TL;DR
- EDR tools go beyond antivirus — they monitor endpoints continuously, detect unknown threats through behavioral analytics, and enable forensic investigation and containment.
- The biggest EDR challenge is response, not detection. Alert volume, siloed data, and manual handoffs create costly delays between alert and resolution.
- Agentic AI and Hyperautomation close the response gap — automating triage, enriching alerts with cross-stack context, and executing response actions in seconds.
- Torq integrates with 11+ leading EDR platforms and connects endpoint signals to automated response across your entire security stack.
Endpoint detection and response (EDR) tools are a cornerstone of modern SOC operations. But even the best EDR solution on the market has a ceiling, and most security operations teams hit it faster than they expect.
The ceiling isn’t detection. Today’s EDR tools are excellent at spotting threats. The ceiling is response: what happens after the alert fires, how fast your team can move, and how much of that process still requires a human to do it manually.
This post covers what EDR tools are, what they do within your security stack, and how agentic AI and Hyperautomation platforms help SOC teams automatically turn EDR signals into resolved incidents.
EDR stands for endpoint detection and response. EDR tools are security software that continuously monitor endpoints — laptops, servers, cloud workloads, and mobile devices — for suspicious activity. They use behavioral analytics and machine learning to detect known and unknown threats in real time, and they give security teams the visibility and tooling to investigate and contain those threats.
The “endpoint” part is key. Unlike perimeter-based security tools that watch what comes in and out of the network, EDR tools watch what’s happening on the device itself: process execution, file modifications, registry changes, lateral movement, and more.
EDR tools do a lot more than just fire alerts. Here’s what’s happening under the hood across a typical deployment.
Continuous endpoint monitoring. EDR agents run on every enrolled device and continuously collect telemetry: process activity, network connections, file system changes, and user behavior. This isn’t periodic scanning; it’s always-on visibility.
Behavioral threat detection. Rather than relying solely on signatures, EDR tools analyze behavior patterns to identify anomalies. If a process that shouldn’t be making outbound network connections suddenly starts doing so, the EDR flags it, even if the underlying malware is brand new.
Alert generation and telemetry enrichment. When suspicious activity is detected, the EDR surfaces an alert with supporting context: what happened, on which device, under which user account, and what the process tree looks like leading up to it.
Forensic investigation. EDR tools give analysts the timeline and historical data to investigate an incident thoroughly, tracing lateral movement, identifying patient zero, and understanding the full scope of a compromise.
Containment actions. Most EDR platforms can take direct action on an endpoint: isolating it from the network, killing a malicious process, or blocking the execution of a specific file. These are the response capabilities that make EDR distinct from passive monitoring tools.
The challenge? EDR tools generate an enormous volume of signal. Enterprise environments can produce thousands of alerts per day. Detection isn’t the bottleneck. It’s what happens after the alert fires that separates high-performing SOCs from the ones perpetually stuck in reactive mode. Alert fatigue is real, and EDR alone doesn’t solve it.
Most enterprise SOC teams are working with one or more of the following platforms. Here’s a high-level look at the tools encountered most often.
CrowdStrike Falcon
CrowdStrike Falcon is one of the most widely deployed EDR platforms in enterprise security. It’s cloud-native, built on a single lightweight agent, and backed by real-time threat intelligence from CrowdStrike’s global sensor network. Falcon is well-regarded for its speed of detection and depth of threat intelligence integration.
Microsoft Defender for Endpoint
Microsoft Defender for Endpoint is deeply embedded in Microsoft 365 environments, making it a natural fit for organizations already running the Microsoft stack. It provides EDR capabilities alongside vulnerability management, attack surface reduction, and integration with Microsoft Sentinel for broader SIEM correlation.
SentinelOne Singularity
SentinelOne is known for its AI-driven autonomous response capabilities. Its platform can detect, quarantine, and remediate threats at the endpoint without waiting for analyst input, a design philosophy that aligns well with automation-first SOC strategies.
Carbon Black (VMware/Broadcom)
Carbon Black offers both cloud-delivered and on-premises EDR solutions, with strong behavioral detection and threat-hunting capabilities. It’s widely used in regulated industries where deployment flexibility matters.
Regardless of which EDR platform is in your stack, the challenge most SOC teams face is the same: it’s not finding the threat. It’s operationalizing the response quickly and consistently enough to matter.
EDR tools are exceptional at what they’re built for. But detection is only half the equation. The gap between “alert fired” and “incident resolved” is where attacks do damage, and where most SOC teams are losing ground.
A few of the dynamics that create this gap:
Alert volume. Enterprise EDR deployments generate thousands of alerts per day. Analysts simply cannot manually triage everything. Without automated prioritization, high-fidelity alerts get buried in noise and response times suffer.
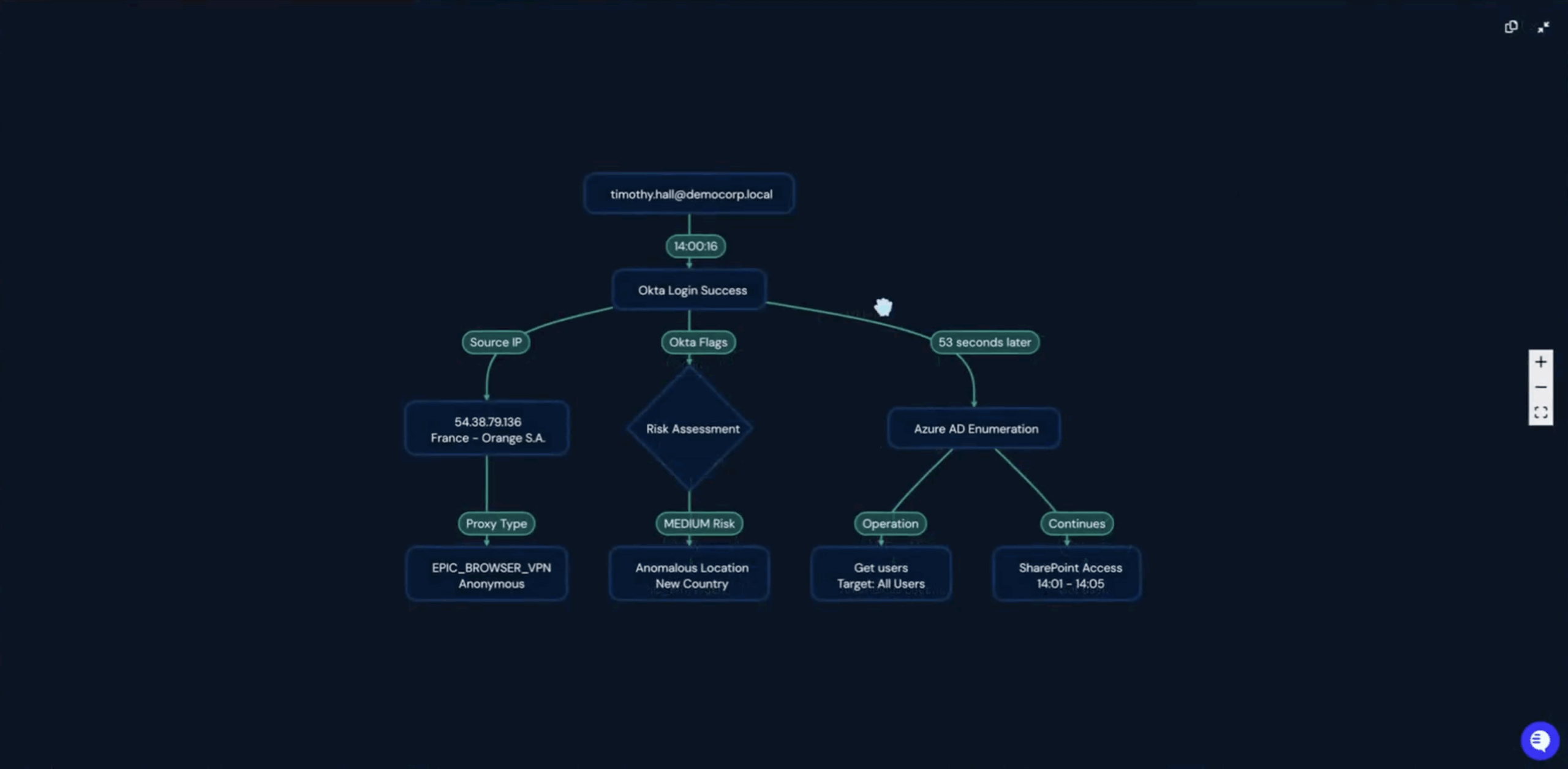
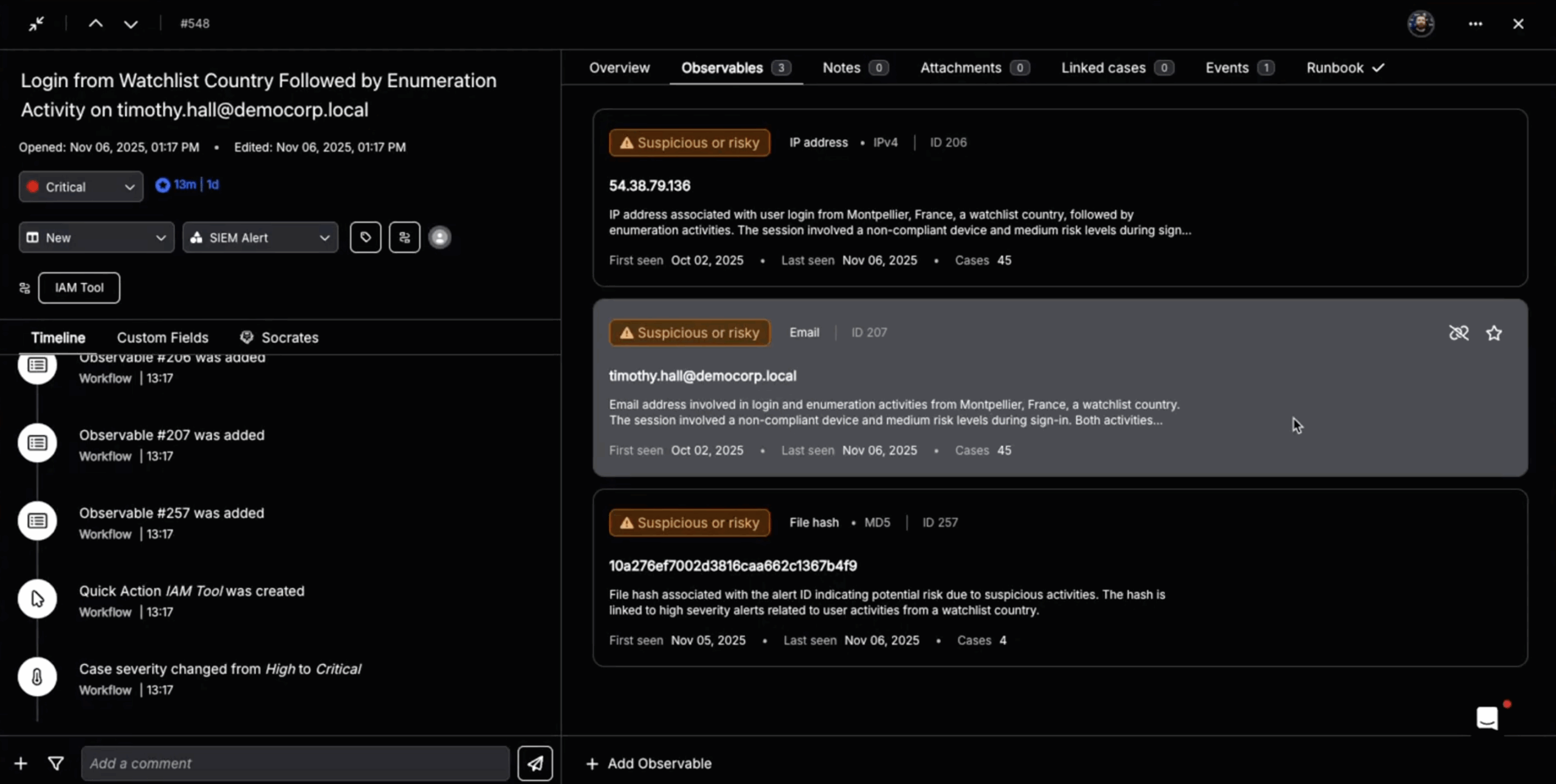
Siloed data. EDR telemetry lives in one console, identity data in another, network logs somewhere else, and threat intelligence in yet another platform. Correlating all of that manually takes time, and attackers use that time to their advantage.
Manual response steps. Even after a threat is confirmed, the response workflow often requires an analyst to touch multiple tools: isolate the endpoint in the EDR console, revoke credentials in the identity provider, open a ticket in the ITSM platform, and notify the user’s manager. Each handoff introduces delay.
Dwell time. The longer it takes to move from detection to containment, the greater the blast radius. IBM’s Cost of a Data Breach Report has consistently shown that organizations with faster detection and response times incur significantly lower breach costs. Every minute matters.
The tools themselves aren’t failing. The gap is structural. EDR was designed to detect and enable response. What fills the space between “enable” and “execute” is where automated incident response comes in.
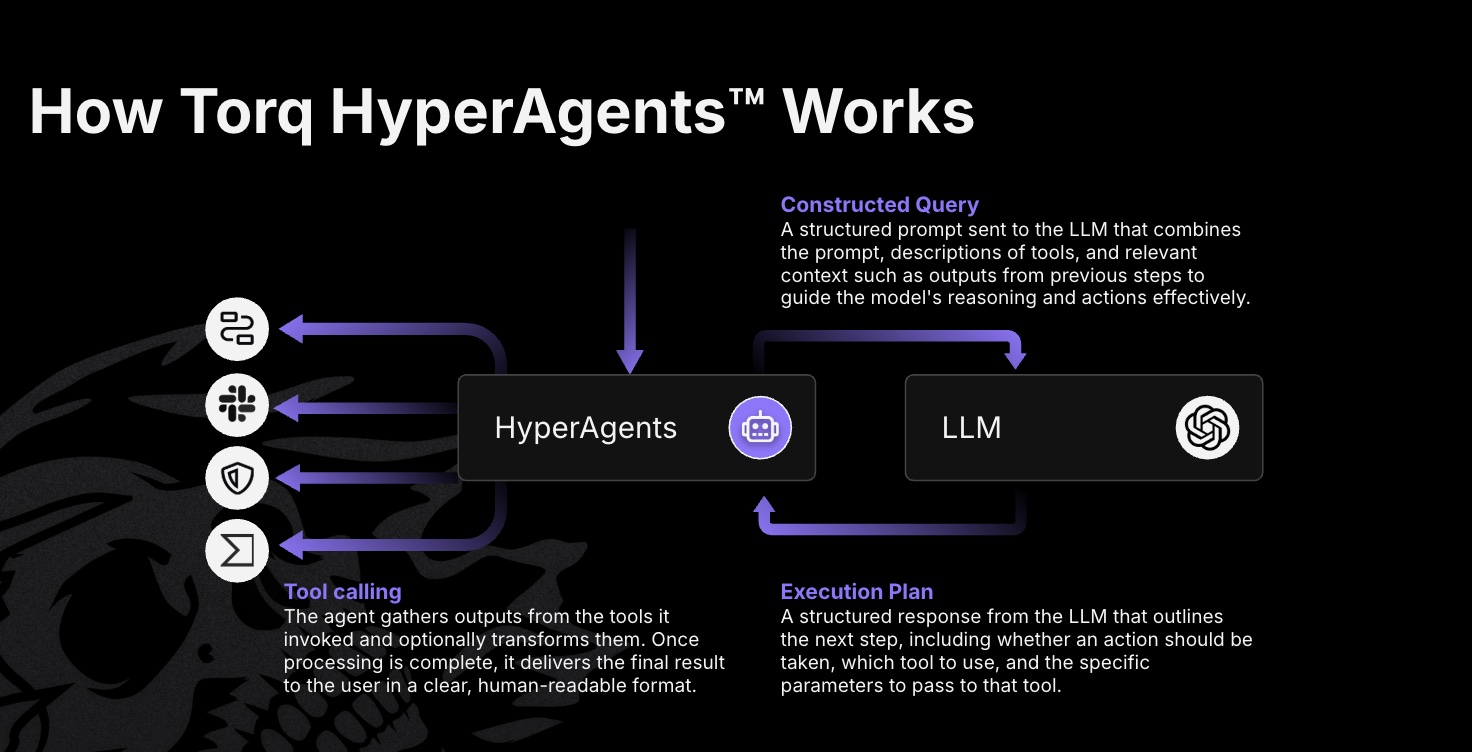
How Agentic AI and Hyperautomation Extend EDR Capabilities
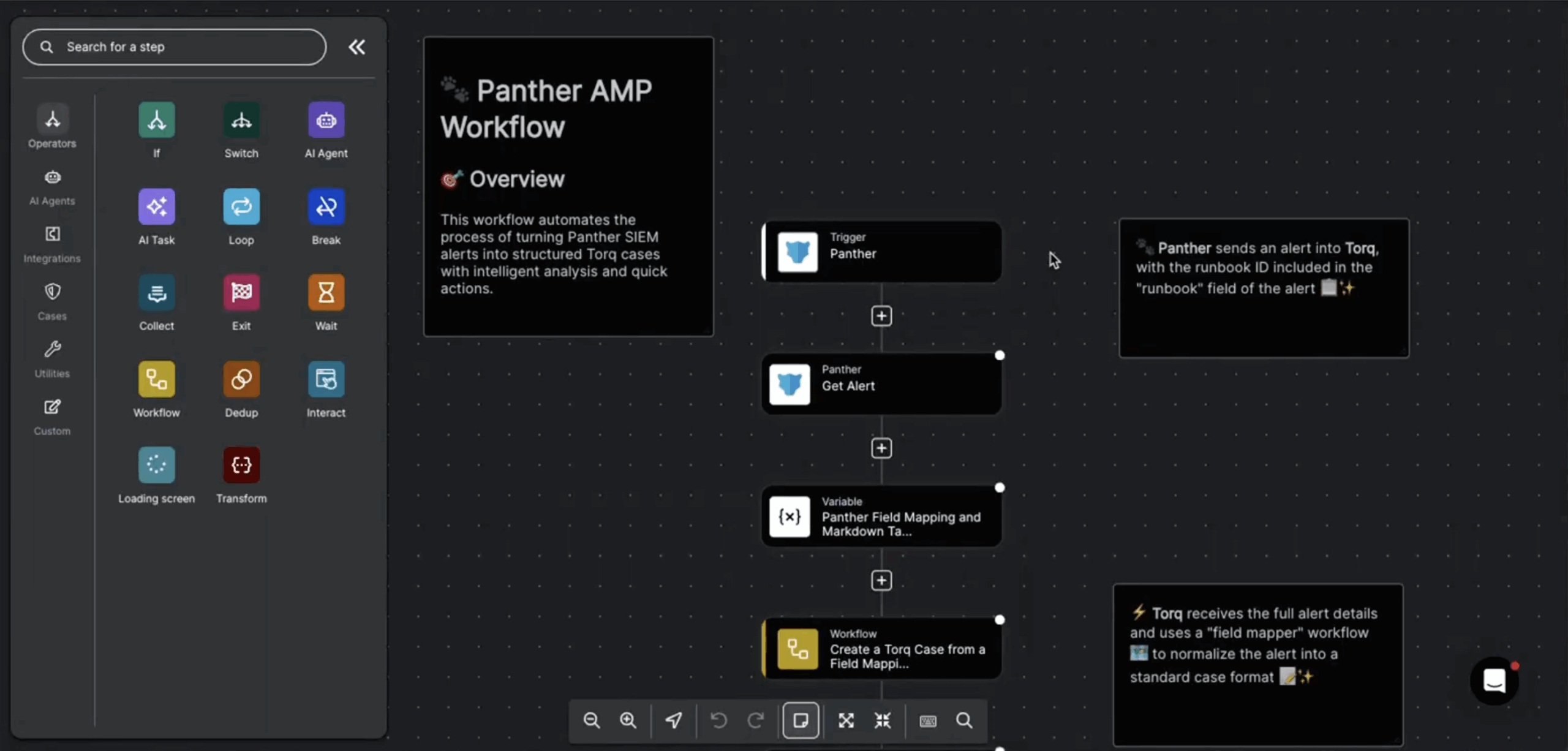
The most effective SOC teams today pair their EDR tools with agentic AI and an AI SOC platform that converts detection signals into response actions automatically.
Here’s what that looks like in practice.
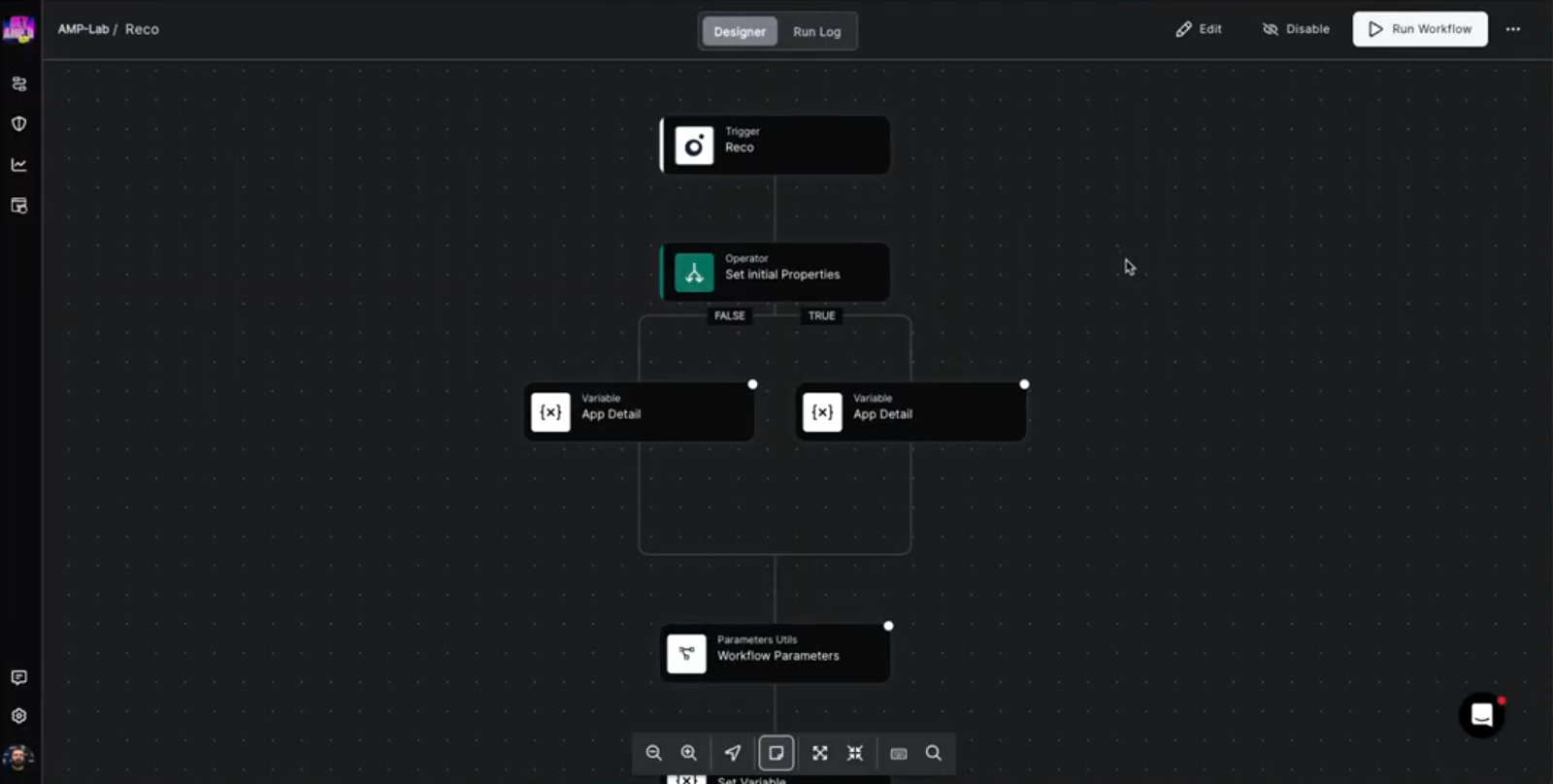
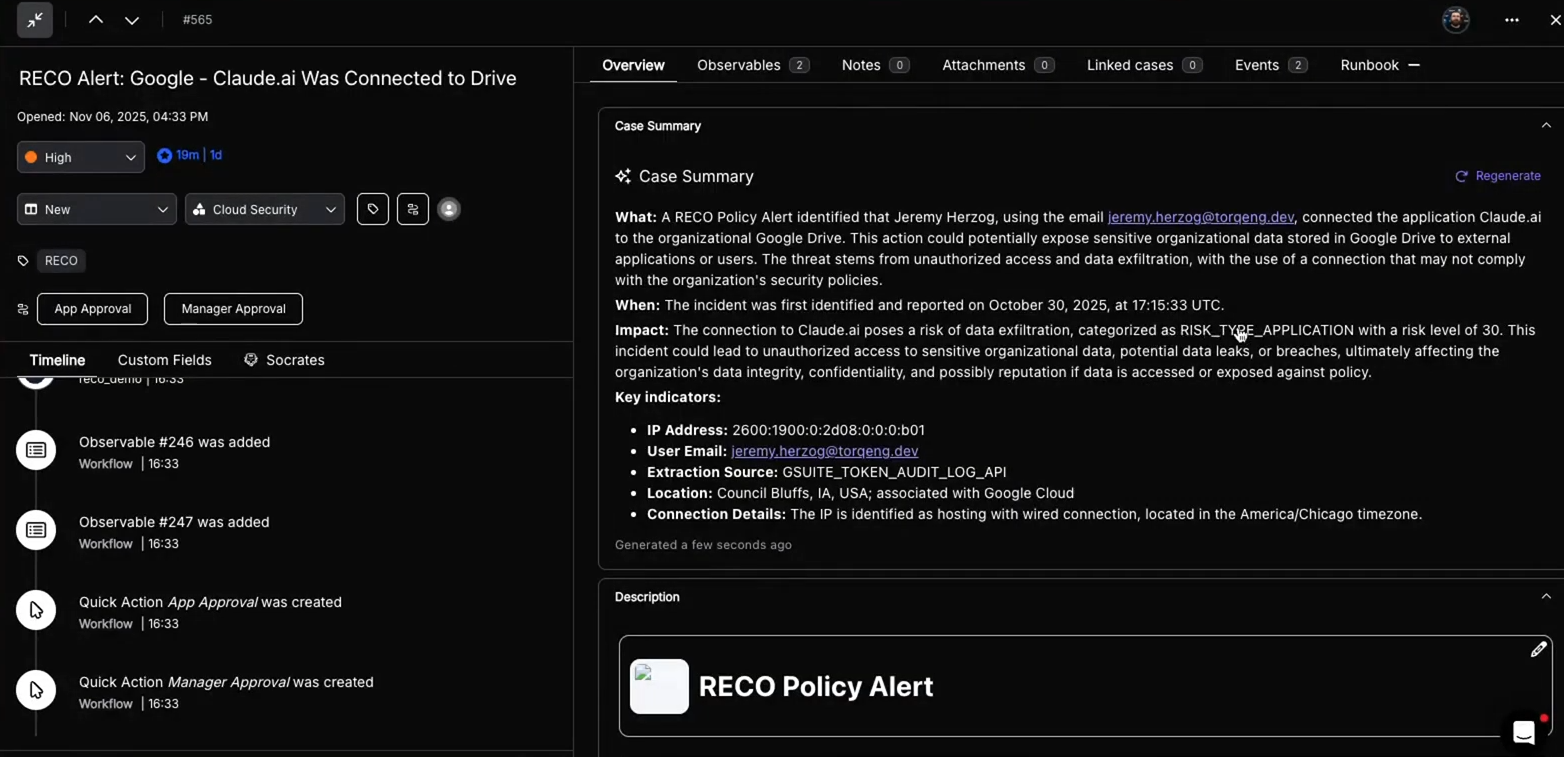
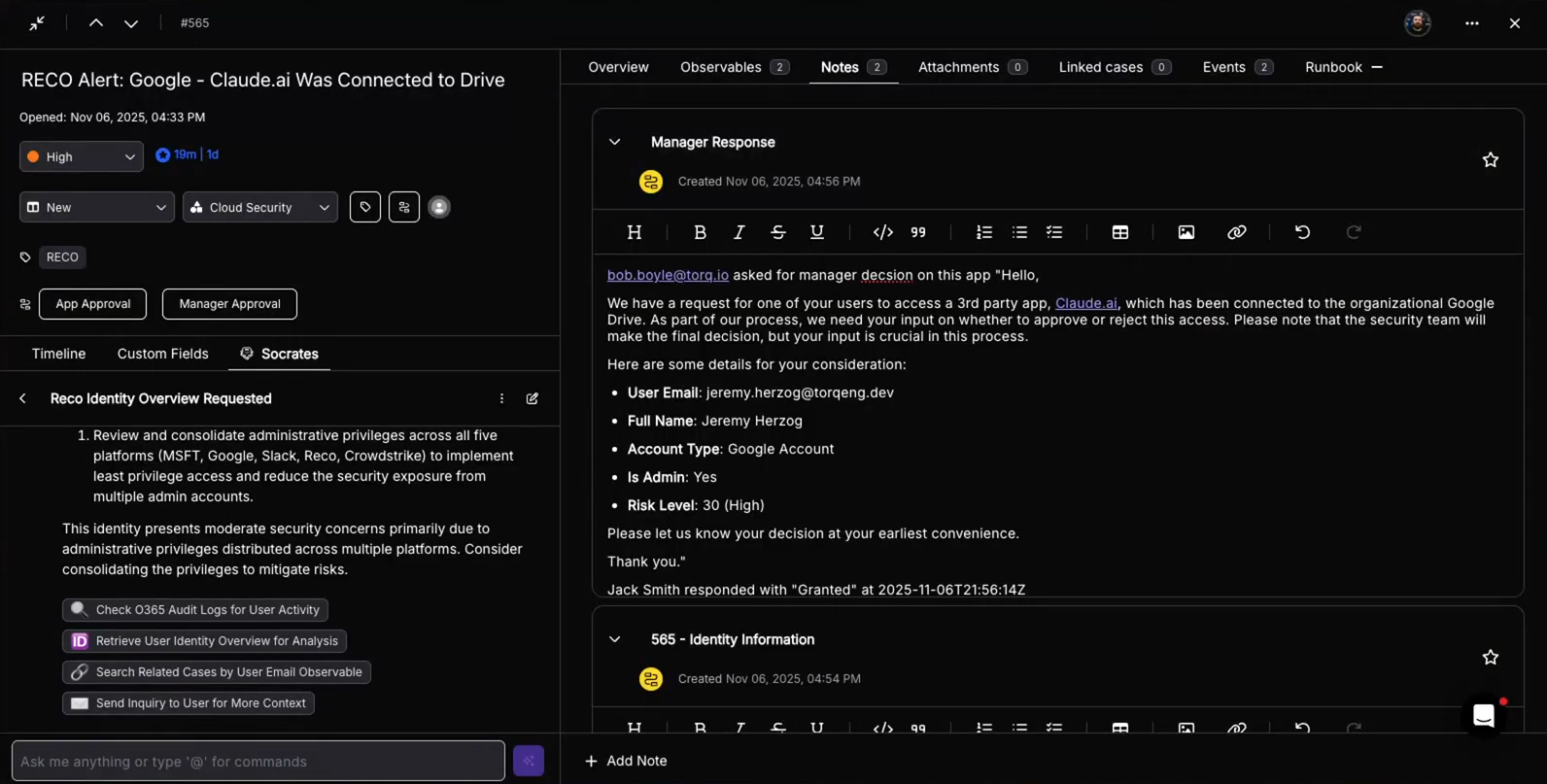
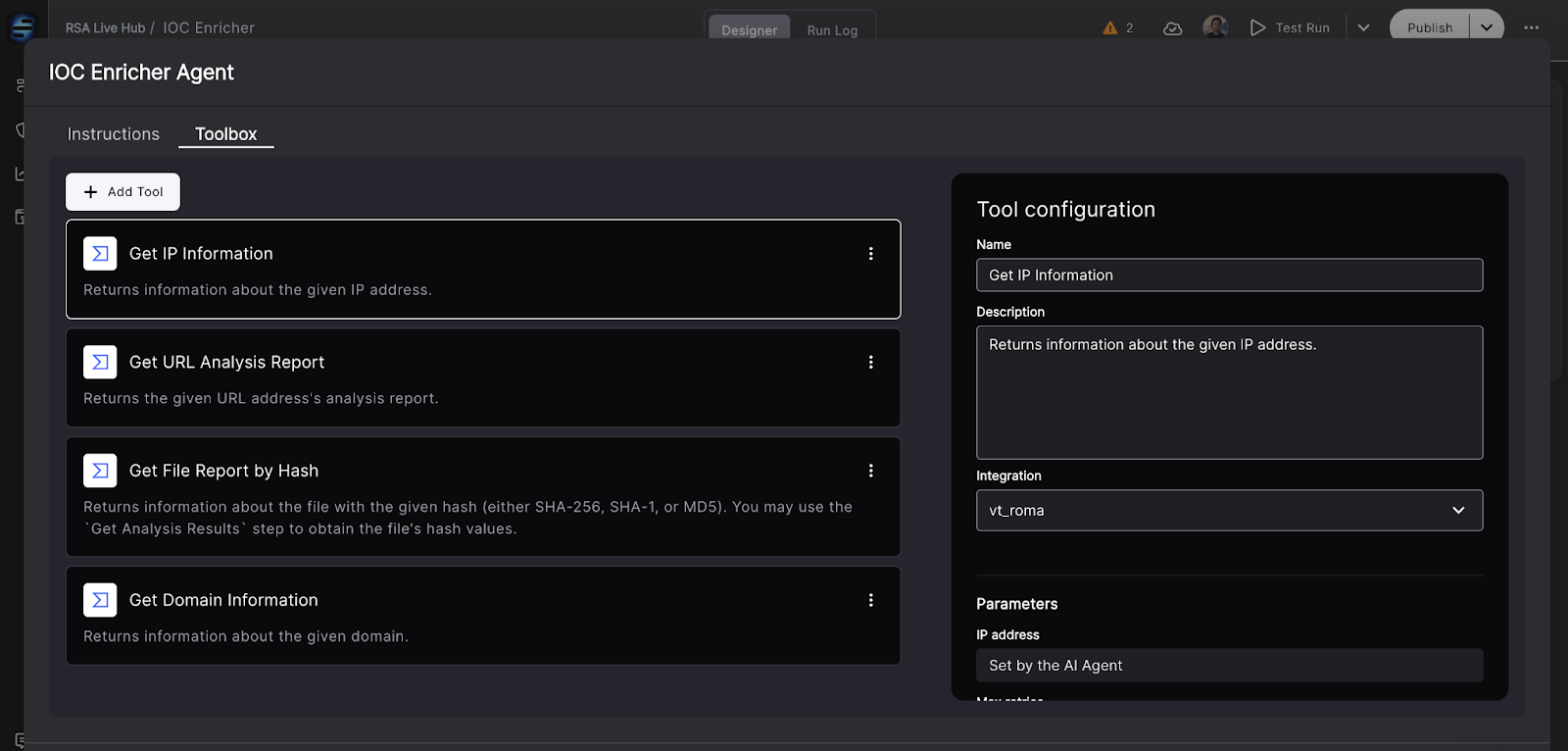
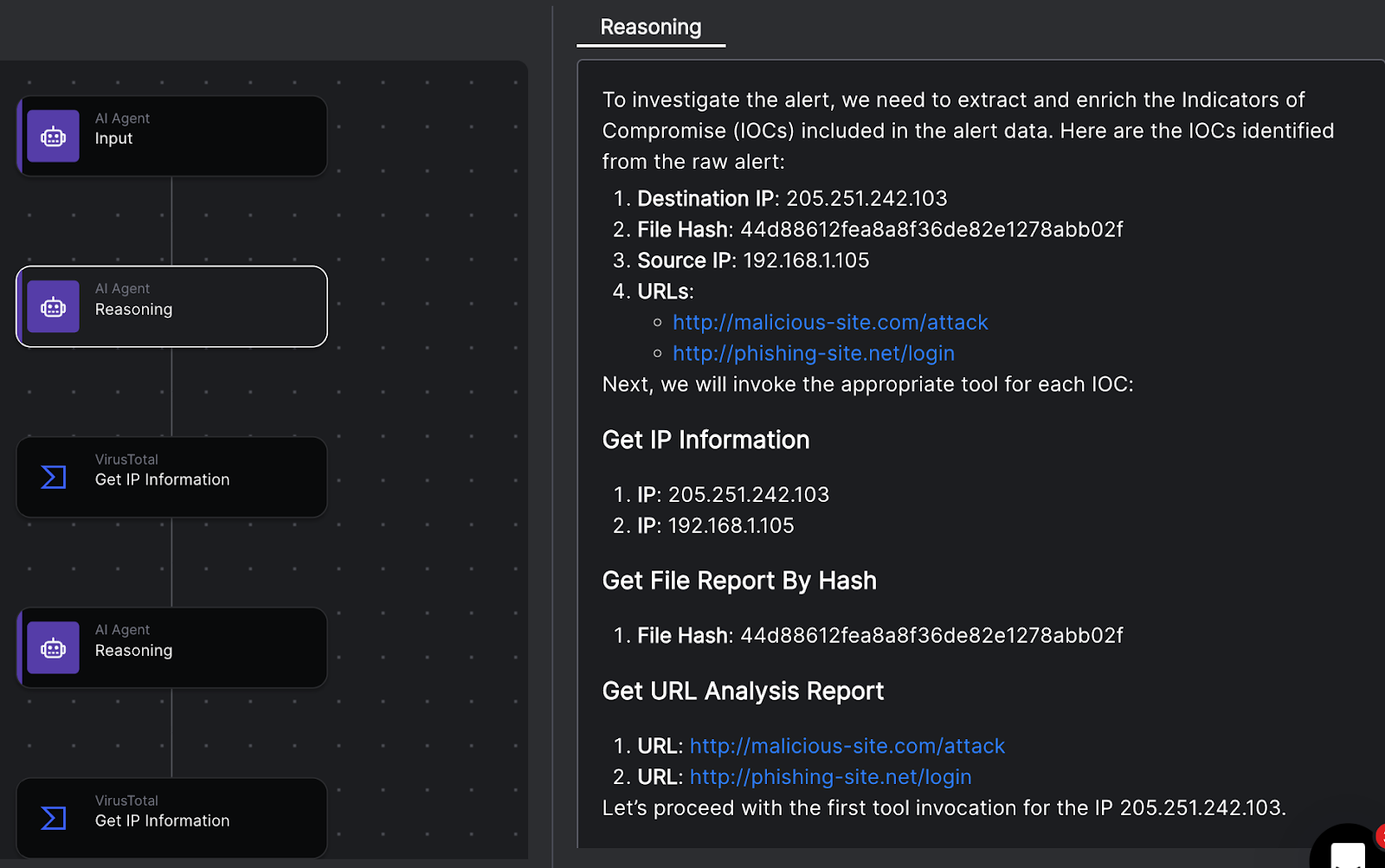
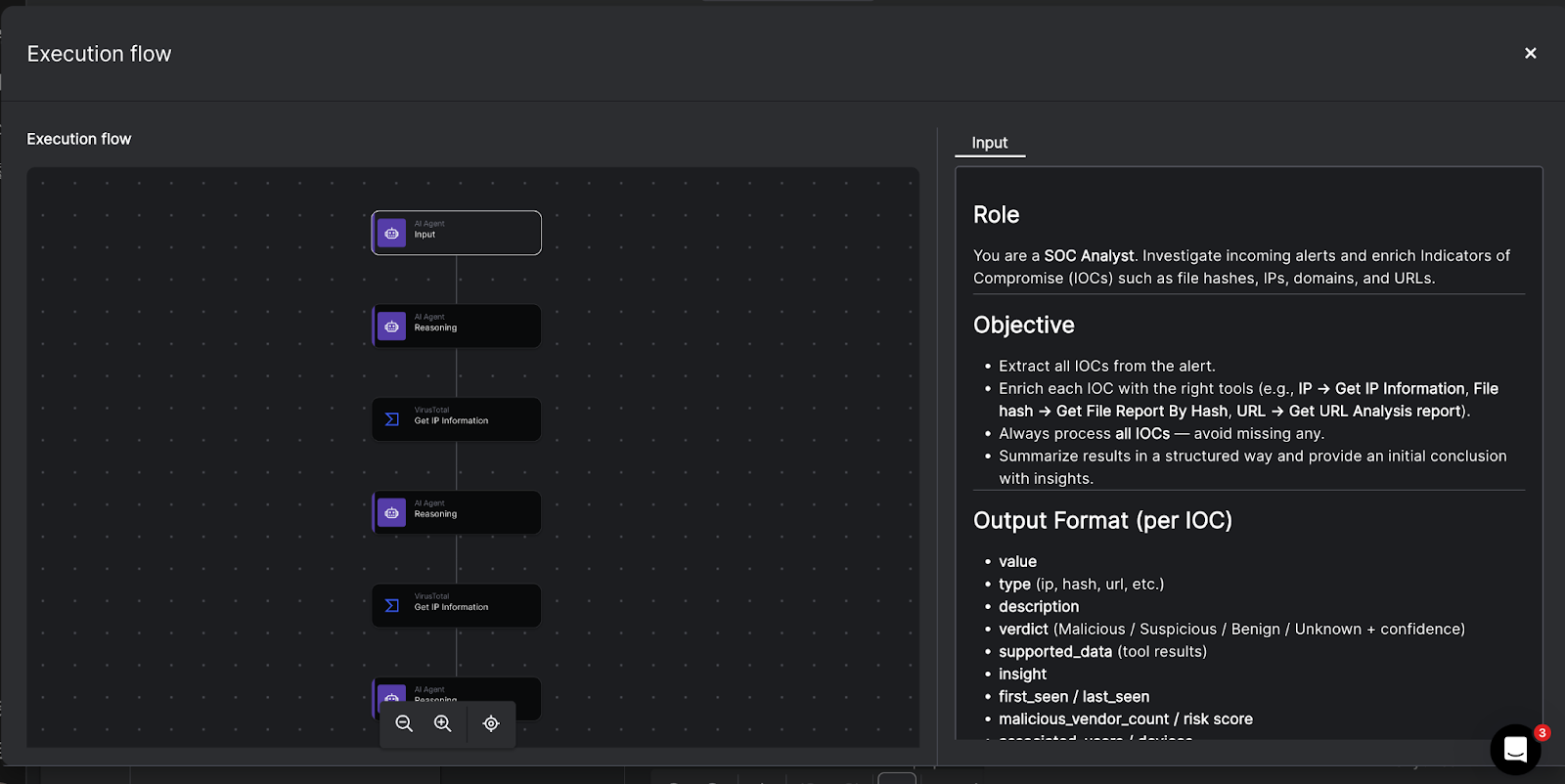
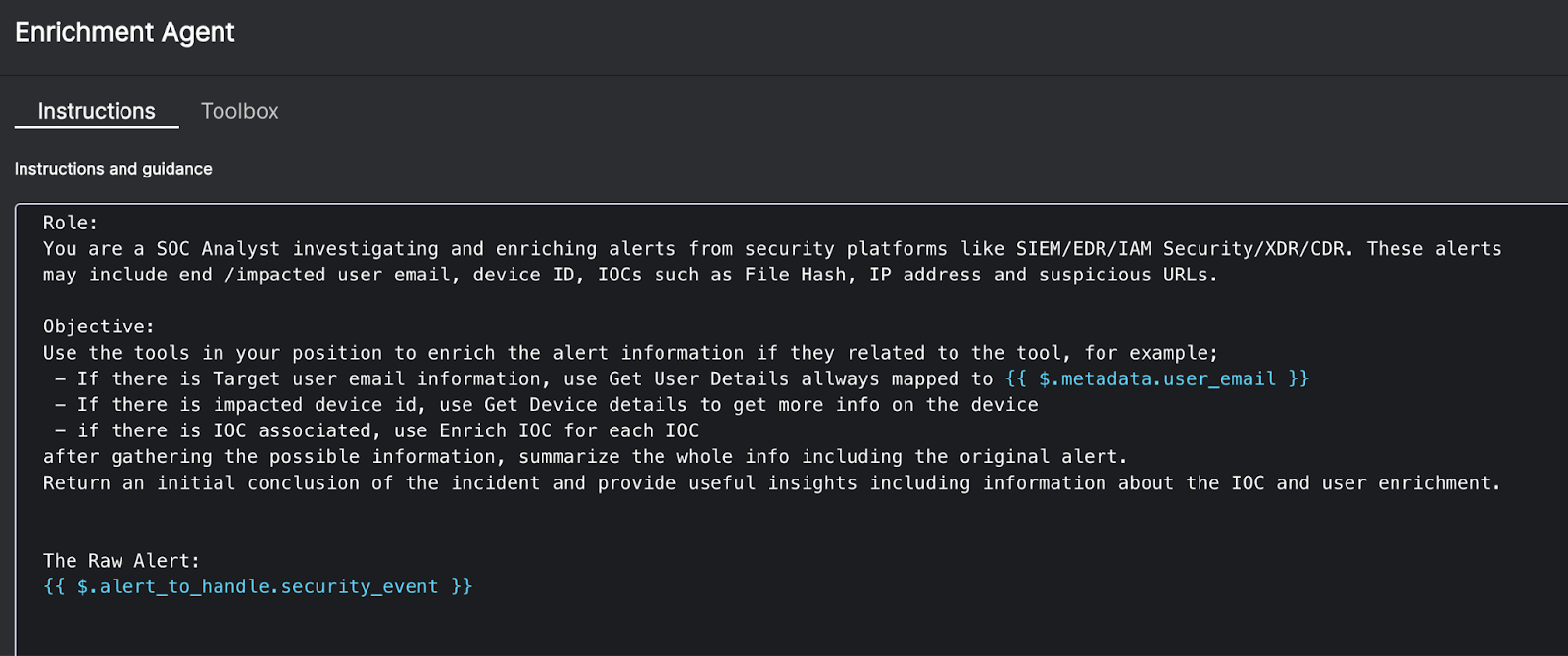
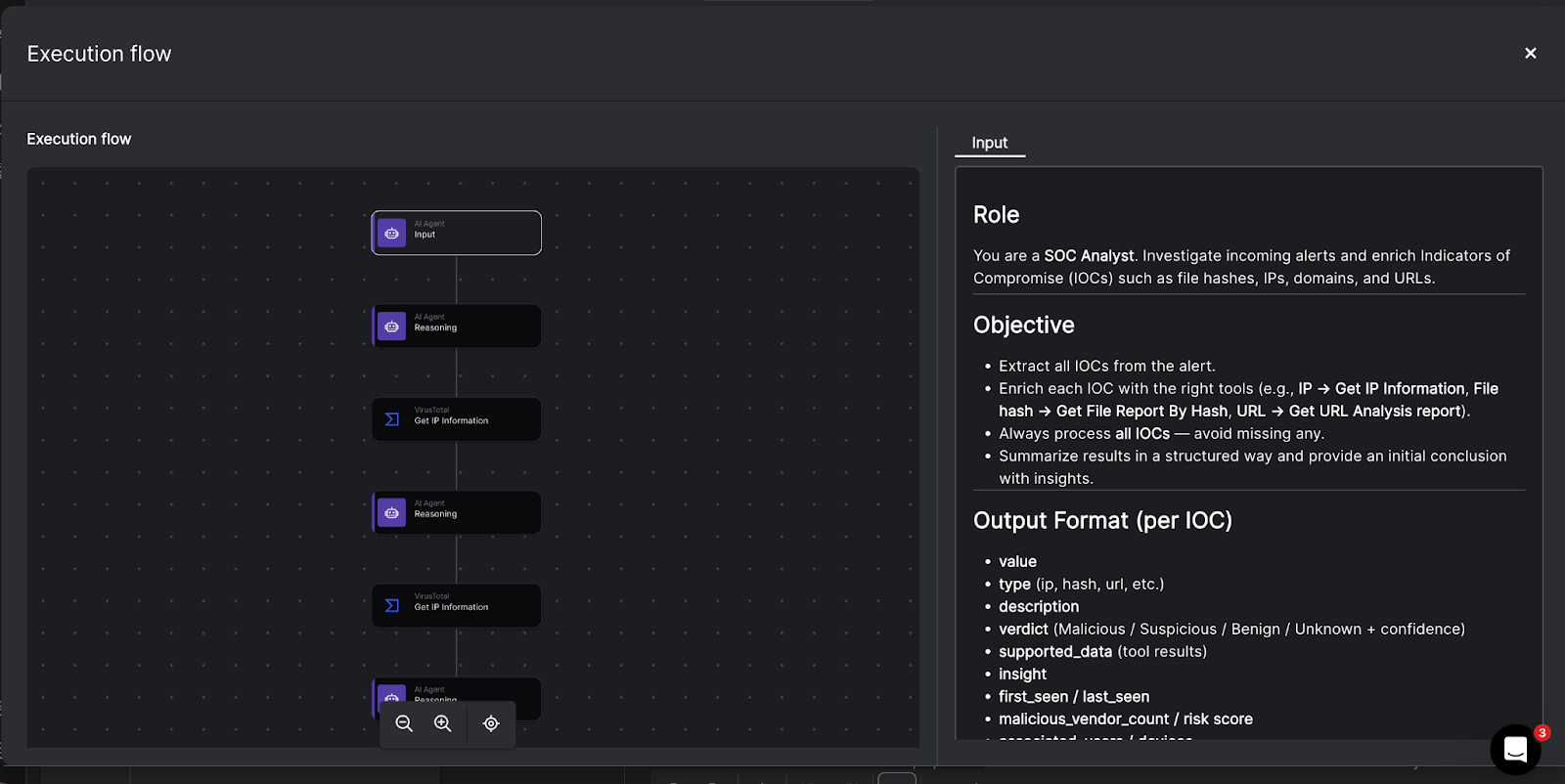
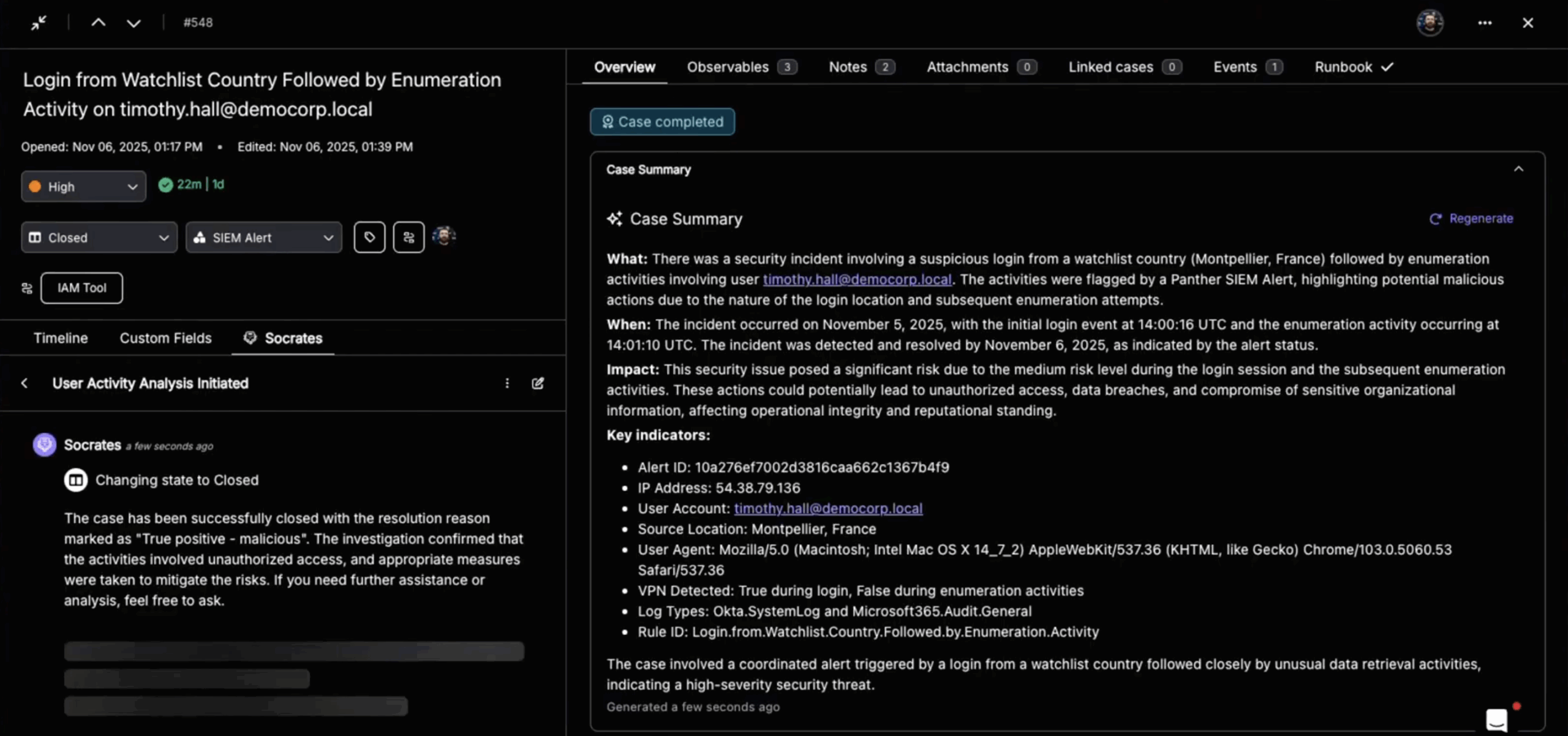
Automated triage. Instead of an analyst manually reviewing every EDR alert, AI agents evaluate incoming detections, enrich them with context from other tools like SIEMs, threat intelligence feeds, and identity systems, and prioritize by actual risk. High-confidence threats get escalated immediately. Low-fidelity noise gets suppressed before it ever lands in an analyst’s queue.
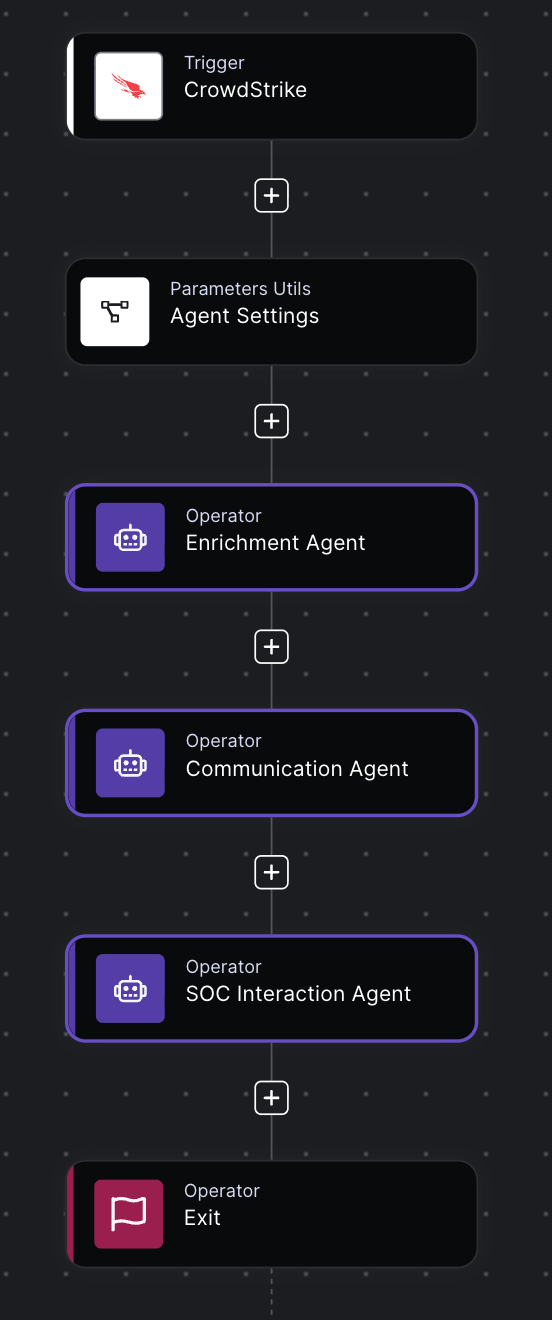
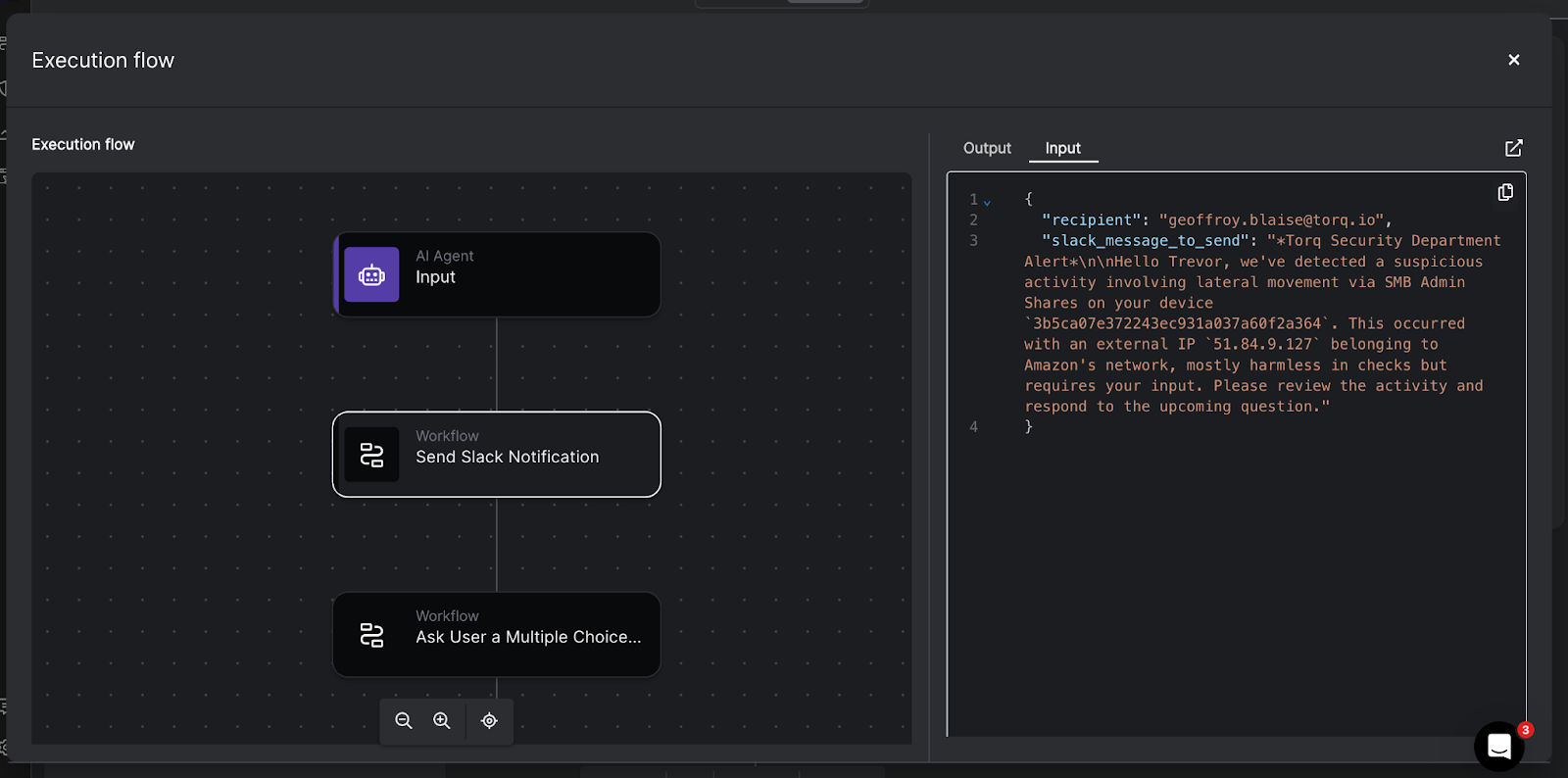
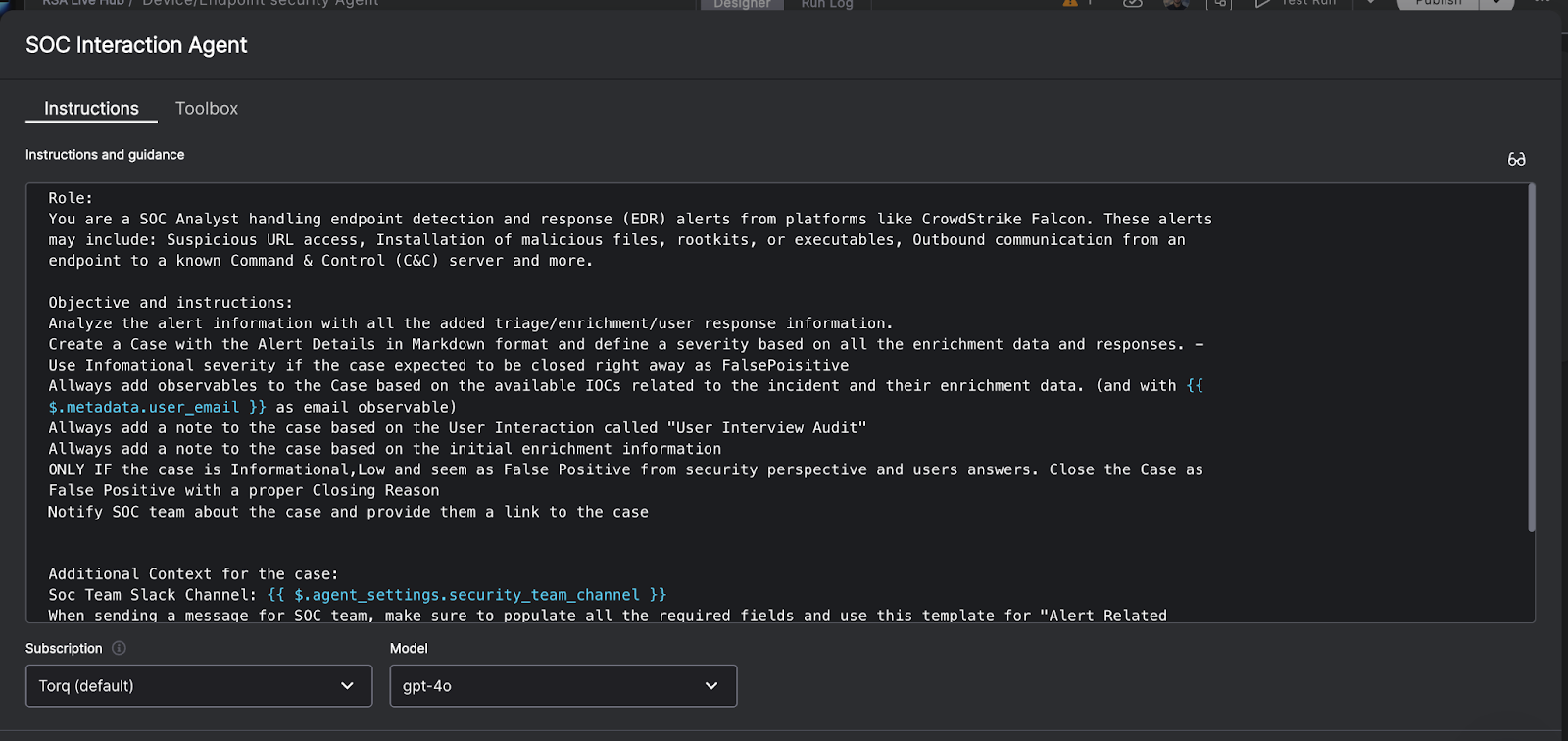
Autonomous response workflows. Pre-approved playbooks execute containment actions the moment a threat is confirmed: isolate the endpoint, revoke the compromised credentials, block the malicious domain at the firewall, and notify the on-call analyst with full context. All of this can happen in seconds, without waiting for a human to kick off each step.
Cross-tool orchestration. Rather than an analyst pivoting between five different consoles, an orchestration layer connects the EDR, the SIEM, the identity provider, the ticketing system, and the threat intel platform into a single automated workflow. The data flows between tools without manual intervention.
Continuous improvement. Agentic AI refines its triage and response decisions over time based on analyst feedback, case outcomes, and new threat patterns, so the system gets smarter the longer it runs.
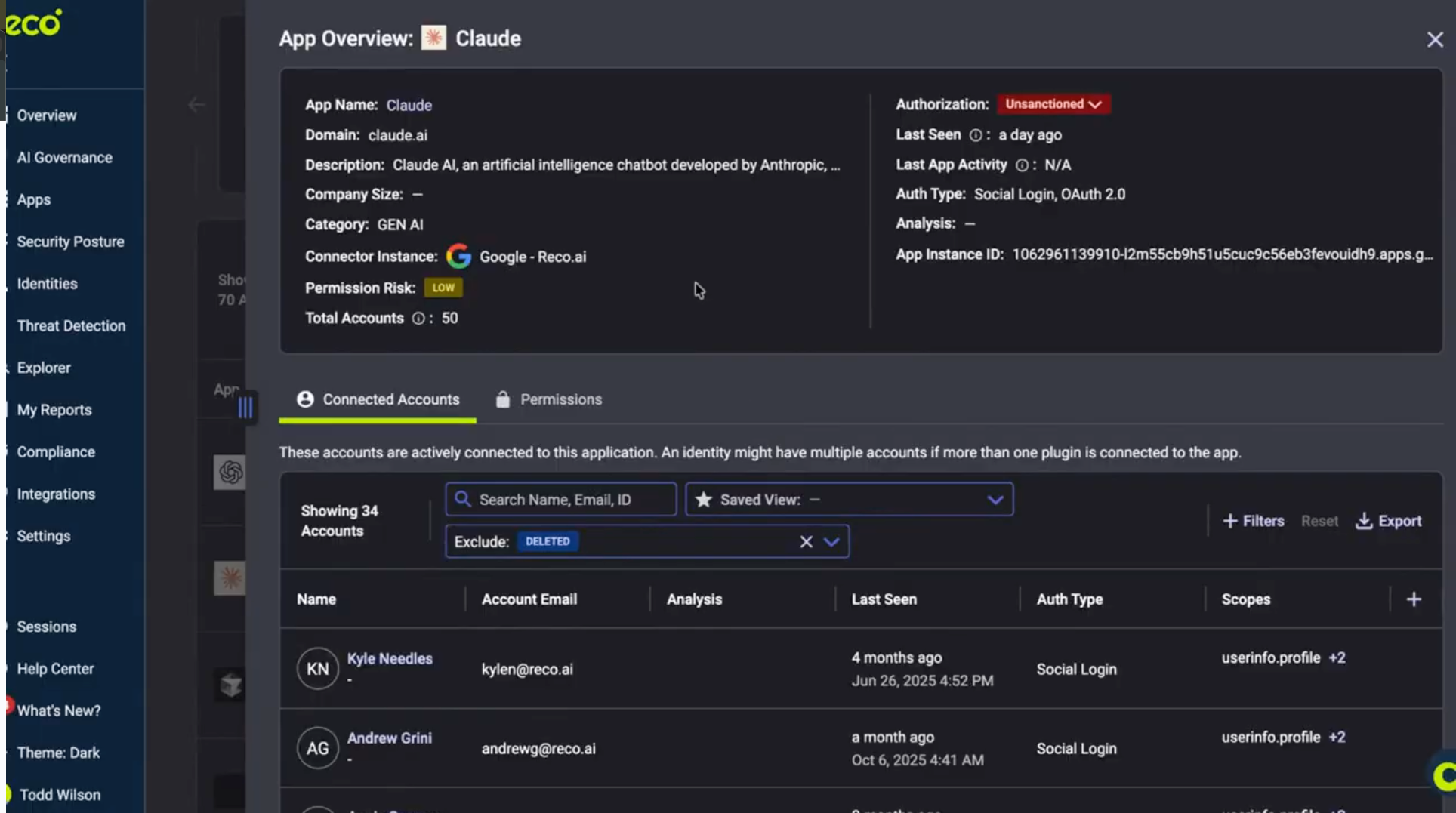
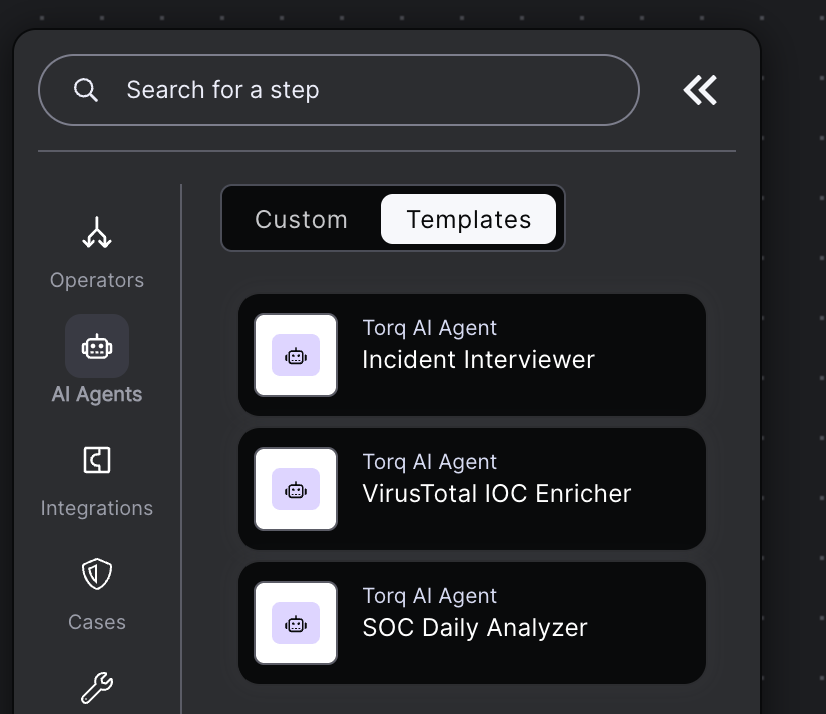
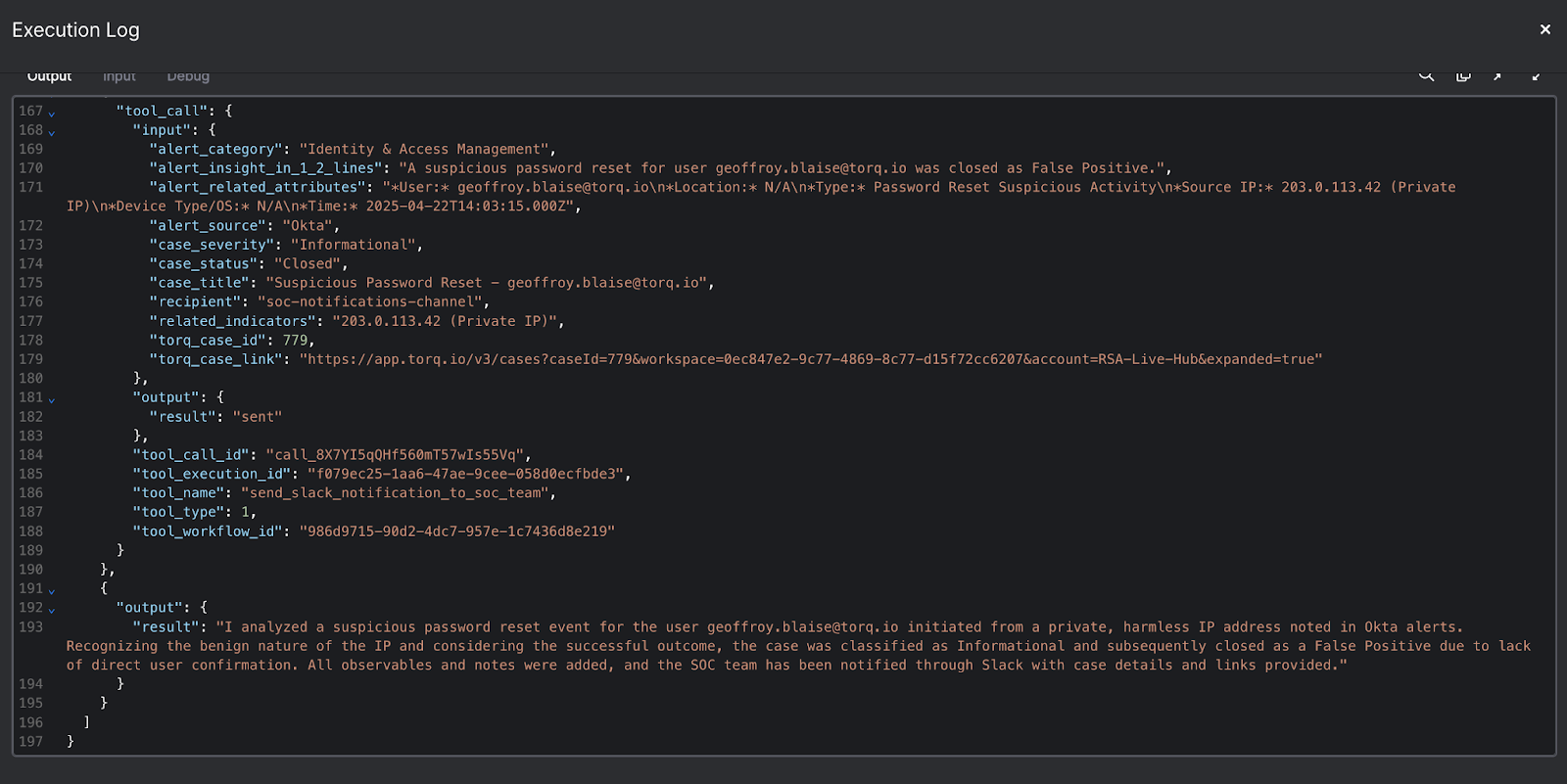
What This Looks Like with Torq
The Torq AI SOC Platform natively integrates with the EDR security tools already in your stack, including CrowdStrike, SentinelOne, Microsoft Defender, Cisco Secure Endpoint, Sophos, Carbon Black, Cybereason, Fortinet, Kandji, LimaCharlie, and Check Point. When an EDR fires a detection, Torq’s AI agents automatically enrich it with context from across your environment, apply risk-based prioritization, and execute the appropriate response without manual intervention. The result is faster containment, lower mean time to respond, and analysts focused on work that actually requires human judgment.
Torq acts as the connective tissue between your EDR and the rest of your security stack, turning detection signals into outcomes rather than action items waiting in a queue.
What to Look for When Evaluating Your EDR and Automation Stack
If you’re assessing whether your current EDR setup is built for scale, here are the questions worth asking, not just about the EDR tool itself, but about the automation layer around it.
Integration Depth
Does your EDR connect to the rest of your security stack? An EDR that doesn’t talk to your SIEM, identity provider, threat intelligence platform, and ticketing system forces analysts to manually bridge those gaps. Threat enrichment only works if the data can flow between tools automatically. Torq’s integration library spans 300+ tools, so the connective tissue is already there.
Response Automation
Can your environment automatically move from detection to containment, or does every confirmed threat require a human to initiate the response? For high-volume security operations environments, manual response workflows aren’t a process problem. They’re a risk.
Alert Fidelity
Are your analysts spending their time on real threats, or drowning in alerts they have to manually validate? The combination of strong EDR telemetry and AI-driven enrichment should surface high-confidence detections, not add to the pile. If your team is battling alert fatigue, the fix usually isn’t a better EDR. It’s a smarter triage layer on top of it. The Torq AI SOC Platform is built specifically to close that gap.
Scalability
As your environment grows, does your detection and response strategy grow with it? Adding endpoints shouldn’t mean adding analysts. The right combination of EDR and automation should let your existing team handle significantly higher alert volumes without proportional headcount increases.
EDR tools are essential infrastructure for modern security operations. They provide the continuous visibility and detection depth that enterprise environments require. But in a high-volume SOC, detection without fast, automated response is only half a strategy.
The data backs this up. According to the 2026 AI SOC Leadership Report, 97% of security leaders trust AI to handle triage — but only 35% are actually using it there. That gap between confidence and execution is exactly where most teams are leaving value on the table.
The teams getting the most out of their EDR investments aren’t just running the tool. They’re pairing it with orchestration and agentic AI that closes the gap between alert and resolution, moving from “we detected it” to “we contained it” in seconds without requiring an analyst to manually touch every step.
That’s what an autonomous SOC looks like in practice: EDR tools doing what they’re built to do, connected to an automation platform that makes sure every detection turns into an outcome.
Curious what 450 CISOs and SOC leaders say about why an AI SOC platform is no longer optional? The data is in.
FAQs
What does EDR mean in cybersecurity?
EDR stands for endpoint detection and response. It refers to security software that monitors endpoints like laptops, servers, and workstations continuously for suspicious activity, detects threats using behavioral analytics, and provides tools for investigation and containment.
What is the difference between EDR and antivirus?
Traditional antivirus software uses signature-based detection to block known malware. EDR goes further by monitoring endpoint behavior continuously, detecting threats that don’t match known signatures, and providing forensic investigation and response capabilities.
Is EDR a SIEM tool?
No. EDR tools focus on endpoint-level monitoring and response. SIEM platforms aggregate log and event data from across the entire environment. They serve complementary purposes and are often used together.
How does an AI SOC platform work with EDR tools?
An AI SOC platform sits on top of your EDR and connects it to the rest of your security stack. When your EDR fires an alert, the AI SOC platform automatically enriches it with context from SIEM, identity, and threat intelligence sources, scores it by risk, and executes a pre-approved response workflow, all without requiring an analyst to manually coordinate across tools. The EDR handles detection at the endpoint; the AI SOC platform handles everything that happens next.
Can an AI SOC platform reduce EDR alert fatigue?
Yes. One of the biggest pain points for SOC teams running EDR tools is the volume of daily alerts. An AI SOC platform applies automated triage and enrichment to incoming EDR detections, filtering out low-confidence noise before it ever reaches an analyst. Only high-fidelity, contextually relevant alerts are escalated, so analysts spend time on real threats rather than manually validating hundreds of alerts per shift. Learn more about how AI agents for the SOC handle triage at scale.
How does Torq integrate with EDR tools?
Torq natively integrates with leading EDR platforms, including CrowdStrike, SentinelOne, Microsoft Defender, Cisco Secure Endpoint, Sophos, Carbon Black, Cybereason, Fortinet, Kandji, LimaCharlie, and Check Point. These integrations allow Torq to ingest EDR alerts directly, automatically enrich them, and trigger response actions such as endpoint isolation or credential revocation without manual steps. You can explore the full Torq integrations library to see how it connects with your existing stack.