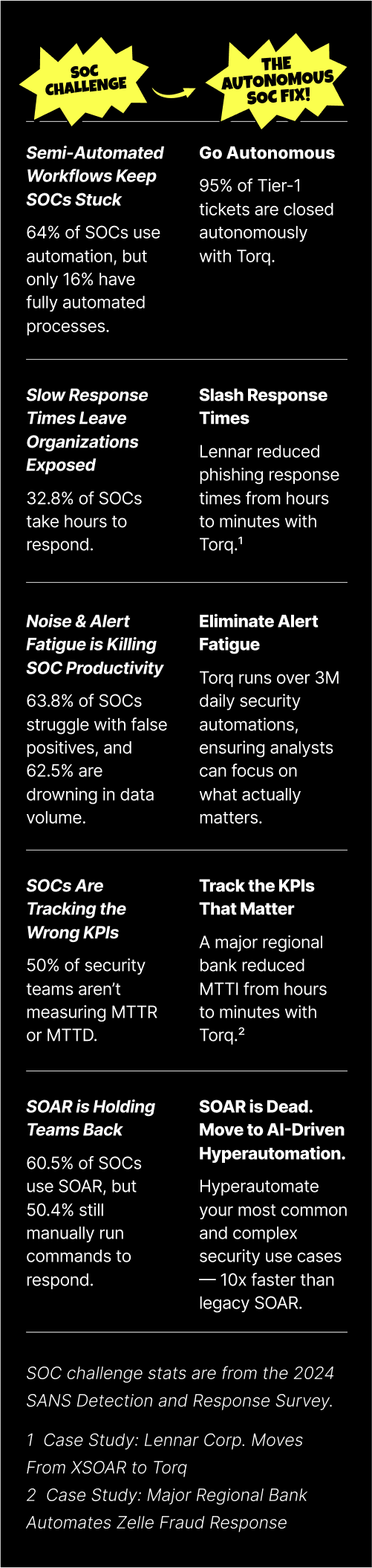
For years, SOAR promised efficiency but delivered bottlenecks. Most legacy SOAR platforms struggle with:
- Rigid playbooks that break as soon as attack patterns shift.
- Slow adoption due to complex coding requirements.
- Integration limits that leave critical parts of the stack disconnected.
- High maintenance costs that drain already-stretched SOC analysts.
This leaves security operations centers overwhelmed by alert volume, unable to evolve with modern threats, and locked into inefficient tools.
SOC transformation requires moving beyond SOAR. With Torq, migration isn’t about replicating brittle playbooks — it’s about redesigning how your SOC operates, using Hyperautomation, AI agents, and dynamic case management to create lasting efficiency and resilience.
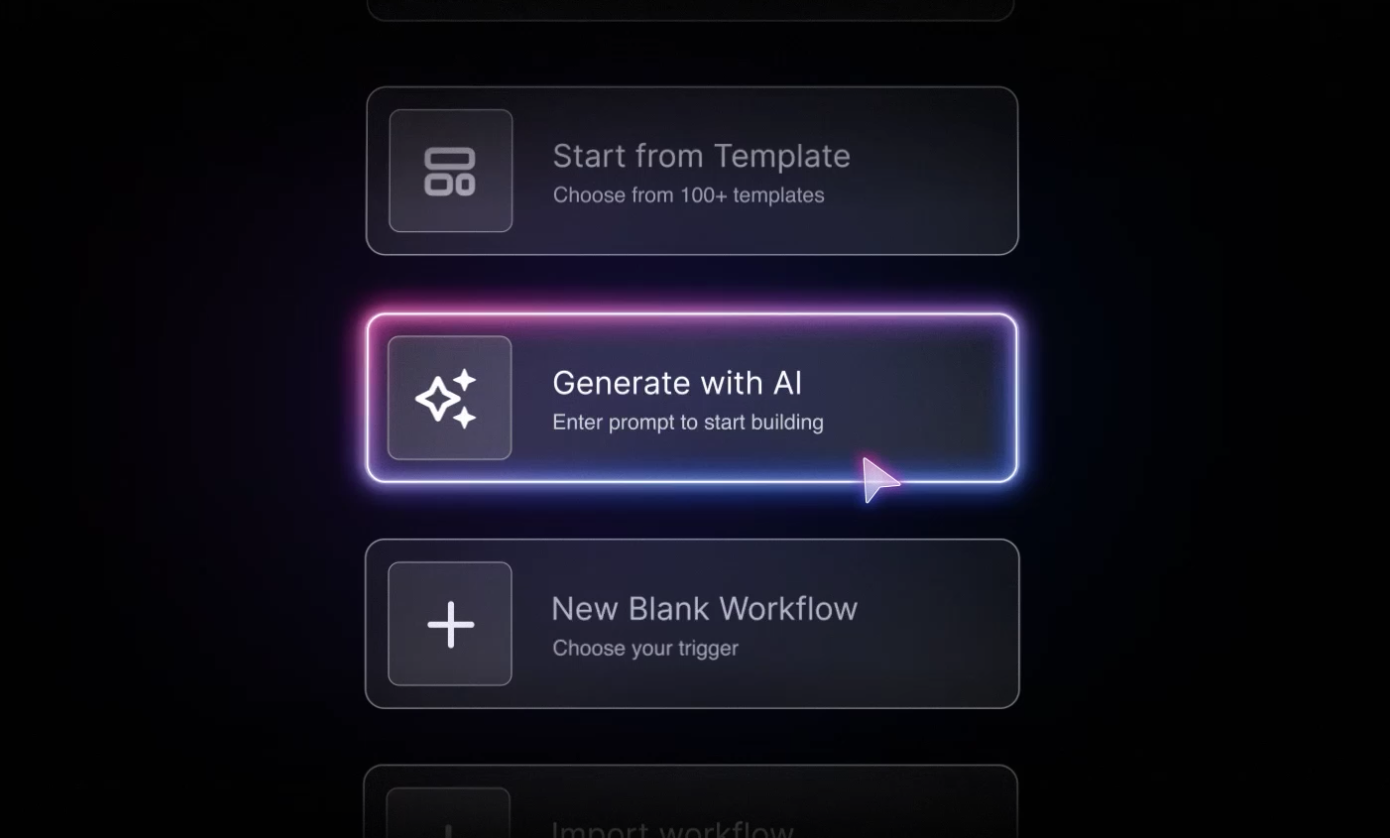
Stop Lifting and Shifting: Redesign Workflows with Hyperautomation
One of the first — and most striking — realizations for companies logging into the Torq platform for the first time is just how easy it is to build workflow automations. For those who previously used code-heavy automation tools and had to manage thousands of lines of Python, Torq’s intuitive, drag-and-drop workflow designer and AI workflow builder is transformative. It enables security teams to build and deploy Hyperautomated workflows faster than ever before. Users can also test each workflow step in real time, gaining instant feedback and making adjustments on the fly.
With Torq, even customizing integrations with APIs or configuring various data sources becomes accessible to those without advanced dev skills, by using AI agents with expert coding logic and syntax for script writing, CLI, and data manipulation.
When migrating existing workflows to Torq, the platform’s ease of use and robust scalability allow for things that simply weren’t possible with legacy SOAR. To escape tech debt and inefficient and outdated processes, Torq encourages new customers to think beyond a “lift and shift” mentality so they can optimize processes rather than replicating them exactly as they were.
The Torq team has seen it all and has vast expertise and experience to recommend best practices for optimizing security processes. Torq Hyperautomation makes it much simpler to combine traditional workbooks into seamless workflows that take advantage of the platform’s strengths, such as AI-driven remediation and dynamic case management.
Most Torq customers can consolidate processes during the migration — achieving the same outcomes with significantly fewer and much more efficient automations.
Unblock Your Stack: Eliminate Integration Limits with Torq
In almost every proof of concept (POC), new users consistently highlight the same recurring challenges with their legacy SOAR platforms: limited integrations and difficulty connecting to essential data within existing tech stacks. This often forced their teams to resort to extensive, time-consuming Python coding, a painful and difficult-to-scale process.
Torq enables rapid, limitless integrations. Companies can connect their entire security stack in record time by using AI to generate integrations in seconds, or they can maintain granular control with draggable, low-code, or full-code capabilities. Even if your third-party API or data format changes (a recipe for disaster in legacy SOAR platforms), real-time API monitoring ensures none of your integrations are at risk of breaking, so your stack always stays connected for uninterrupted automation.
In one example Mark shared, a customer needing specific SIEM technology functions — which were previously inaccessible through their SOAR platform — achieved their goal in minutes by simply copying an API command into Torq’s intuitive Workflow Builder canvas, eliminating the need to wait months for a team to develop custom code to create the connection.
Go From Concept to Workflow, Fast
“Whenever we talk to customers or the folks that are POCing Torq and getting into the platform for the first time, there’s one word that comes up in every single engagement: intuitive.”
– Mark Carosella, Sales Engineering Manager, Torq
Building security automation workflows in Torq’s drag-and-drop and AI-assisted interface is highly intuitive, so teams quickly grasp the fundamentals to get up and running during onboarding. Mark shared that new users often independently build custom automation workflows within a day or two. This can feel like a major “aha” moment for users who came in with the perception of automation as a complex, code-heavy experience in legacy SOAR platforms.
One Torq user shared, “My favorite thing about Torq is that concepts go from my head to a working reality in just a few hours, instead of a few weeks, largely due to the no-code functionality.”
This ease of use empowers any user, regardless of their coding skills, to rapidly implement workflows and adapt their security operations, accelerating time to value.
Inside the SOC Transformation Experience: What Surprises Torq Customers Most
When organizations migrate to Torq, we always hear these things:
- How fast adoption happens. Teams expect a steep learning curve but find themselves self-sufficient within days.
- How flexible the system is. Workflows aren’t locked into rigid playbooks; they adapt as threats evolve.
- How much easier integrations become. Instead of brittle connectors, everything connects in real time — security, IT, SaaS, and beyond.
- How much efficiency scales. Customers consolidate dozens of workflows into streamlined, AI-powered automations that handle 95%+ of Tier-1 tasks.
- How analysts feel the impact. Less alert fatigue, fewer overnight pings, and more time for high-value work like threat hunting and investigation.
Real-World Impact: Torq Use Cases
Migration stories are nice. Measurable outcomes are better. Here’s what SOC transformation actually looks like when legacy SOAR gets replaced by Hyperautomation.
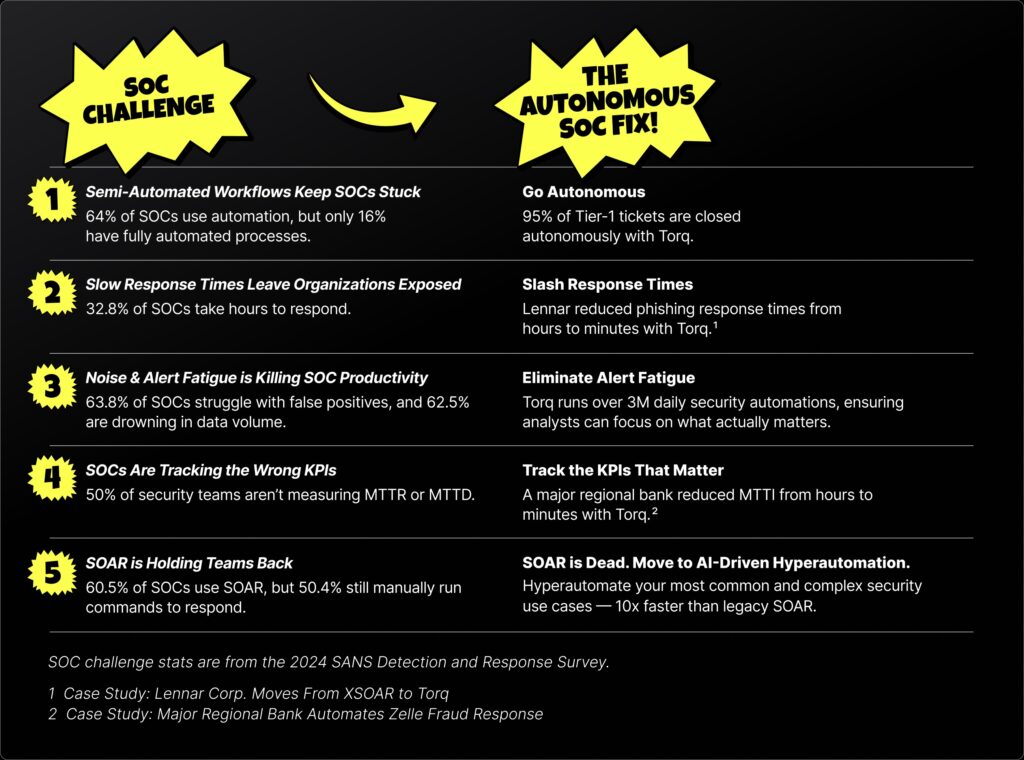
Alert Overload
The problem: SOCs are buried under thousands of daily alerts — most of them noise. Analysts spend 75% of their time on manual triage instead of actual threat hunting, and at least 30% of alerts never get investigated at all.
The solution: Torq’s AI Agents automatically triage incoming alerts, enrich them with contextual data, and filter false positives before they ever reach an analyst. No static playbooks. No manual correlation. No burnout.
The result: Organizations using Torq reduce false positives by 70%+ and enable analysts to focus on critical threats — reclaiming hours of capacity daily.
Playbook Maintenance Drain
The problem: Legacy SOAR playbooks break constantly — every API change, every new tool, every evolving threat pattern requires manual updates. Security teams spend more time maintaining automation than benefiting from it.
The solution: Torq Hyperautomation replaces brittle playbooks with dynamic, AI-driven workflows that adapt in real time. The AI Workflow Builder lets teams create automations using natural language, and real-time API monitoring ensures integrations stay connected even when vendors ship changes.
The result: Teams that previously managed 50+ fragile playbooks consolidate to fewer, smarter workflows — deploying automations 10x faster than legacy SOAR and eliminating the maintenance tax entirely.
Slow Incident Response
The problem: When incidents hit, legacy SOAR can’t keep up. Static playbooks don’t adapt to novel attack patterns, and manual handoffs between tools add hours to response times — giving attackers more dwell time.
The solution: Torq HyperSOC™ unifies detection, investigation, and response into a single platform powered by agentic AI. Socrates, the AI SOC Analyst, autonomously triages, investigates, and remediates threats at machine speed — escalating only what truly requires human judgment.
The result: Organizations reduce investigation time by up to 90% and handle 3-5x more alerts without adding headcount. MTTR drops from hours to minutes.
Transform Your SOC: Get the SOAR Migration Guide
If you’re ready to finally pull the plug on your SOAR, get the Kill Your SOAR Migration Guide to plan ahead. It covers the big picture of what you need to know going into a migration, plus a migration success story from a leading security company, advice from a SOC manager who made the switch, and the top 3 POC use cases.
With Torq, your migration isn’t just about switching platforms — it’s an opportunity to transform your security operations.