It’s 2024, and we’ve got to stop using “automation” and “orchestration” synonymously.
Security automation eliminates manual effort by automatically executing tasks at machine speed. Security orchestration streamlines processes by connecting disparate tools and coordinating multiple automated workflows.
But not all automation is created equal. Traditional security automation has limitations. Enter AI-driven Hyperautomation, which takes security operations beyond scripted workflows into a truly autonomous, self-sustaining security model.
Here’s why that matters and why legacy SOAR’s approach to security orchestration is no longer effective.
What is Security Automation?
Security automation leverages AI and automated workflows to efficiently handle cybersecurity tasks at machine speed, eliminating the need for human intervention and reducing time-consuming manual processes. This enables faster threat detection, analysis, and response. Instead of waiting on your already bogged-down analysts to triage and investigate alerts, automation executes predefined actions instantly, ensuring faster, more accurate responses.
What was once a luxury for Fortune 500s is now non-negotiable for any security team facing overwhelming alert volumes, talent shortages, and non-stop cyberattacks.
In a modern SOC, automation can handle most of Tier-1 work and repetitive, time-consuming tasks for security teams. The use cases are endless, ranging from threat detection and response to GRC workflows like compliance and patch deployment, to blocking domains and encrypting data.
The benefits speak for themselves. Cybersecurity automation accelerates response times, filters out false positives, and provides the context analysts need to take decisive action. It doesn’t take breaks, it doesn’t get overwhelmed, and it operates at machine speed 24/7 to stop threats before damage is done.
What is Security Hyperautomation?
At Torq, we call this AI-driven Hyperautomation. Torq Hyperautomation™ is security automation that goes beyond simple playbooks and rigid rule sets.
Unlike traditional security automation, which focuses on predefined rule-based responses, Torq Hyperautomation dynamically connects disparate tools, enriches alerts with real-time intelligence, and autonomously executes remediation — all without manual intervention. It integrates AI and large language models (LLMs) to correlate signals across multiple sources, filter false positives, and instantly prioritize real threats.
So, what makes Torq Hyperautomation different?
- Intelligent case automation and prioritization: Comprehensive case management that reduces the analyst’s workflow through automation and enhanced response times.
- Autonomous remediation: No waiting for analysts to act. Hyperautomation automatically isolates compromised endpoints, blocks malicious domains, and disables compromised accounts in seconds.
- Full-stack integration: Legacy SOAR is notorious for missing critical integrations, causing silos. Torq Hyperautomation connects to every tool in your stack.
- No-code automation: No engineers, no problem. Hyperautomation lets SOC teams automate complex processes using natural language, making security automation accessible to everyone, not just developers.
Where security automation removes friction, Hyperautomation eliminates inefficiencies entirely — allowing organizations to move from reactive to proactive, self-sustaining security operations. With agentic AI-powered automation, security teams can investigate, escalate, and remediate threats autonomously, closing security gaps faster than ever. AI-powered Hyperautomation doesn’t just improve security workflows but redefines modern SOCs’ operations.
“Employing AI to augment human security analysts acts as a force multiplier that helps security teams be more productive. This approach not only improves response times, but also ensures that human ingenuity is applied where it is most needed, effectively expanding the capabilities of existing security teams.” – Forbes
Security Automation in Action: Real-World Use Cases
Understanding security automation and orchestration concepts is one thing — seeing them deliver measurable results is another. Here’s how organizations are using Torq Hyperautomation™ to solve their most pressing security challenges.
Eliminating Alert Fatigue and Accelerating Threat Response
The problem: Security teams are drowning in alerts. The average SOC receives thousands of notifications daily, and analysts simply can’t keep pace. The result? Slow response times, missed threats, and burnout. When every alert requires manual triage, investigation, and action, critical threats can sit unaddressed for hours — giving attackers the time they need to move laterally and escalate damage.
The solution: Torq automates alert triage using AI-driven workflows that analyze, enrich, and prioritize incoming threats at machine speed. Instead of analysts manually reviewing every notification, Torq’s Hyperautomation platform automatically correlates signals across multiple security tools, filters out false positives, and escalates only verified threats that require human attention. For confirmed incidents, Torq can autonomously execute containment actions — isolating endpoints, blocking malicious IPs, and disabling compromised accounts — without waiting for manual intervention.
The result: Organizations implementing Torq’s automated alert triage have achieved a 40% reduction in response time, dramatically enhancing threat mitigation efficiency. Analysts are freed from repetitive triage work to focus on strategic threat hunting, while threats are contained in seconds rather than hours.
Streamlining Patch Management Across the Enterprise
The problem: Patch management is a critical but often neglected security function. When vulnerabilities are disclosed, organizations face a race against time to deploy patches before attackers can exploit them. But manual patch deployment is slow, error-prone, and resource-intensive — especially across complex environments with thousands of endpoints, multiple operating systems, and distributed infrastructure. Delays in patching leave systems exposed and create windows of opportunity for attackers.
The solution: Torq’s security orchestration automates the entire patch management lifecycle. When new vulnerabilities are identified, Torq workflows automatically assess which systems are affected, prioritize patches by risk severity, coordinate deployment schedules across teams, and execute patch installations across systems — all without manual coordination. Integration with vulnerability scanners, ITSM platforms, and endpoint management tools ensures that patches are deployed consistently and verified as successful.
The result: Teams using Torq for automated patch management have compressed remediation timelines from weeks to hours, minimizing the window of vulnerability exposure and improving overall system integrity. Automated verification ensures patches are applied correctly, reducing the risk of misconfigurations and compliance gaps.
What is Security Orchestration?
Security orchestration is the automated management and coordination of multiple security workflows, often spanning multiple tools within an organization’s security infrastructure.
Orchestration ensures that interdependent automated tasks within the security ecosystem proceed smoothly, with data shared effectively and subsequent actions triggered correctly across different tools. Orchestration is crucial for managing complex security operations where automated processes rely on each other for completion and data exchange.
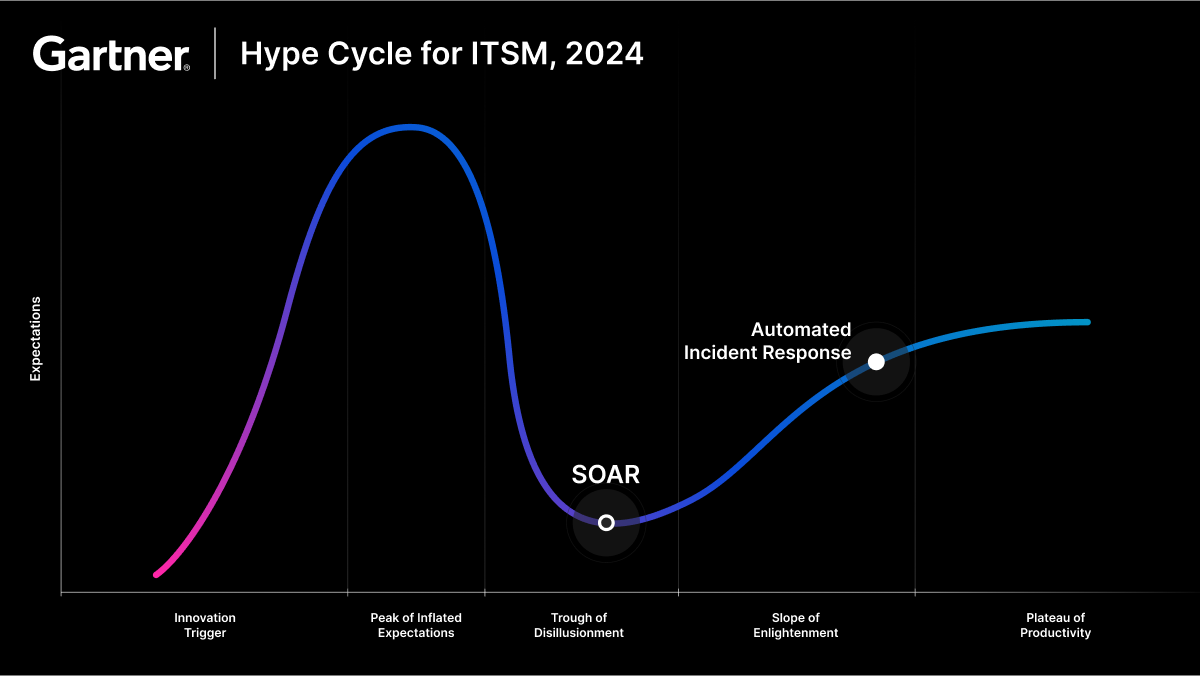
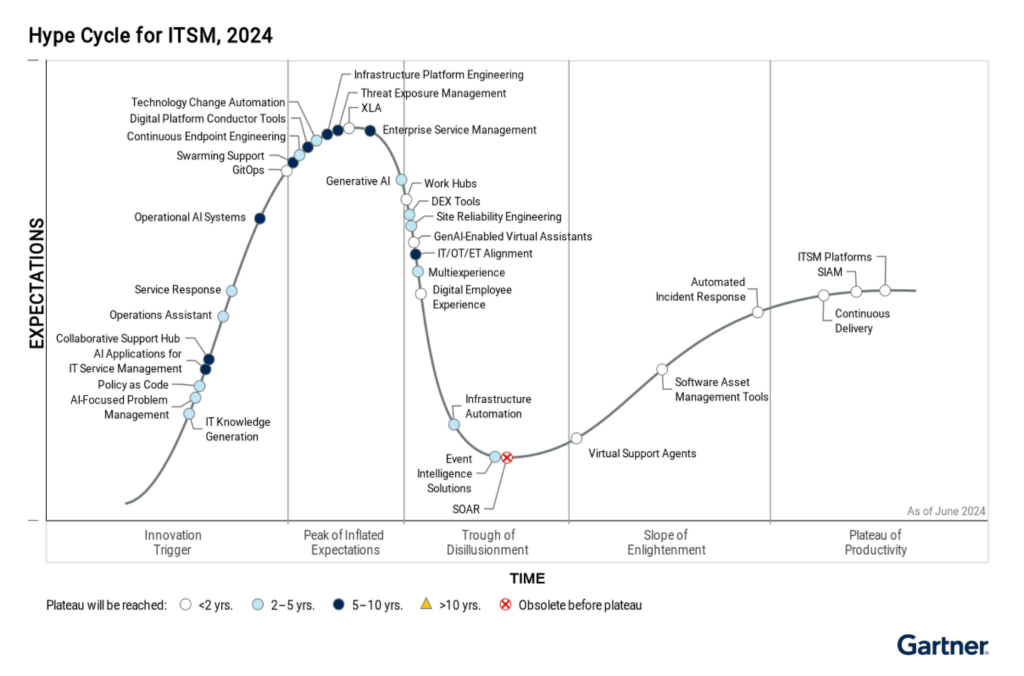
Why is SOAR Dead?
Security Orchestration and Response (SOAR) platforms were supposed to be the missing link between security tools to streamline workflows and reduce manual efforts. Instead, they became bottlenecks and money pits.
SOAR platforms promised to unify security operations. They failed. Why?
- Playbooks required constant maintenance
- They were slow, rigid, and lacked adaptability
- They demanded skilled engineers to build and manage workflows
- They relied on manual tuning
Security teams don’t need another tool that creates more work — they need one that eliminates it. That’s why Security Hyperautomation is the next evolution. AI-driven, no-code, and fully autonomous.
Ready to pull the plug on your SOAR? We can help >
Why Hyperautomation Replaces SOAR-Based Security Orchestration
Security orchestration as a concept isn’t dead — it’s evolving. Torq still orchestrates workflows, but not the way legacy SOAR did. Here are the main differences:
- Legacy SOAR playbooks require maintenance. Hyperautomation learns and adapts in real time.
- Legacy SOAR is static. Hyperautomation makes security processes dynamic, enabling them to optimize and adapt to new attack patterns.
- Legacy SOAR requires engineers. Hyperautomation is no-code and accessible to any SOC analyst.
- Legacy SOAR operates in silos. Hyperautomation connects seamlessly across your entire environment.
The clunky, expensive orchestration of the SOAR era is over. But intelligent, adaptive orchestration powered by agentic AI is alive and thriving in the world’s most advanced SOCs.
Hyperautomation in Action: Real-World Results
Accelerating threat response: Manual investigation and containment takes 30+ minutes per alert — time attackers use to move laterally. Torq Hyperautomation executes detection, enrichment, and containment in seconds, automatically isolating endpoints and disabling compromised accounts the moment indicators are confirmed. Valvoline cut analyst workload by 7 hours per day after implementing Torq.
Eliminating integration bottlenecks: Legacy SOAR platforms are notorious for missing critical integrations — creating silos and forcing manual workarounds. Torq connects seamlessly across your entire stack with 300+ pre-built integrations and AI-powered custom integration generation.
No-Code Automation for Every Analyst: Traditional automation required skilled engineers to build and maintain playbooks — a bottleneck most SOCs can’t afford. Torq’s no-code interface lets any analyst create complex workflows using natural language, removing the barrier between security expertise and automation capability. Fiverr’s VP of Business Technologies says: “The only limit Torq has is people’s imaginations.”
Autonomous Tier-1 Operations: Alert fatigue drowns SOC teams; analysts can’t keep pace with thousands of daily notifications. Torq’s agentic AI handles Tier-1 triage autonomously, filtering false positives, enriching real threats, and executing containment without human intervention. Carvana automated 100% of Tier-1 alerts within one month, with 41 runbooks deployed and running at machine speed.
The Bottom Line
Security automation and security orchestration aren’t interchangeable — but in 2024, the distinction matters less than the outcome. Legacy SOAR tried to orchestrate rigid playbooks across siloed tools and failed. Modern Hyperautomation delivers what SOAR promised: unified, intelligent, autonomous security operations that actually work.
The question isn’t whether to automate; it’s whether your automation can keep pace with attackers operating at machine speed. Static playbooks can’t. AI-driven Hyperautomation can.
Torq combines the speed of automation with the coordination of orchestration, powered by agentic AI that reasons, adapts, and executes without waiting for human intervention. It’s why the world’s most advanced SOCs have moved entirely away from legacy SOAR.
Get the GigaOm SOAR Radar Report to learn why Torq has outranked legacy SOAR for two years running.
FAQs
What is the difference between security automation and orchestration?
Security automation executes individual tasks at machine speed without human intervention — like blocking a malicious IP or isolating an endpoint. Security orchestration coordinates multiple automated workflows across different tools, ensuring data flows correctly and actions trigger in sequence. Automation handles the “doing,” orchestration handles the “connecting.” Modern Hyperautomation combines both into a unified, AI-driven approach. Learn more about Hyperautomation →
How does security Hyperautomation improve traditional methods?
Traditional automation relies on static, rule-based playbooks that break when conditions change. Hyperautomation uses AI and LLMs to dynamically adapt — correlating signals across tools, filtering false positives, prioritizing real threats, and executing remediation autonomously. It’s the difference between following a script and actually reasoning through a problem. Torq customers like Carvana now automate 100% of Tier-1 alerts with agentic AI.
Why is legacy SOAR considered outdated?
Legacy SOAR platforms promised unified security operations but delivered complexity instead. Playbooks required constant maintenance, integrations were limited, and skilled engineers were needed to build and manage workflows. They created more work, not less. Hyperautomation eliminates these pain points with no-code building, 300+ pre-built integrations, and AI that adapts in real time. See why SOAR is dead →
What benefits does AI-driven security automation provide?
AI-driven automation accelerates response times from hours to seconds, filters out false positives before they reach analysts, and provides contextual enrichment for faster decision-making. It operates 24/7 without fatigue, handles unlimited alert volumes, and frees analysts to focus on strategic threat hunting instead of repetitive triage.
How can organizations transition from manual to automated security processes?
Start by identifying high-volume, repeatable workflows — phishing triage, suspicious login investigation, and endpoint isolation are common starting points. Choose a platform with pre-built templates and no-code customization so your team can deploy quickly without engineering dependencies. Measure results (MTTR, automation rate, analyst hours saved), then progressively expand. Torq customers typically see production value within 30 days. Get a demo →