Contents
Get a Personalized Demo
See how Torq harnesses AI in your SOC to detect, prioritize, and respond to threats faster.
One of the superpowers of the Torq Hyperautomation platform is the ability to integrate with anything. We combine forces with leading security vendors to create automations that make SOC analysts’ lives easier while also improving their organizations’ security posture.
Torq Hyperautomation integrates seamlessly with Recorded Future to take your threat intelligence workflows from manual and reactive to fully automated and autonomous.
Whether you’re enriching IOCs, sandboxing suspicious files, detecting phishing, or spotting impossible logins, Torq makes it easy to turn Recorded Future threat intel into real-time security action — without writing a single line of code.
Why Integrate Recorded Future with Torq?
Recorded Future is one of the most powerful threat intelligence platforms available, collecting, analyzing, and delivering high-fidelity data on threat actors, tactics (TTPs), and indicators of compromise (IOCs). But using it effectively still requires:
- Manual triage of alerts and indicators
- Context switching between tools
- Analyst time to trigger remediation
By connecting Recorded Future’s API to Torq’s no-code, AI-driven Hyperautomation platform, you can:
- Automate IOC enrichment and validation
- Trigger real-time auto-remediation workflows across your stack
- Share intelligence instantly across SecOps, IT, and cloud teams
- Reduce MTTR by moving from “intel to action” in seconds
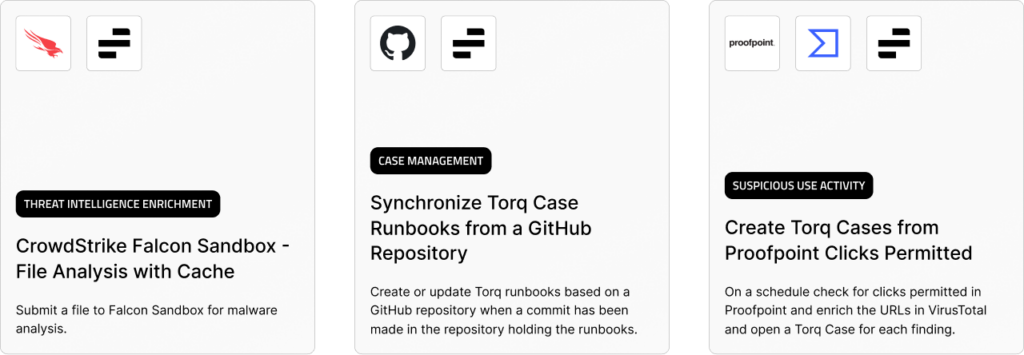
Top Torq + Recorded Future Automations
Here are four high-impact automations that combine the power of Torq’s orchestration with Recorded Future’s threat data.
1. Analyze URLs and Files in Recorded Future Sandbox
Eliminate the manual back-and-forth of investigating suspicious URLs and files by letting Torq handle ingestion, validation, and sandbox submission.
Workflow example:
- Torq receives a list of potentially malicious links or file download URLs from any source — SIEM, email, chat, or manual input.
- URLs in the urls_list are sent for Recorded Future website analysis; file links in the files_url_list are downloaded and submitted for file analysis.
- Invalid or malformed URLs are automatically filtered out to avoid false positives and wasted cycles.
- Recorded Future’s sandbox verdicts (malicious, suspicious, clean) are returned in real time and pushed to the requesting team via Slack, email, or ticketing systems.
SOC teams get actionable verdicts in seconds with zero analyst touch time, drastically reducing triage delays.
2. Enrich Hashes, CVEs, and IP Addresses via Slack
Make threat intelligence instantly available where analysts collaborate, removing the need to pivot between multiple tools.
Workflow example:
- A user drops a SHA256 hash, CVE ID, or suspicious IP into a Slack message or SOC request channel.
- Torq automatically extracts IOCs, confirms the input with the requester, and queries Recorded Future for enrichment.
- Threat context, severity scores, and related intelligence are instantly posted back into the same Slack thread for transparency.
Analysts never leave Slack to check an IOC, reducing investigation times from minutes to seconds and minimizing workflow disruptions.
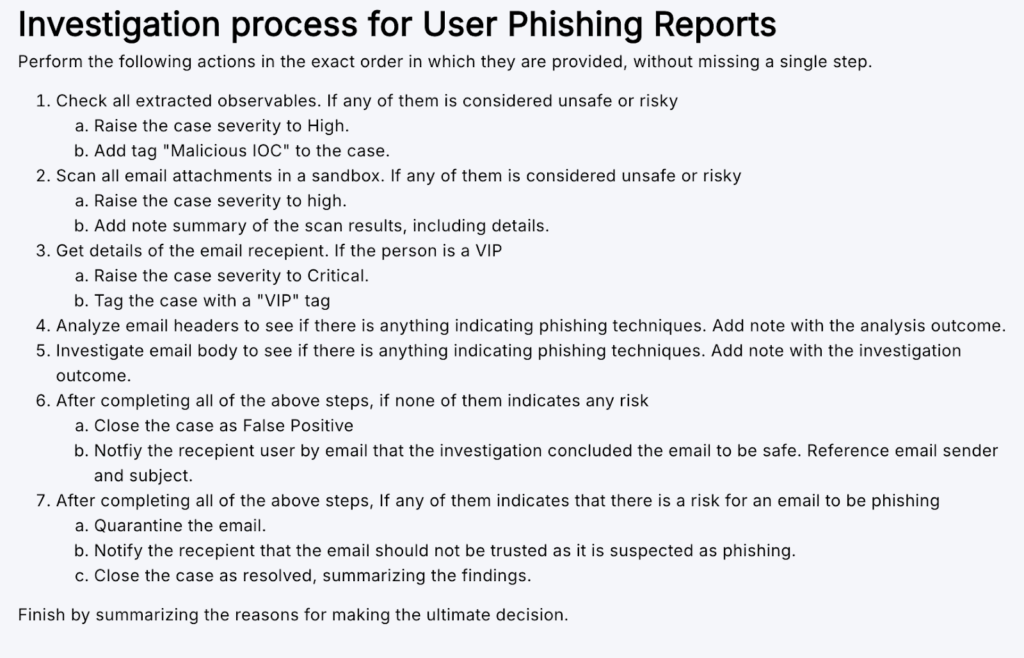
3. Monitor Outlook Mailboxes for Phishing
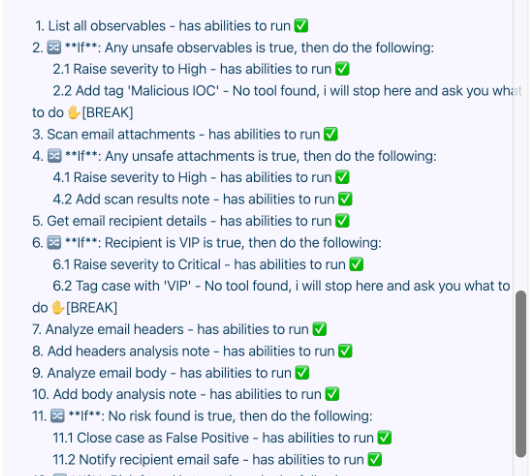
Automatically process and classify suspected phishing emails without analyst intervention.
Workflow example:
- Torq watches a specific Outlook folder (e.g., “Not-Scanned”) for new submissions from users.
- Torq extracts URLs, attachments, and IPs from the email body and headers.
- The platform runs those IOCs through Recorded Future’s intelligence platform and sandbox.
- It applies labels like Investigated, Suspicious, Malicious, or Phishing directly to the mailbox and notifies the reporter of the findings.
End-to-end phishing triage — from user submission to final verdict — happens in minutes, not hours, with zero manual file or URL lookups
4. Detect Impossible Travels in Okta Logins
Identify impossible travel anomalies and respond to compromised accounts in real time using behavioral and geolocation analysis.
Workflow example:
- Torq ingests successful login events from Okta.
- It then compares the login’s IP geolocation to the last known login location for the same user.
- The platform flags logins that occur in physically impossible timeframes (“impossible travel”) for review.
- It queries Recorded Future for IP reputation to confirm risk.
- If suspicious, automatically resets the user’s password, logs them out of active sessions, and sends an alert to both the user and the SOC.
Immediately contain account takeover attempts before malicious actors can escalate privileges or exfiltrate data.
Enrich Your Threat Intel Workflow with Hyperautomation
Recorded Future gives security teams deep, contextual intelligence on the threats that matter most — but intelligence alone doesn’t stop attacks. Without the right orchestration layer, valuable data can sit idle in an inbox, SIEM queue, or analyst’s to-do list.
Torq Hyperautomation ensures that every IOC, every alert, and every piece of context moves seamlessly from insight to action — at scale and without manual intervention.
With Recorded Future’s API feeding into Torq workflows, you can:
- Automate IOC processing: Eliminate manual copy-paste and data re-entry by automatically ingesting hashes, IPs, domains, and CVEs from any source — chat, email, SIEM, or threat feed — and routing them directly into Recorded Future for analysis.
- Enrich data at scale: Combine Recorded Future’s rich threat context with data from internal CMDBs, cloud logs, EDR telemetry, and other intel feeds to build a 360° profile of each IOC, enabling faster and more confident decisions.
- Trigger precise, policy-driven responses: Automatically execute targeted playbooks, such as quarantining an infected endpoint, blocking a malicious domain at the firewall, or disabling a compromised account, all within seconds of detection.
- Eliminate silos across the SOC: Push enriched intel and recommended actions into every relevant system, ensuring all teams have the same, real-time picture of the threat.
Threat data is instantly operationalized by combining Recorded Future’s intelligence with Torq’s Hyperautomated workflows. The result is faster MTTR, fewer missed threats, and a security team that can scale without adding headcount.
From Intelligence to Action — Automatically
Pairing Recorded Future integrations with Torq turns threat intelligence into outcomes: you collect data from technical sources via API, enrich IOCs with TTPs, and orchestrate precise actions across endpoints — all surfaced in shared dashboards. This approach facilitates faster triage and lowers MTTR by moving what’s collected into real decisions and responses in seconds, not hours.
Whether you’re piloting or pushing to GA, Torq operationalizes your intel pipeline end-to-end — so your analysts spend time resolving threats, not copy-pasting between tools.
Don’t let valuable threat data sit idle. Read our Don’t Die, Get Torq manifesto to see how your SOC can eliminate Tier-1 grind and focus on what matters most.