Contents
Get a Personalized Demo
See how Torq harnesses AI in your SOC to detect, prioritize, and respond to threats faster.
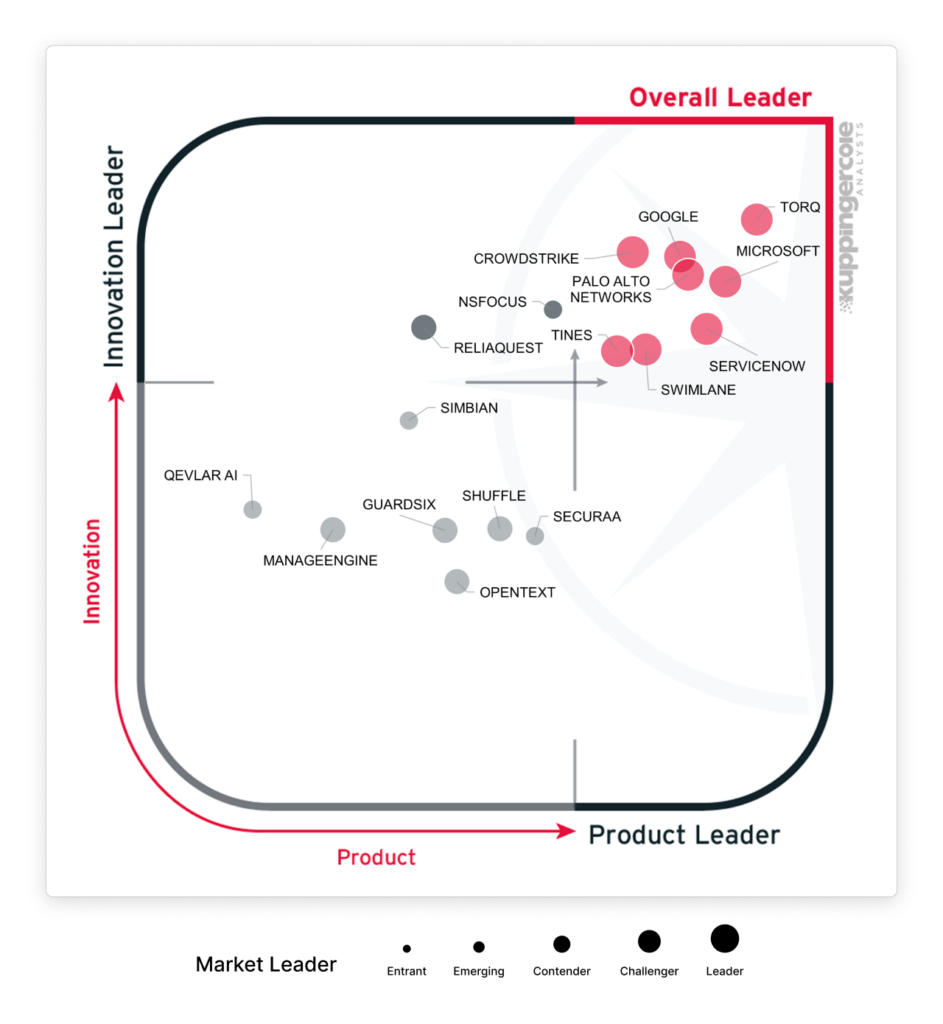
The security automation market just got its definitive evaluation and its new name.
KuppingerCole Analysts is the global analyst firm that sets the benchmark for cybersecurity technology evaluations. Their Leadership Compass is the gold-standard independent assessment enterprises rely on when making platform decisions, rigorously scoring vendors across product maturity, innovation, and market execution. When KuppingerCole Analysts names a category, the industry follows. When they name a Leader, buying teams listen.
KuppingerCole Analysts’ April 2026 Leadership Compass retired the SOAR category entirely. The report is now called The Emerging AI SOC to reflect the market transformation. In the words of KuppingerCole analyst Matthew Gardiner, “Traditional rule-based workflow and playbook-based SOAR systems have hit an efficiency and implementation brick wall. The cost and expertise required to get significant ROI from traditional SOAR systems is out of reach for average security organizations… AI is showing early signs of changing this calculus and lowering the bar for smart(er) automation.”
We couldn’t agree more. The new frontier is agentic AI, adaptive reasoning, and platforms that augment analysts, not replace them. Transparency and control have been at the heart of our AI SOC strategy for years.
Torq was named a Leader by KuppingerCole Analysts in all four categories for the AI SOC: Overall, Product, Innovation, and Market.
Torq scored highest in both Innovation Leadership and Product Leadership. We are named a Market Leader driven by rapid customer growth, expanding revenues, and increasingly comprehensive capabilities. And was evaluated as an Overall Leader across every dimension that KuppingerCole Analysts measures.
Here’s what the KuppingerCole Analysts Leadership Compass for the Emerging AI SOC found and what it means for the market.
The AI SOC Category Is Official. SOAR Is Not Coming Back.
KuppingerCole Analysts rebranded the report category because the underlying technology for security automation has fundamentally shifted. Newer automation capabilities “increasingly focus on AI-based reasoning, natural language chat interfaces, contextual enrichment, and adaptive decision support” rather than simply executing preconfigured rules and playbooks. Rule-based systems only work when the problem space is stable, and security operations are anything but.
The competition has shifted with the market. Differentiation is no longer about who has the most predefined playbooks or the longest feature list. It’s about usability, flexibility, scalability, and the ability to support heterogeneous, tool-rich environments without excessive engineering or people-intensive overhead. Playbooks and out-of-the-box integrations still matter, but they’re table stakes. The real differentiator is how effectively a platform reduces the human burden while handling the messy, multi-vendor reality of a modern SOC.
This is the shift Torq was built for — and the criteria KuppingerCole Analysts used to separate Leaders from the rest of the field.
The report also names the operational problem driving that shift: agentic AI has the potential to rebalance the false-positive-to-false-negative tradeoff that has defined SOC work for years. With manual triage, alert fatigue is so severe that missed threats become an accepted cost. AI agents don’t experience fatigue. They triage 100% of alerts continuously, shifting sensitivity to catch threats rather than just manage volume.
The buyer data backs this up. Torq’s 2026 survey of 450 security leaders found that 97% are confident AI can handle triage, the highest-volume function in the SOC. But only 35% have deployed it there. The confidence exists. The platforms to act on it haven’t — until now.
Where Torq Outscored in the KuppingerCole Analysts AI SOC Evaluation
KuppingerCole Analysts evaluates vendors across product leadership, innovation, and market execution. Here’s where Torq stands.
Product Leader. Torq scored highest in product leadership. The Product Leaders in this analysis stand out for the breadth, depth, and maturity of their current product capabilities, delivering robust, production-grade platforms that address the full lifecycle of modern SOC operations. This includes detection integration, triage, investigation, automation, case management, governance, and reporting. Torq earned this position with strong architectural foundations, rich functionality, and proven suitability for complex operational environments.
Innovation Leader. As Gardiner states, “Innovation Leaders push the boundaries of how SecOps are designed, automated, and augmented with AI.” Torq scored highest in innovation, with a standalone callout for behavioral detection coverage across users, devices, AI agents, and other non-human identities, as well as threat actor attribution, cloud infrastructure automated response coverage, and extensive AI decision explainability.
Market Leader. Market Leadership weighs the number of customers, their geographic distribution, deployment size, support services, partnership ecosystem, and financial health. As KuppingerCole Analysts makes clear, “Market Leadership requires global reach.” Named a Market Leader, Torq has quickly emerged as a security automation market leader, driven by rapid customer and revenue growth, unique branding, and increasingly comprehensive product capabilities — reshaping expectations for modern security automation by emphasizing simplicity, extensibility, and rapid deployment through low-code automation, lowering the barrier to adoption while supporting complex enterprise use cases.
Overall Leader. Named an Overall Leader, the Torq AI SOC Platform exemplifies a new generation of security automation — excelling at low-code orchestration, rapid automation across security tools, and AI-assisted and agentic workflows. Positioned as a security automation engine within the SOC that is independent of the large security platforms. And in a relatively short time, acquired a significant number of enterprise customers.
Torq’s AI SOC Strengths Documented in the KuppingerCole Analysts Leadership Compass
The report identified eleven specific strengths for Torq. Here are the ones that matter most for buying teams.
Proven Agentic AI
Torq has measurable, documented success with agentic AI among early-adopter customers, including Fortune 500 production security operations.
Our 2026 Torq AI SOC Leadership Report found that 72% of CISOs and security leaders are comfortable with fully autonomous AI for medium-severity incidents and below, but most haven’t deployed it because the platform controls aren’t in place. Not a problem with Torq. Documented customer success with Torq Agentic AI shows that Torq controls work in practice, not just in a demo environment.
“Torq Agentic AI now handles 100% of Carvana’s Tier-1 security alerts and has automated 41 different runbooks within just one month of deployment.”
– Carvana
Deep Integration Layer
KuppingerCole Analysts noted Torq’s extensive support for third-party SIEM, EDR/XDR, ITSM, web gateways, firewalls, threat intelligence sources, IAM/PAM, UEBA, and file sandbox systems as the first in its list of strengths.
300+ pre-built integrations covering a broad spectrum of SOC use cases. Extensive support for public cloud response actions, including enabling/disabling users and starting/stopping instances. Deep integrations with ITSM platforms like ServiceNow, Jira Service Management, BMC Helix, Freshservice, and Ivanti. Broad support for incident communication systems, including email, Slack/Teams, PagerDuty, and SMS. Customization support for both enterprise customers and MDR providers.
This directly addresses the fragmentation problem we see in SOCs: 85% of CISOs want a unified AI SOC platform. You can’t unify what you can’t integrate.
AI-Native Architecture
The Torq platform supports Retrieval Augmented Generation (RAG) for pulling in external data sources, Model-Context Protocol (MCP) for standardized tool connectivity, and agent-to-agent collaboration, enabling specialized AI agents to coordinate across investigation steps without human handoffs. Analysts can describe what they want in plain language — “enrich this alert with threat intel, check if the user has had prior incidents, and isolate the endpoint if confidence is high” — and the platform automatically generates and validates a production-ready workflow.
This is the architectural difference the KuppingerCole Analysts AI SOC evaluation is measuring: whether AI is the foundation of the platform or a feature layer added on top of legacy automation. Torq was built for the former.
Our research found that 92% of security leaders want AI that learns and adapts to attack patterns, which requires an architecture designed for continuous learning from the ground up.
Enterprise-Grade Trust and Governance
Torq provides broad support for role-based, attribute-based, and policy-based access controls, along with strong authentication for administrative users — giving security teams granular control over who can do what within the platform. Global datacenter support enables regional data sovereignty, which is critical for EU customers operating under strict compliance requirements.
And for MSSPs and large enterprises, the platform supports full look-and-feel customization, white-labeling, and tenant isolation — so providers can deliver Torq-powered services under their own brand without exposing the underlying platform to end customers.
In our recent report, 92% of security leaders cited at least one factor that reduces their trust in AI; governance isn’t optional. The number one thing that would build confidence is full transparency into AI decision-making. Torq scored highest in the Leadership Compass for AI decision explainability — the exact capability buyers say they need before they’ll expand AI autonomy.
Financial Stability and Market Momentum
Torq’s recent unicorn-level $1.2 billion valuation is a strength noted by KuppingerCole Analysts because it matters when you’re betting your SOC infrastructure on a vendor’s longevity. Torq has quickly emerged as a market leader, driven by rapid customer growth and expanding revenues, and has acquired a significant number of enterprise customers in a relatively short time.
For buying teams evaluating standalone AI SOC platforms against platform vendors, commercial viability is a real consideration. KuppingerCole Analysts’ inclusion of this as a documented strength signals that Torq has crossed the threshold from promising startup to established market participant.
What This Means for Security Teams
The AI SOC is no longer a concept; it’s a defined market category with a formal evaluation framework, scored vendors, and documented production outcomes. The KuppingerCole Analysts Leadership Compass for AI SOC makes that official. And the data from 450 security leaders in the 2026 Torq AI SOC Leadership Report confirms the urgency: security teams aren’t debating whether AI belongs in the SOC. That adoption argument is over, with 94% already using AI. The conversation is now about accountability and results. Enterprises are seeking an AI SOC platform that actually delivers.
For buying teams, the decision comes down to architecture. Do you extend a legacy system with bolted-on AI capabilities and questionable ongoing investment? Or do you invest in a cloud-native, AI-augmented platform designed for the multi-vendor, multi-signal reality of your security stack?
KuppingerCole Analysts evaluated that exact question across product strength, innovation, and market execution. One platform scored highest in innovation and product leadership, and earned Leader status in every measured category — with production-grade results to back the scores.